Dewar
Dewar is a very malicious file-encrypting threat that belongs to the Ransomware category. In return for retrieving your personal files, Dewar asks you to make a ransom payment to a given cryptocurrency account.
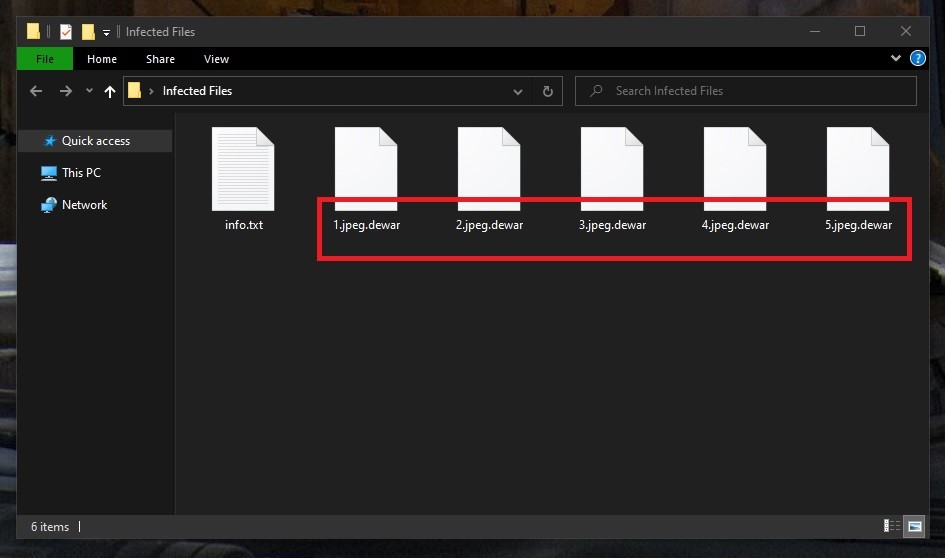
The Dewar Virus will encrypt your files
If your work-related documents, photos, videos, and other important information have been blocked by means of encryption and a frightening ransom note has demanded you to pay some money to regain access to them, there is a strong reason to be scared. Most probably, you have fallen victim to Dewar which is one of the latest ransomware cryptoviruses that can be found on the web.
This malware works by applying complex code encryption that does not damage your files or device like many other forms of malware. This means that if you fall victim to Dewar, you will not have your data corrupted, but you will have it locked with a powerful algorithm that’s almost unbreakable. The file encryption approach is used only to intimidate the victims and to allow the malicious actors behind the Ransomware to ask those who want to decrypt their files to pay a ransom.
This illegal money-making scheme has, unfortunately, evolved into a lucrative business model for various hacking organizations, and they have come up with new and advanced threats of this type. Victims are normally promised to recover their documents with the help of a decryption key if they pay the required ransom money. However, no assurance is actually given that they will receive the decryption key from the crooks behind the ransomware.
The Dewar virus
The Dewar virus is a stealthy ransomware infection that encrypts user files and holds them for ransom. The Dewar virus can hardly be detected, since it is well hidden in the system, with very few visible symptoms.
As the malware sneaks into the device, the information is encrypted immediately, but hardly any obvious signs will suggest the malicious event. Only when the whole encryption process is complete will the cryptovirus be detected and this will usually happen when a ransom note appears on the screen. In general, the hackers will do their best to convince you about the harmful consequences of not paying the ransom. They will set a deadline and may threaten to delete all of your information if their demands are not met. Some versions of ransomware may even play an audio file that tells you what has happened to your information. All this is done to make the victims pay as quickly as possible and not give them time to remove the infection.
The Dewar file encryption
The Dewar file encryption is a method that people with criminal intentions use to encode user files and keep them inaccessible. The Dewar file encryption file can be very difficult to reverse. Therefore, even the corresponding decryption key that the hackers keep in secret may not be effective.
In many cases, the hackers don’t really send the victims a decryption key when they pay. That’s the reason why many security experts advise against giving your money to the crooks behind the ransomware. Taking the initiative in your hands and having the ransomware removed instead of risking your money is a good alternative, though, and our instructions may be able to help.
SUMMARY:
| Name | Dewar |
| Type | Ransomware |
| Detection Tool |
Remove Dewar Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

I am Sunardi from Indonesia
The files on my computer got the Dewar ransomeware virus.
can you help me in overcoming this problem.
thank you for your attention
Hi sunardi, go to this page and try to find the decryptor for the ransomware which has encrypted your files.