Prnds
Prnds belongs to the category of malicious code known as ransomware. Prnds is among the file-encrypting subtype variants, which means that it encrypts the files on its victims’ computers.
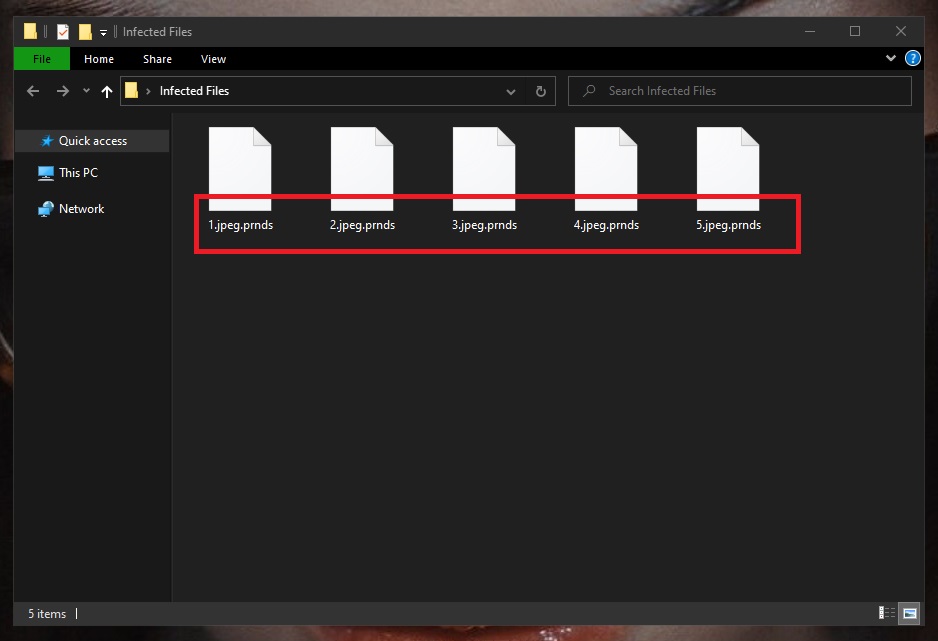
The Prnds Ransomware encrypted files
Ransomware of this kind can target a very wide range of different file formats. So pretty much all popular files types will go: pictures, videos, audio files, databases, text documents – you name it. However, the process of encrypting these files is a tedious one and may often take hours to complete. This is due to the fact that first the virus in question needs to scan the system for the files it’s after, and then it needs to start creating encrypted copies of what it finds – on by one, separately. And as it goes, variants like Prnds, Zida, Masodas will also delete the original files, so that at the end of the day the victims are left with a bunch of unrecognizable and essentially useless bits of data.
After this entire process is complete, Prnds will usually generate a ransom note someplace where the victim will see it (e.g. on the desktop of the computer). And in that ransom note the hackers behind the virus will typically state their demands, such as ransom amount, transfer details, deadlines, etc. It’s very common for them to include some form of scare tactic as well, but it’s important to not fall for it or let that define your actions thereafter.
The main point of the note is that you are required to send a certain amount of money in exchange for which you will receive a decryption key. And that key, in turn, is what is set to undo the encryption and make your files usable again. What these cybercriminals won’t tell you, however, is that there are also other options available to you. And we’ll tell you about them in the second part of the removal guide below.
The Prnds virus
The Prnds virus typically acts in complete stealth and doesn’t trigger a response from most antivirus systems. This is due to the fact that the encryption process the Prnds virus uses does not actually do anything to harm the affected data.
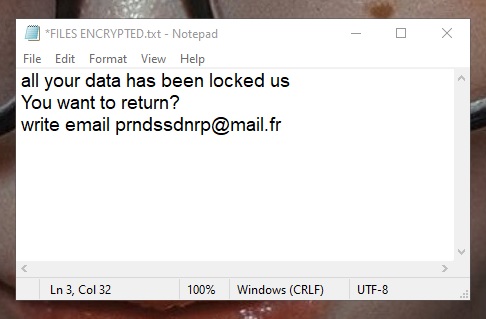
The Prnds virus ransom note
Hence, your antivirus program will most likely not prevent the encryption process from happening, nor will it even notify you about it. This is a major advantage that ransomware has and is also one of the main factors that has skyrocketed its numbers in recent years. Furthermore, the use of cryptocurrencies has also propelled the success of this virtual blackmail scheme in that the hackers can hide behind the shield of anonymity that they provide. This is another reason why we encourage ransomware victims to seek alternative methods of handling such infections. Paying the ransom is essentially funding the criminals who are extorting money from you, and the only way to put a stop to that is deny them what they want.
The Prnds file extension
The Prnds file extension is the suffix that’s attached to the end of every encrypted file name. It is because of the Prnds file extension that no software can recognize the encoded data.
SUMMARY:
| Name | Prnds |
| Type | Ransomware |
| Detection Tool |
Remove Prnds Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment