*Jyos is a variant of Stop/DJVU. Source of claim SH can remove it.
Jyos
Jyos is a Ransomware cryptovirus that can make your files inaccessible by applying a secret encryption code to them. If your computer has been infected by Jyos , you will see a ransom-demanding notification somewhere on your screen.
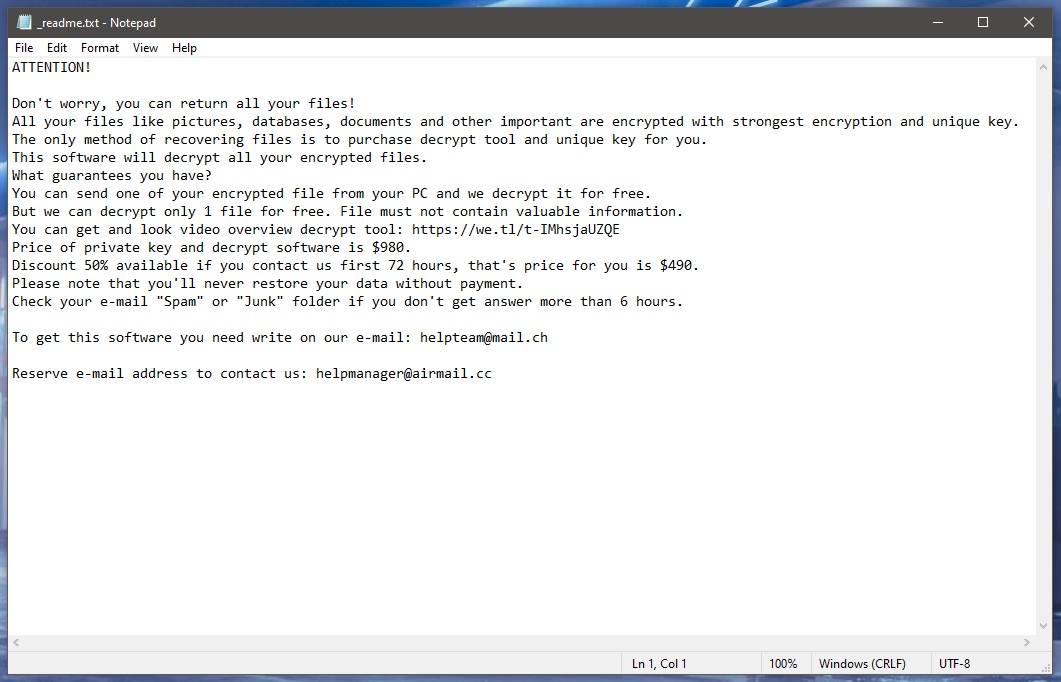
It’s not good to have a close encounter with such Ransomware like Jypo, Tyos . People who are victims of this malware category normally are denied access to their personal digital information and are required to pay a ransom to unknown hackers to regain access. Once inside the system, the malware will simply encrypt the documents, videos, audio files, photographs, and other information that is considered valuable for the victim. Then, it will demand a fixed amount of money as a ransom in return for a decryption key. Jyos is a threat that works precisely in this way. It secretly locks all the data stored on the infected computer with a complex encryption code. The virus then produces a message that demands a money transfer. Right after the attack, the hackers give instructions for the ransom payment and threaten that the user files will remain inaccessible for good if the payment is not received on time.
You may naturally feel shocked and stunned if you have found such a ransom message on your screen. However, we assume that you most likely are looking for a solution to remove Jyos and avoid the ransom payment. That’s why, on this page, we have listed some alternative methods below that do not include giving your money to the hackers. What you will find after the following paragraphs is a step-by-step removal guide to delete Jyos and some suggestions for file recovery that may help to get your encrypted documents via system backups.
The Jyos virus
The Jyos virus is a very common infection that works as a ransomware cryptovirus. The Jyos virus cannot be detected with a naked eye and this helps it to secretly encrypt a portion of digital files and ask a ransom for their decryption.
Ransomware infections are generally very different from most other viruses. In contrast to infections like Trojans, Spyware or Worms, they rarely attempt to damage the system. Rather, they use the typically harmless method of file encryption as a means of harming their victims and extracting money from them. File encryption is, in reality, one of the most trusted and unbreakable data protection methods that can be implemented in many industries such as the banking, healthcare and other sectors where digital data are to be protected. The encrypted data can only be opened or used by the person holding the appropriate decryption key. This should, of course, be the owner of the information. But in the event of a ransomware attack, it’s the hackers, who hold the key for the files of the victims.
The .Jyos file encryption
The .Jyos file encryption is a special code that converts any kind of digital files into unreadable data bits. The Jyos file encryption code is often very complex to decipher and even the matching decryption key may not be able to reverse it.

Sadly, the payment of the ransom, cannot guarantee the restoration of the encoded files. The hackers can simply vanish with the money and the victims may never receive a decryption key from them. Or the key may not function properly and may fail to decode the complex encryption code that has been applied. This gives us a good reason not to pay the money but to choose alternatives. Therefore, we suggest that our readers opt for solutions that can help them remove Jyos instead of sponsoring the hackers behind it.
SUMMARY:
| Name | Jyos |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
| Detection Tool |
*Jyos is a variant of Stop/DJVU. Source of claim SH can remove it.
Before you start Here are four important notes that must be pointed out before the start of the guide.
- First, make sure to disconnect any device with internal memory (phones, USB sticks, external drives, etc.) from your PC to prevent the encryption of the files that are on it.
- Next, it’s advisable to keep your PC disconnected from the web in case the Ransomware tries to communicate with its server while you are trying to delete it.
- Thirdly, if you are considering the ransom payment as a possible option, it may be better if you don’t remove the virus just yet. Instead, it’s better to leave its removal for after the ransom is paid and your files have (hopefully) been restored. If you delete the virus before that, you may never get the decryption key even if you pay. That said, we advise against opting for the ransom payment.
- Finally, even if the virus seems to be gone from your PC (many Ransomware threats automatically delete themselves after completing the encryption), it’s still recommended that you finish the guide below.
Remove Jyos Ransomware
To remove Jyos , the following steps need to be complete in the given order:
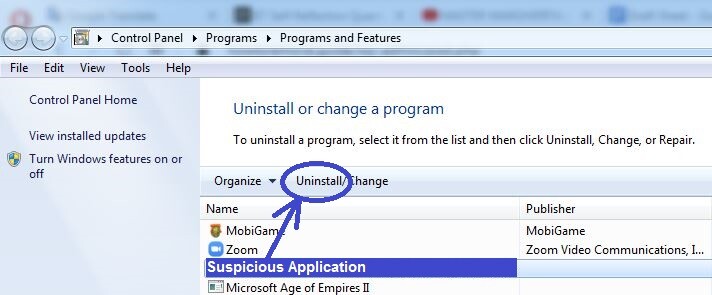
- If there are any recently installed programs that you suspect of being connected to the infection, uninstall them.
- Check what processes are running in the system and stop the ones that seem questionable.
- Any changes made by the virus to the system’s settings should be revoked.
- To remove Jyos , the final thing to do is to find and delete all malicious files located in the computer.
With the help of the instructions below, you should be able to complete each of those steps. If you have any questions, you can use the comments section to ask them.
Detailed Guide

To look for recently installed rogue programs, go to the Start Menu, open the Control Panel and select the option labelled uninstall a Program. Now look at the installation dates and if you see there’s a questionably-looking program added right before the virus locked up your files, select that program and then click the Uninstall button from the top to begin the uninstallation process.
Note: If you are offered to keep any settings or other data related to the program you are uninstalling, refuse that offer and make sure nothing from the program is allowed to stay on the computer.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Jyos is a variant of Stop/DJVU. Source of claim SH can remove it.
Press the [Ctrl] + [Shift] + [Alt] keys and open Processes. Sort the list by Memory/CPU usage and look at the items shown to have the highest usage of the respective resource. If any of them have questionable names, use another device with Internet connection to look up their names (because your PC should currently be disconnected from the web).
If you find any information shared on trusted cybersecurity forums or other cybersecurity sites that states the process you looked up could be malicious, you should end the latter and delete what’s inside of its location folder.
If you didn’t find relevant information or you want to be sure that the process is harmful, one other reliable way of checking it is to right-click on it, open the File Location folder, and scan the files located there with a reliable anti-malware scanner. You can find one such powerful scanner right below – visitors of our site can use the scanner for free and since it requires no installation, one can use it directly from this page.


