.Copa
.Copa is a ransomware cryptovirus that hackers use to encrypt user files. Once it applies its encryption, .Copa keeps the targeted files locked and demands a ransom payment from the victims.
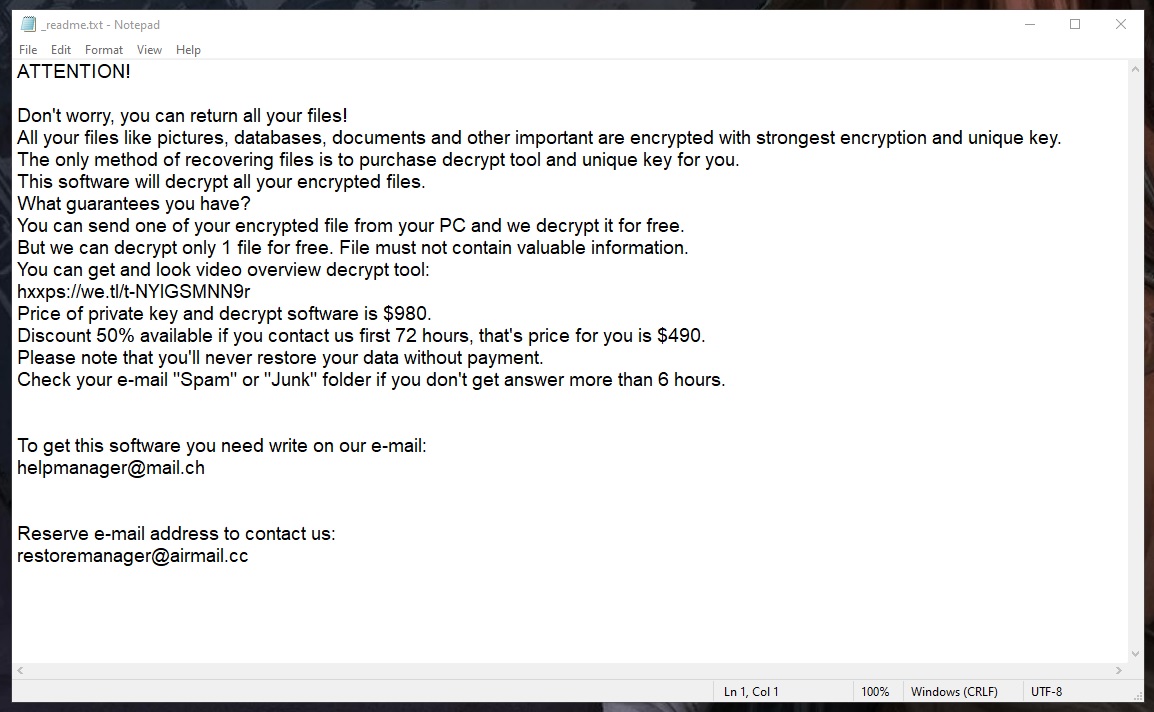
The .Copa virus ransom note
One of the key factors behind the incredibly high effectiveness of such malware attacks is the file encryption used by the ransomware cryptoviruses. Modern cryptoviruses like .Copa, for instance, are programmed to lock their victims’ files with sophisticated encryption codes that are extremely hard to break.
If .Copa has already restricted your from accessing the files inside your computer, we will help you remove this insidious virus from your computer and gather some ideas on where to seek file-recovery solutions. Of course, every user should determine for themselves what the best course of action in their situation is but, in this post, we will give you some alternative suggestions. We must alert you, though, that irrespective of what you may try to do with your locked files, there is a chance that you won’t be able to get all of them back. This is the main trouble with threats like .Copa – there is no guarantee about the recovery of the encrypted files no matter what you do.
The .Copa virus
The .Copa virus is a money-extorting virus that secretly initiates a process of file encryption in the background of the system. The .Copa virus locks the most valuable data found on the infected computer and demands a ransom for it.
