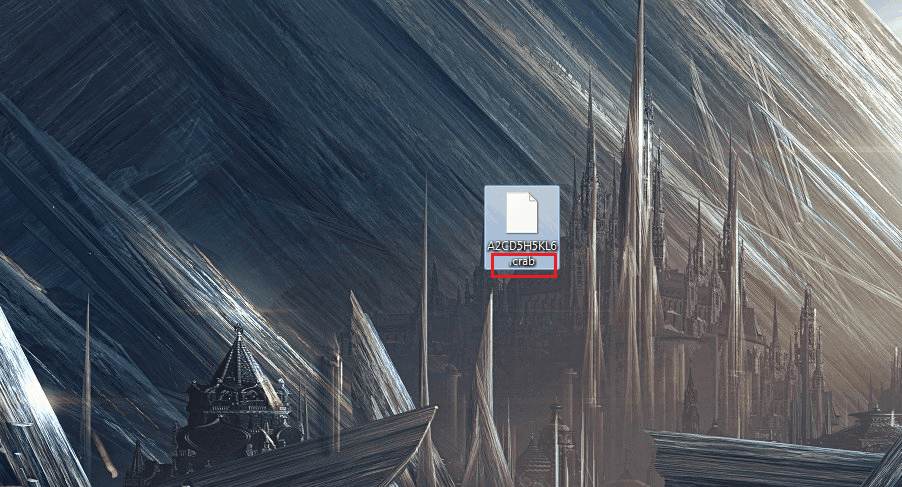
.Crab
If you have recently had a virus named .Crab virus infect your computer, then your personal data files are most likely currently inaccessible to you because the malware program has encrypted them. In such a case, you’d be asked to pay a ransom in return for a special decryption key which would supposedly set your files free.
How does Ransomware work?
Once a computer gets infected by a Ransomware, the user of the PC will likely not notice anything suspicious going on. Note that viruses like .Crab are extremely stealthy and most of the time there won’t be any overly-noticeable symptoms. Furthermore, bear in mind that even a good antivirus might be unable to spot a Ransomware infection. The reason for that lies in the process used by the malware to render the files inaccessible. We already mentioned that this process is called encryption and what’s special about it is that it isn’t actually an inherently damaging one. In most cases of Ransomware attacks. Pretty much nothing gets initially harmed by the virus. Though the files would get locked, they will remain intact. Because of this, many conventional antivirus programs could fail to recognize the process ran by the virus which would, in turn, leave the infection undetected allowing the Ransomware to continue locking the files that it has targeted until each and every file has been encrypted.
After the encryption has taken place
The second stage of a Ransomware attack is the ransom request that gets generated on the user’s computer after the encryption process has been completed. Typically, the ransom-remanding note gets generated in the form of a notepad file placed on the desktop or inside the directory where the encrypted files are. Within this note, the hackers state their demands in terms of how much money is requested and how the sum needs to be transferred. A typical method of transferring the ransom is by using a cryptocurrency such as BitCoin. This is a very common ransom request since cryptocurrencies are notoriously difficult to track and most hackers are thus able to remain unpunished for their crimes.
When talking about the ransom payment, we ought to note that making the money transfer doesn’t guarantee the restoration of your files. The hackers might or might not send you the needed key and there’s nothing you can do about it if they decide to not send it. Due to this, the payment should usually be regarded as a last resort option rather than the first thing you do once you see that your files have been locked-up. We always advise our visitors to seek alternative solutions to Ransomware infections which is also the reason why we strive to offer such possible alternatives here, on our site. Therefore, if you are currently struggling with .Crab, try out our guide that we have added down below – it includes instructions on how to remove the virus from your PC and there’s also a separate section concerning the decryption process. Though we can’t promise you that those instructions will always be successful, it is certainly preferable if you tried them first, before going for the ransom payment.
You must keep your PC protected!
Obviously, Ransomware is a significant malware threat and it is always better to simply ensure that your machine doesn’t get attacked by such a virus instead of trying to get rid of it and of its consequences afterwards. In order to properly protect your PC system against such or any other type of malware in future, you need to be very careful and vigilant when browsing the Internet as this is the most common sources of such infections.
We strongly advise you to stay away from any websites that do not seem trustworthy since visiting suspicious and questionable web addresses can significantly increase the chance of getting your machine attacked by malware. Another important rule is to never open e-mails or other web messages if you think that they look like spam – distributing Ransomware through online spam messages is another very commonly utilized method. Our next suggestion is to always have a reliable antivirus to protect your system cause it will improve your protection against Trojans. Trojan Horses are commonly used to load Ransomware into PCs that have already been infected by them so keep that in mind. Last but not least, backup any important files that you have on your PC using a separated device that isn’t connected to the computer. This is an extremely effective way of dealing with potential future Ransomware infections since the hacker wouldn’t have any leverage over you that they can use to blackmail you.
SUMMARY:
| Name | .Crab |
| Type | Ransomware |
| Detection Tool |
.Crab Virus Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Try using the instructions from the guide, hopefully this would help you deal with the virus.
You ought to remove those IPs from your Hosts file as they mustn’t be there.
I have the virus and i followed the guide. But in ny host file there wasent Another ip. And do u still have on the pc if i restert it?
If the malware isn’t removed, restarting the PC won’t do anything to remove it. Did you check the Registry Editor for any suspicious entries? Also, have you recently downloaded anything sketchy?
Yeah i download something but is there a way to remove it
Well, can you locate the file you downloaded and delete it?
hello guys .my laptop attacked by (.CRAB) virus ! is there way to remove completely or must format completely? what should i do ? all my images,files videos all got affected !
Try the guide posted on this page and also you might want to visit our special article named How to Decrypt Ransomware. Removing the virus should be possible, but we can’t guarantee that your files can be restored at this moment.
I was exposed to this virus, and I tried various methods but failed and finally I reinstalled my windows, but the file that changed to my krab still kept I moved it to my friend’s laptop, can the file be reversed?
The first thing we’d advise you to do is try some of the recovery instructions available on our site (in the How to Decrypt Ransomware article).
Hello.
I used Spyhunter 5 to remove GandCrab v5. 0. 4. I still have IPs in my hosts file underneath the local host.
0. 0. 0. 0 pubads. g. doubleclick. net
0. 0. 0. 0 securepubads. g. doubleclick. net
0. 0. 0. 0 www. googletagservices. com
0. 0. 0. 0 gads. pubmatic. com
0. 0. 0. 0 ads. pubmatic. com
0. 0. 0. 0 spclient. wg. spotify. com
Should I delete these?
Thank you.
Yes, you should most definitely delete these – they are not supposed to be in your Hosts file. Even if the main issue has been dealt with, there is no reason to keep those IP addresses in your Hosts file.