If one or more of the location folder files are found to be malicious, quickly go to the rogue process, end it, and then delete the location folder. Anything that you may not manage to delete right now, you should be able to remove by the end of the guide, so be sure to delete any files that may be left once you are done with the guide.
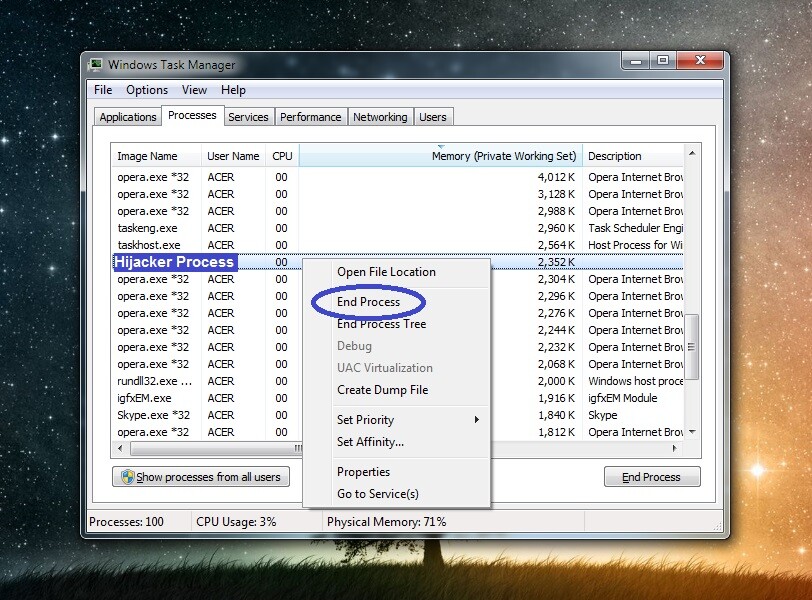

Jyos may attempt to start its process(es) again, or you may not have ended them all, to begin with. In either case, it’s best to enter Safe Mode, as this will hopefully prevent the virus from launching any more harmful processes.

*Jyos is a variant of Stop/DJVU. Source of claim SH can remove it.
Now it’s time to delete the virus files, but before you attempt to do that, you must first “unhide” any hidden files and folders that are in the system. To do this, go to your Start Menu, type in its search box Folder Options, and press Enter. In the window you will be taken to, select View and then find an option labeled Show Hidden files, folders, and drives and put a tick in the box next to it. It’s also recommended that you uncheck the following two options from the list:
- Hide extensions for known file types
- Hide empty drives in the Computer folder
Once you are done, click OK, and then, one by one, copy the next lines, place them in the Start Menu search, and hit Enter after each one.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete all data that has been created after the virus attacked you in the first four folders. As for the final one (Temp), simply delete everything that’s stored inside it.

Search for msconfig in the Start Menu, open the app that shows up, and go to Startup. Remove the ticks from the boxes next to all items that you don’t recognize or that have unknown developers, and select OK.
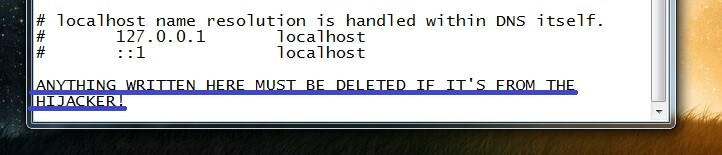
After that, open This Computer, go to the drive where your OS is installed (in most cases that would be drive C:), and then navigate to the following folder: Windows/System32/drivers/etc. There, you must find a file named hosts and open it using Notepad. Next, from the file, if there is any text or strange IPs below “Localhost”, copy what’s there, paste it in the comment section, and wait for our reply. We will soon tell you if what you have sent us is from the virus and if you would need to delete it from your Hosts file.

This final step focuses on cleaning the Registry from rogue items and since there are many sensitive settings for Windows stored in the Registry, you must be very cautious, so you don’t end up deleting anything you aren’t supposed to.
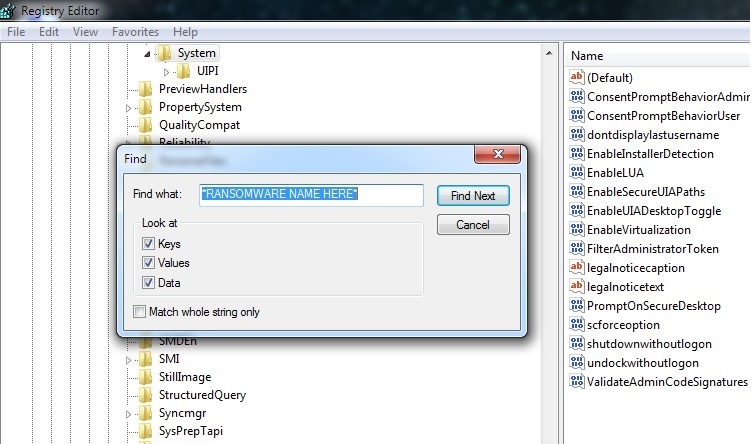
One way you can access the Registry Editor tool is to open the Start Menu, search in it for regedit.exe, and to open the app with the same name that appears in the search results. Windows will then ask for your approval, so select Yes when that happens to open the Editor.
From the Editor window, select the Edit button and click Find from the drop-down menu. In the Find window, type Jyos , click Find Next to search for related items and delete the item that gets found. Keep searching for more items and keep deleting them until nothing related to Jyos is left.
Finally, navigate to the directories shown below by manually expanding the different folders in the left sidebar.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
Look at what items are present in each of the locations and if you find anything with a long and random-looking name similar to this “2390r98ehd98et89r323928ry3298dh9823hhd”, delete it. Of course, if you think you may need help determining if a given item must be removed, the comments section below is open to you, and you are free to use it to ask us about such items.
If the manual steps didn’t help If Jyos is not going away no matter what you do and despite you having completed the manual instructions above, it’s best to either consider taking the computer to an IT professional who can personally have a look at it or to use the help of a reliable security tool that can take care of the infection for you. The good thing about the latter option is that it has the potential to save you tons of time, but you must know what program to use to successfully remove Jyos . One program that we believe can help you with that has been shared throughout this guide, and we highly recommend using it to clean your computer from the malware.
How to Decrypt Jyos files
To decrypt Jyos files, our recommendation is to try whatever alternative methods you can find rather than paying money to the blackmailing hackers. Before you try to decrypt Jyos files in this way, however, you must first ensure that the computer is clean from malware.
If, for example, there are still suspicious files on your PC that look like they could be harmful, remember to use the scanner offered on our site to test them for malicious code and delete them if such is detected in them.
Decryption tool
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Once the PC is clean, you can then safely proceed to the data recovery process – in our How to Decrypt Ransomware article, we’ve shared the best alternative recovery methods we’ve been able to find alongside instructions on how you can use them on your PC.
Jyos is an advanced form of computer malware that belongs to the Ransomware file-encrypting category. The main goal of the Jyos Ransomware is to extort money from you by keeping your files encrypted and demanding a ransom payment for the private decryption key. This type of malware has persistently been one of the most serious cyber threats for the past 6-7 years, and it doesn’t appear to be slowing down. Currently, hackers are using advanced Ransomware viruses to extort millions from big companies, organizations, governments, and more. In the case of Jyos , however, the main target seems to be regular users. Once the malware infiltrates the user’s system, it secretly launches a file-encrypting process that soon renders inaccessible all files on the computer that belong to a predetermined list of file types. Those file types are normally commonly-used ones such as text, audio, video, and image files as well as spreadsheets and other office files. This increases the chances of encrypting data that’s important to the user.
Jyos is a Ransomware virus that aims to put encryption on your files in order to later get you to pay a ransom for the corresponding decryption key. The Jyos virus automatically reveals its presence in the system after the encryption through a ransom-demanding note. The note details how the demanded ransom is supposed to be paid. In most cases of Ransomware blackmailing, the hackers behind the attack require the money to be sent to them in the form of Bitcoins or another cryptocurrency – this is to help keep their anonymity and avoid getting traced by the authorities. In most cases, paying the money for the decryption key is not an advisable course of action, and we try to discourage our readers from opting for this. The main reason is the fact that you cannot know if this would have the desired effect and if you’d get your files restored. The only certain thing is that you’d lose any money you pay to the hackers.
To decrypt Jyos files, we recommend that you try using alternative data-recovery methods rather than transferring your money to the blackmailers. Paying the ransom in an attempt to decrypt Jyos files doesn’t guarantee that you will get the decryption key or that it will work. Unfortunately, there are no alternative file-recovery methods that work one hundred percent of the time. However, it’s still worth trying the ones that are available to you to see if they get the job done because this could potentially save you a lot of money. One possible thing you could try is to use a free decryptor tool – many such tools developed by reputable security companies are available on the Internet, but they are usually Ransomware-specific, which means that you’d need a decryptor designed especially for unlocking Jyos files. Shadow-copy restoration is another thing you could try – sometimes, there are older versions of the encrypted files stored deep within the system, and you may be able to recover them. Of course, if nothing else works, you could still pay the ransom, but this should really only be seen as a last resort option.

Leave a Comment