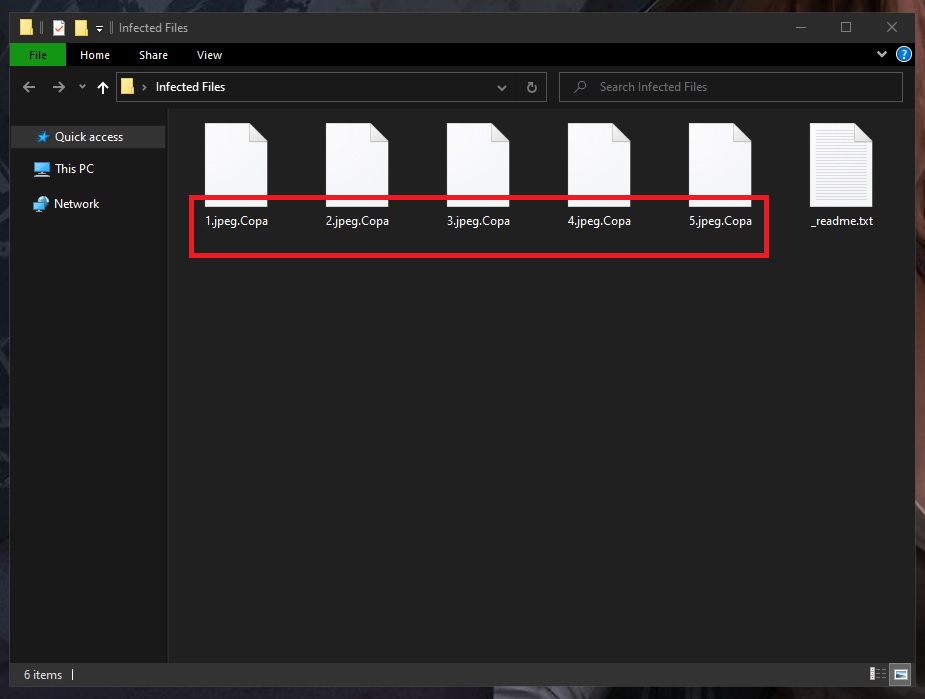
The Copa Ransomware will encrypt your files
The malicious actors who stay behind such cryptoviruses (.Kolz, Egregor) usually offer the victims with ransomware-locked files to pay a fixed amount money to them in order to receive a secret decryption key with the help of which they are said to reverse the applied encryption.
Most people give in to the ransom demands and quickly spend the required money with the hopes that this nightmare will end and they will restore their files to their previous state. Sadly, sending money to the criminals doesn’t guarantee anything. Moreover, not everyone has the exact amount of money that the hackers demand. Usually, the ransom is required in hundreds if not thousands of dollars, and raises quickly if the money is not transferred within the given period of time.
Another, perhaps even worse, problem is that there is no guarantee that you will receive the promised decryption key even if you pay. There are more than enough cases of users who comply with the demands of the criminals only to be left with empty pockets and a bunch of useless encrypted files. This is why the ransom payment option should not be your first choice when facing ransomware unless you are willing to risk your money and your files are extremely valuable.
The .Copa file decryption
The .Copa file decryption is a process in which the corresponding file-decryption key is used to return the encrypted keys to their previous state. If the .Copa file decryption key is not available to you, tryng other alternatives is your best option.
Despite the common concern, alternative file recovery methods exist and some of them are working well, thus giving every possible option a try is definitely worth it. Of course, nothing can guarantee that your files will be fully restored. However, it won’t cost you anything if you try out the suggestions listed in this post. Just don’t forget to remove .Copa before you start your file-recovery attempts because if you manage to recover some files and the ransomware is still on your system, it will encrypt them all again.
SUMMARY:
| Name | .Copa |
| Type | Ransomware |
| Detection Tool |
Remove .Copa Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

_readme.txt
Don’t……..
Your personal ID:
0253IjrfgyLmSgnnZ83QuIlpmT6YBDxONtYOXGEcfd9iC3WRc
how to get
second code for PersonalIDD.txt there
yLmSgnnZ83QuIlpmT6YBDxONtYOXGEcfd9iC3WRc
When use emsisoft decryptor software to encrypt my file
File: D:\Users\user\Pictures\stamp001.jpg.copa
Error: No key for New Variant online ID: yLmSgnnZ83QuIlpmT6YBDxONtYOXGEcfd9iC3WRc
Notice: this ID appears to be an online ID, decryption is impossible