*Source of claim SH can remove it.
Dark Power
Dark Power can infect most types of operating systems out there and is generally immune to the majority of antivirus programs out there. Dark Power falls into the category of ransomware, and more specifically – its file-encrypting subtype.
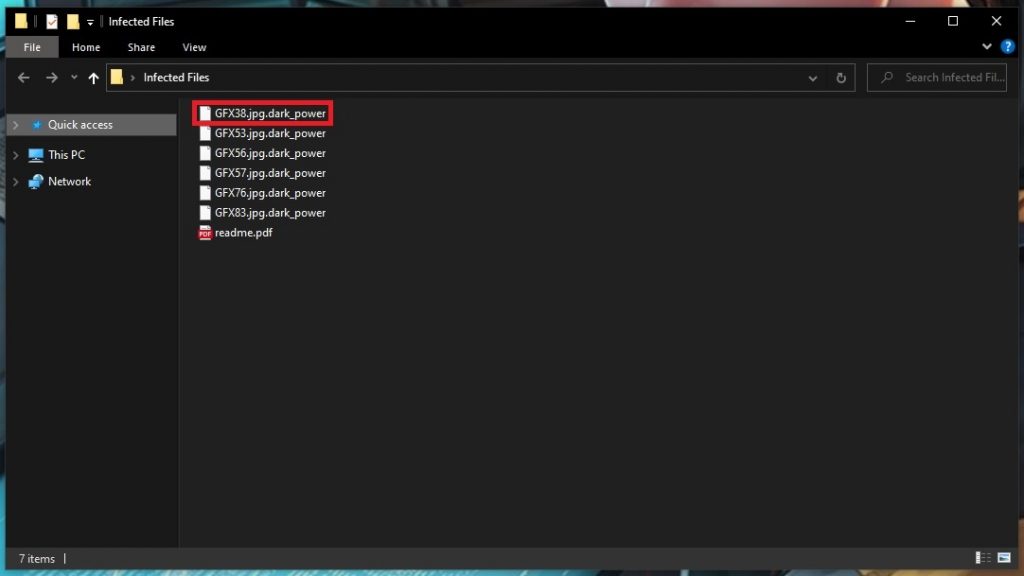
What this means is that Dark Power targets certain file types on the computers of its victims. And once it has located them and compiled a list with them all, it begins to create encrypted copies of them using a complex algorithm. Simultaneously, the originals of these files are deleted. And at the end of this tedious process, the victims are left with a long list of files that they can no longer access.
Typically, this will include all your pictures, your music, your documents, videos – pretty much everything you have stored on all your disks and drives that are connected to the PC at the time of infection. And to top it all off, you will be notified about this horrific process by means of a ransom note that will be placed directly on your desktop so you won’t miss it.
As a rule, the hackers behind the viruses like Jyos, Jywd will demand that you pay them a certain amount of money in exchange for a decryption key, which is to make the files readable again. And usually there will also be some type of scare tactic involved, like an ultimatum urging you to pay up quickly – or else…
If this sounds familiar, then the first thing you will want to take care of is the removal of Dark Power. Below is a set of removal steps that will guide you along this process. And in the second part of our guide below you will also discover a set of methods that you can try as an alternative means of recovering your data.
The Dark Power virus
The Dark Power virus acts in complete stealth and its encryption process typically won’t trigger your antivirus system. This makes variants such as the Dark Power virus highly dangerous and gives the hackers an unfair advantage.
However, there are ways in which we can still have the upper hand in the fight against ransomware. We’re talking about keeping copies of your most important data on separate drives or even a cloud. That way, even if you are attacked again in the future, the hackers won’t have anything to use as leverage to blackmail you.
The Dark Power file distribution
If you know the main Dark Power file distribution mechanisms, you also have a good chance of preventing future infections. The Dark Power file is most commonly sent around in malicious spam messages and included in malvertisements.
The latter are practically online ads that have been injected with malware, on in this case – ransomware. And upon clicking on a malicious ad like this, you more or less automatically download the virus it contains. For this reason, it’s obviously a good idea to avoid interacting with advertising content when browsing the web as there’s no way to visually tell the bad kind apart from the benign popups or banners.
SUMMARY:
| Name | Dark Power |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Source of claim SH can remove it.
Remove Dark Power Ransomware

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Dark Power files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment