Conti
Conti is a dangerous PC virus capable of entering your system without any infection signs and then locking up any important files stored there. Conti is created for the purpose of blackmailing its victims by keeping their data blocked until they pay a ransom.
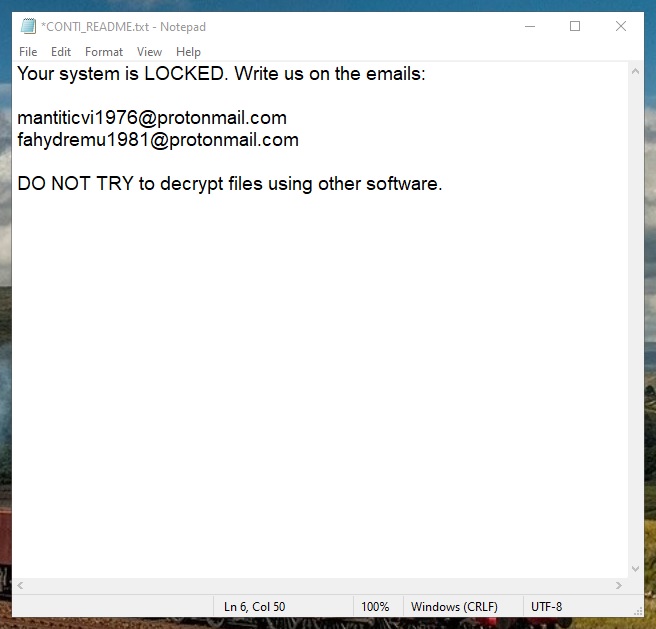
The Conti Virus ransom note
This type of computer threat is particularly problematic because there isn’t a surefire method of dealing with it. Oftentimes, the users who get attacked by infections like Conti, Try2Cry, Prnds never manage to restore the access to their personal files and if any of the lost files have been important to the attacked user, the attack from such a virus can be especially damaging.
Here, we will tell you about the characteristics of the Conti virus, the way it functions, and the actions you can take in order to minimize the damage it may cause.
The Conti virus
The Conti virus is a date-encrypting piece of malware that can secretly lock up the files located on your hard drives. Experts categorize the Conti virus as a Ransomware cryptovirus and warn that it is distributed via spam messages or with the help of disguised Trojans.
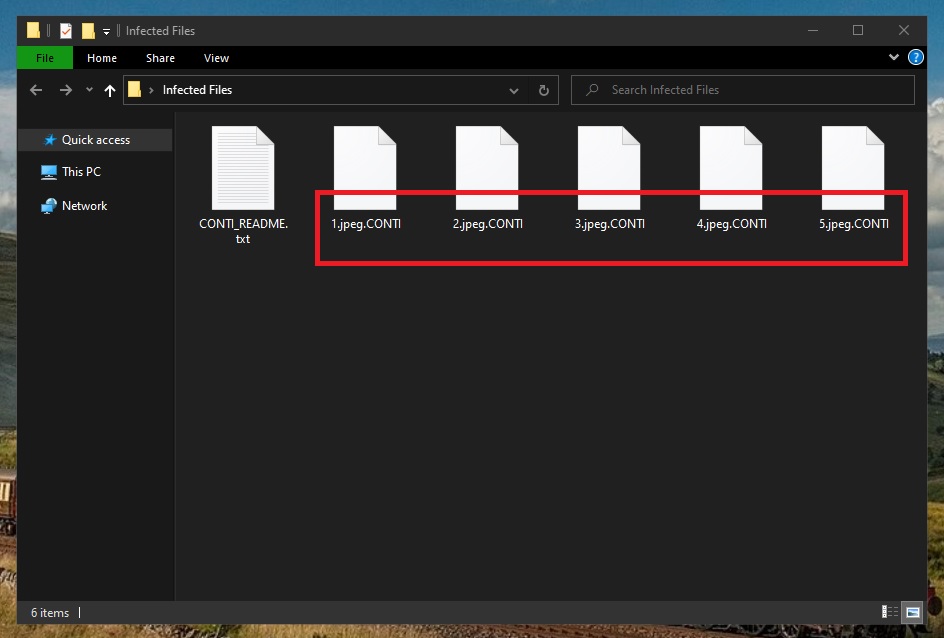
The Conti Virus encrypted files
As soon as this threat enters a targeted system, it launches an advanced process of file encryption. This process silently locks up each and every file it is applied to. Once the encryption process is complete, most (if not all) of the user’s personal files would no longer be available. No regular program can open an encrypted file unless there is a special decryption key located on the computer that can be used to unlock the sealed data. During the encryption process, the Ransomware virus generates such a key and stores it on the hackers’ server. There is a unique decryption key for every computer infected by the Ransomware so using the key generated for another PC won’t unlock your encrypted files – you need the key that’s been generated for your computer specifically.
Of course, the hackers offer to send you the decryption key that matches the encryption on your files but only if you send them a certain amount of money following their strict instructions. Generally, we’d advise against going for this option because the chances of getting tricked and lied to by the hackers and never receiving the access key that you need are too high.
The Conti file decryption
The Conti file decryption is what can allow you to restore your files using the corresponding access key. If the key for the Conti file decryption isn’t available to you, there may be some other things you can try to restore your data.
In the guide present on this page, you will first find removal instructions that will help you safely remove Conti. After you complete this first part of the guide, you can then try the suggested file-recovery alternatives that are free and won’t require you to interact with the hackers. However, we must still warn you that there aren’t any guarantees those alternatives will work – you will have to try them and see for yourself if they would be effective in your case.
SUMMARY:
| Name | Conti |
| Type | Ransomware |
| Detection Tool |
Remove Conti Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment