*Source of claim SH can remove it.
Dllhost.exe
The Trojans Horse infections are at the top of the list of the most dangerous and most widespread forms of malware, and Dllhost.exe is one of them. If you are reading this, you have probably come to this page because Dllhost.exe has invaded your computer, and you are interested in learning how to get it removed.
What is Dllhost.exe?
Dllhost.exe is a legitimate Microsoft Windows process and it is located in the C:\Windows\System32\dllhost.exe. Often times viruses can mimic these processes so they can confuse the OS and the user and continue doing their malicious tasks. If Dllhost.exe is found anywhere outside C:\Windows\System32\dllhost.exe it might be a lurking virus, so we suggest to you to make a thorough scan of your system.
In that case, we must tell you that removing an infection of this kind may not be an easy task, and you will need to carefully follow our instructions in order to successfully make this infection go away. If for some reason our manual instructions don’t work for you, or you are unable to complete them, you can also use the help of the professional anti-malware program that you will find linked in the guide. Using it to remove the Dllhost.exe Trojan is another reliable option in the fight against this malware threat. Before you get to the guide, we advise you to finish reading this article, so as to get an idea about the characteristics of the malware you are currently dealing with. Being well informed about the abilities of any given form of malware is essential in keeping your system protected against that threat.
Dllhost.exe and other Trojans – some important information
As you probably know, the Trojan Horse representatives (Walliant, Wup.exe) are extremely stealthy malware programs that try to stay hidden in the infected computer for as long as possible. Some other kinds of malware, such as the Ransomware cryptoviruses, for example, tend to reveal themselves at a certain point.
The Dllhost.exe Virus
Not the Trojan Horses – a Trojan such as the Dllhost.exe virus is likely to remain under the radar for the time it is in your computer, and it is up to you to find a way to spot such threats. In your case, you already know, or at least suspect, that the Dllhost.exe virus is in your computer, which is actually good.
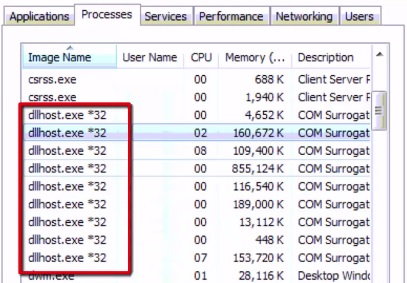
You are a step closer to getting rid of the malware now that you know it is there. Note, however, that oftentimes Trojans are able to disguise their files and processes. They tend to name them after files and processes that belong to the OS, so that it becomes difficult to distinguish them and remove them. Still, there are methods to find out if a given file is related to your OS or is coming from a Trojan. For instance, if there are two system files of the same name, one of them is probably related to malware in your system. The same applies to the processes in your Task Manager. Also, most system files have specific locations, and can’t be found elsewhere. Therefore, if you see a system file in a folder where it isn’t supposed to be, know that it is probably the disguised file of some Trojan.
Trojan Horse versatility
Espionage on the user, theft of banking details, inserting of Ransomware and other threats in the computer, and turning the machine into a bot for cryptocurrency mining are only few of the many ways in which a Trojan can be used. Your job is to make sure that Dllhost.exe isn’t allowed to complete its task, and the guide below will hopefully help you with that.
SUMMARY:
| Name | Dllhost.exe |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Remove Dllhost.exe Virus
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


*Source of claim SH can remove it.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment