*Source of claim SH can remove it.
Conteban
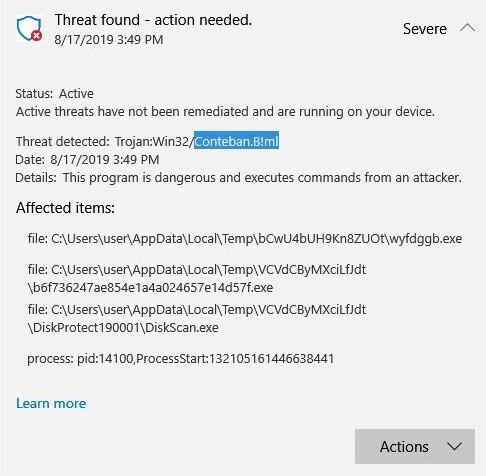
Conteban is a Trojan Horse infection that can destroy information of any kind, including work-related documents, databases, personal files, and system data. To do that, Conteban can secretly sneak inside the system and wipe off the entire disk.
The Trojans are sneaky and extremely malicious threats. You probably would be pretty worried of you find out that a representative of this category has corrupted your machine. Since you are here, however, you most likely have detected an infection of this type called Conteban. Reports about this particular Trojan-based virus have recently been received by our “How to remove” team, and people have been asking for a working solution to remove the infection. So, in the next lines, we will provide a removal guide for those of you who may need it. The guide contains detailed instructions on how to manually find and remove Conteban and all its related files, as well as a professional removal tool for an in-depth system scan.
Trojan script/conteban.a ml
One of the possible actions for which Trojan script/conteban.a ml can be used is theft. And this can involve stealing specific documents and files from your computer, or any work-related or personal data you placed there, as well as correspondence with other people, contacts, emails, etc. An infection like Trojan script/conteban.a ml can help the hackers get financial details from you with the intention to steal your money.
The Conteban Trojan
Threats like the Conteban Trojan can be very, very stealthy. In addition, because of their ability to perform a wider range of malicious actions compared to any other type of malware, they are also very unpredictable. That’s precisely why we can’t tell you exactly how the Conteban Trojan can harm your machine.
How harmful can Conteban be?
The Trojans are some of the most dangerous online threats out there. But this doesn’t automatically mean that, if you’ve been infected, that’s the end of your computer. Sometimes, if detected and removed on time, the Trojan could be prevented from messing everything up. So, the fact that you have been able to detect Conteban, and have landed on this page is already a step towards its removal.
Conteban can also be used in a number of different ways to spy on you. It can be set to record your keystrokes, hack into your microphone and camera, and share with the hackers your conversations. Other possible malicious uses may include the delivery of other malware, such as ransomware, into the computer. On top of that, the Trojan may be configured to delete certain files, or even format your disks, wiping them off from any data stored there.
Regardless of the mission of this particular infection, on this page, you have all the needed resources to remove it. Of course, additional steps should also be taken to ensure that your computer stays safe from such malware in the future. We suggest you start by installing a reliable antivirus program. Also, make sure to keep an eye out for new system and software updates that are available, and download them. This will ensure that there are no system vulnerabilities which can be exploited by a Trojan or by another virus. And last but not least, when browsing the web, be especially careful. Stick to trusted websites and avoid anything that looks sketchy or suspicious.
SUMMARY:
| Name | Conteban |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Remove Conteban Trojan
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Comment