CryptInject may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Source of claim SH can remove it.
CryptInject
CryptInject is a new stealthy virus of the Trojan Horse type that can evade most antivirus programs and infect computers without symptoms. CryptInject takes over the attacked machine by misleading the user and then secretly initiates different malicious processes without getting noticed.
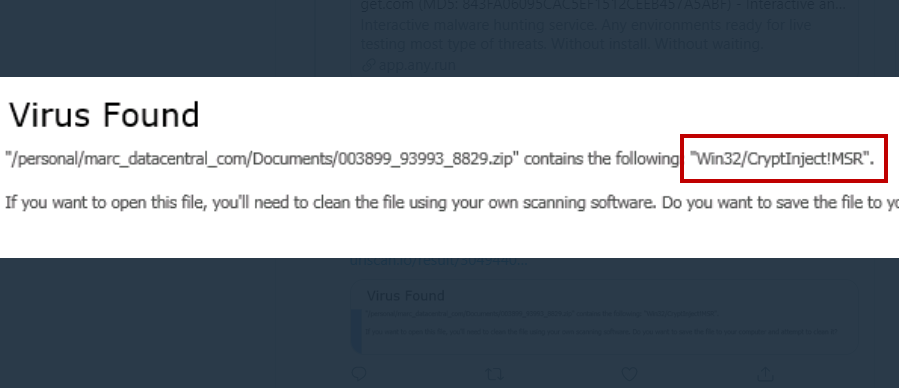
The malware programs of the Trojan Horse family are generally known for being very stealthy and difficult to detect on time. This is even more true about new threats such a CryptInject. What makes such recently released Trojan Horse viruses especially tricky to spot and intercept on time has to do with the inability of most antivirus solutions to reliably detect newer Trojan Horses. The reason for this stems from the method used to detect incoming threats by the majority of antiviruses out there. In most cases, an antivirus program would use its extensive database to recognize software that is deemed unsafe. This detection method is very effective but only against viruses that have already been listed in the database. However, its weakness is that newer threats such as CryptInject that aren’t yet added to the database are able to remain practically invisible to the antivirus. Of course, some more advanced security programs offer additional detection features to detect new threats based on behavioral patterns but, for the most part, if a given threat isn’t in the database of the antivirus, it won’t get noticed by the security program and would be free to infect the attacked computer.
The CryptInject Trojan
If your antivirus cannot effectively detect the CryptInject trojan, your only other chance of spotting the infection on time is if you notice any of its typical symptoms. Unfortunately, many Trojans don’t typically trigger any red flags that could give them away. Despite this, there are certain things you should be on the lookout for as they may indeed indicate that your computer has been attacked by a Trojan.
One of these potential symptoms is the infamous Blue Screen of Death crash. This is an error screen following a system crash that is triggered by a serious issue with the computer. Though there could be many different causes for a Blue Screen crash, a Trojan Horse infection is certainly one of them, especially if this symptom is combined with overall computer sluggishness, screen freezes, or settings changes in the system or the browser that you have not approved or made yourself.
Generally, any type of system disturbances could be a potential sign of a Trojan Horse virus so be sure to always investigate anything that seems to be out of order with your PC.
The damage CryptInject could cause
Because of their versatility, Trojans like this one are used in different cybercrime campaigns and can complete a variety of harmful actions, including spying on the user’s activities, acquiring sensitive personal and/or professional information, inserting new threats in the attacked machine, and even taking over the whole OS and starting new processes without the user’s knowledge or direct approval. All of this means that the damage that a Trojan may cause could be very unpredictable, especially if we are talking about a new threat such as CryptInject. That being said, regardless of what the end-goal of the virus is, you still must make sure to remove the threat ASAP and, hopefully, you will be able to do so after checking out the removal guide we’ve added to this article.
SUMMARY:
*Source of claim SH can remove it.
Remove CryptInject Trojan
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.


Leave a Reply