This page aims to help you remove Cosacos for free. Our instructions also cover how any .Cosacos file can be recovered.
Attacks from programs that attempt to lock up the users’ data are some of the most common malware-related problems nowadays. On this page, we will talk about one such program, which is called Cosacos, and which belongs to the infamous Ransomware family. This particular infection operates as a file-encrypting virus (or a cryptovirus). There are many techniques that the cybercriminals use to access unprotected systems in order to infect them with Ransomware cryptoviruses, because those threats help them extort money from the unsuspecting web users. They do that by secretly encrypting the personal files stored on the infected machine, and then asking for a ransom payment in exchange for the data’s decryption. If your images, videos, audios, documents and other types of valuable data have been locked by Cosacos, and you have landed on this page seeking help on how to remove the infection, stay with us. Below, you will find a detailed removal guide and a professional removal tool for automatic detection, which may be invaluable in the fight with this harmful computer threat.
How does the .Cosacos file encryption work?
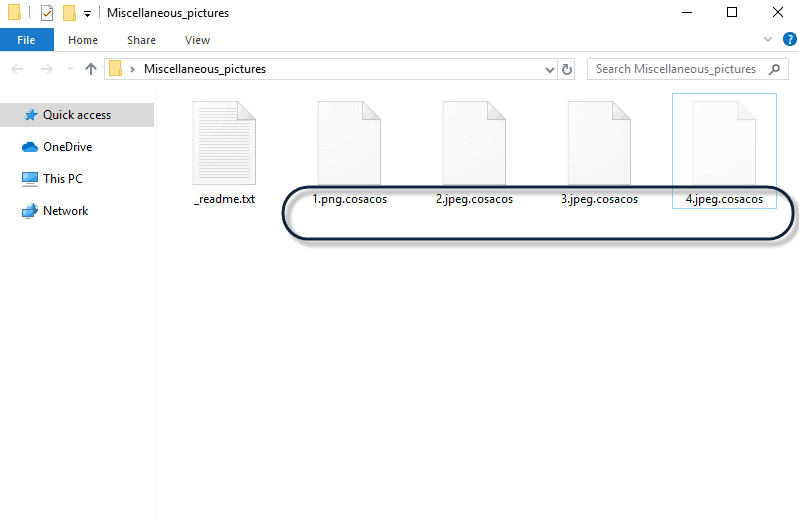
These are the infected files by a new strain of the STOP Ransomware, modifying the extension with .Cosacos
A file-encryption is a reliable data-protection method which keeps digital information away from unauthorized access. The encrypted data is accessible only with the help of a corresponding decryption key, which unlocks it. The file-encryption method has wide implementation in many business sectors and in any area where digital information should be kept safe and private. However, people with malicious intentions have found a way to use this otherwise reliable data-protection process in their favor. With the help of infections like Cosacos or Nelasod, they have found a way to secretly encrypt the information stored on the infected machines and then ask the users for a ransom payment in exchange for sending them the decryption key.
Dealing with such an attack can be very challenging. However, if you don’t immediately fulfill the hacker’s ransom demands, and instead take your time to explore the available alternatives and the legitimate methods which can help you to remove the Ransomware, you may find a working solution.
How to remove the Cosacos virus?
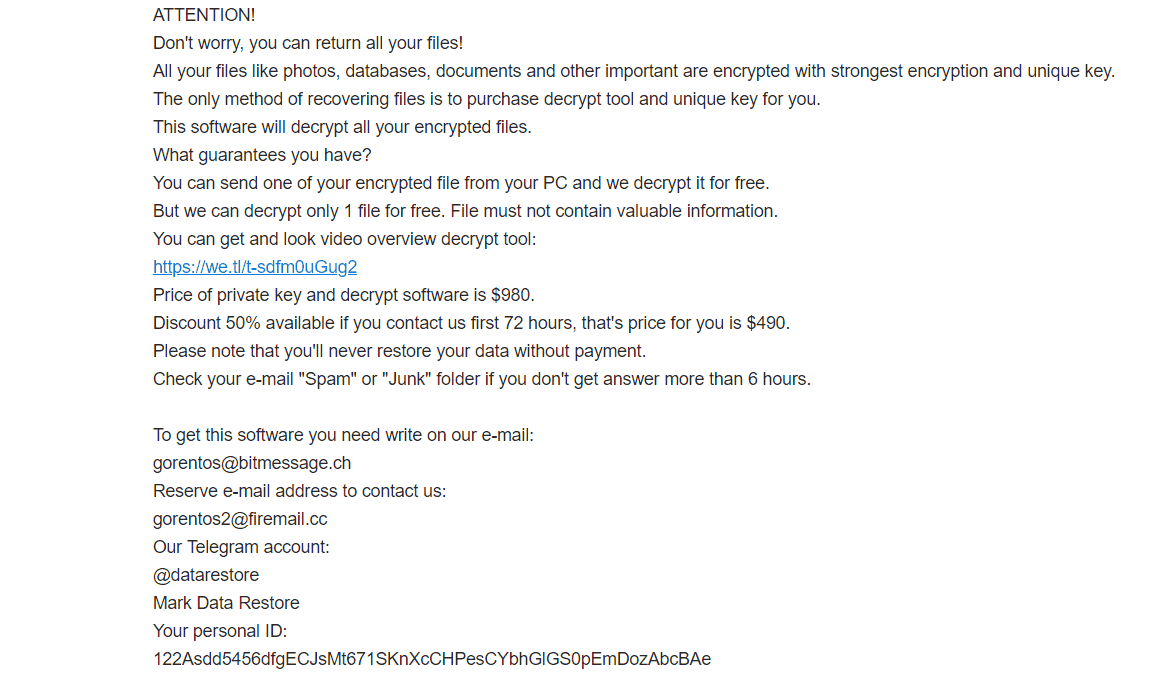
Read_Me.txt file of .Cosacos Ransomware with instructions for you to follow.
According to experts, Cosacos virus is which spreads through spam emails, seemingly harmless ads, fake pop-ups, and other “social engineering” techniques. Generally, the fake emails distributing such infections tell people about missing payments, fees, purchases, and stuff that can easily lead them to open the malicious attachment that comes in the message. In many cases, the Ransomware may sneak into your computer through fake pop-ups, which claim you need to upgrade a given program or download some update. As soon as you interact with the harmful payload, the computer gets infected. If you want to be safe, you should never trust such messages and always check the suggested updates/downloads with the official developer.
If you get tricked and the infection finds its way inside the system, don’t get panicked. Focus the malware’s removal, and explore alternative file-recovery solutions. Paying the ransom is not advisable and should only be considered if nothing else works.
To avoid losing files due to Ransomware file-encryption in the future, you should also consider a reliable form of protection. The first thing you need to do is download and install a trusted anti-malware program on your computer. In addition, make sure you regularly back up your most important data and store it on an external drive or on a cloud. This way, you can always recover it as soon as you safely remove the malware from the system.
SUMMARY:
| Name | Cosacos |
| Type | Ransomware |
| Detection Tool |
Cosacos Ransomware Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment