If you joined the number of victims who have found the Emotet Trojan Horse on their computer, this post and the removal guide below might be exactly what you are looking for. Emotet is a very stealthy Trojan-based virus and it’s very lucky you’ve been able to identify it before (hopefully) it has completed its agenda.
Emotet
Emotet is a dangerous malware known as a Trojan Horse. This type of malware is considered to be potentially very dangerous and Emotet is certainly one to be removed as soon as possible.
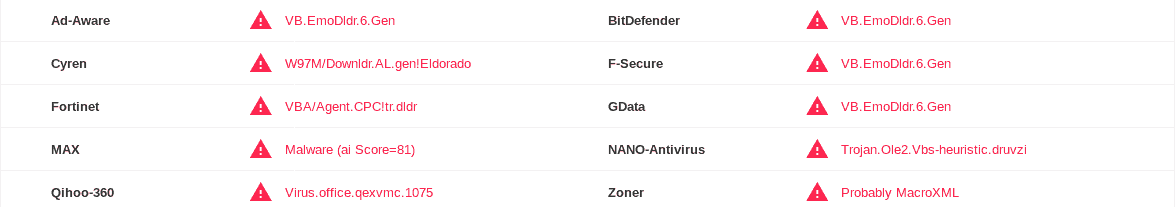
Multiple antivirus scanners show the issue with the Emotet Virus.
Threats like this one are widely used to help other kinds of malware enter the computers of the web users. They are most often used as a backdoor to Ransomware or Spyware viruses. In addition, a Trojan like Emotet can assist the hackers to gain remote access to your machine and exploit its resources for whatever criminal deeds they may need. That’s why, in the next lines, we will help you remove Emotet from your system and prevent it from harming you any further.
You’ve probably heard about the Trojan threats before and understand they can be quite hazardous. These infections, and more specifically the newest representatives, such as Emotet, are the hackers’ favorite instrument because they are so versatile and are able to perform a variety of malicious operations. Proof of this is the fact that only the Trojans make almost three-quarters of all malware assaults on the internet. They can also be extremely stealthy, and, thus, very hard to detect. That’s why we started by stating how lucky it is that you’ve even been able to identify Emotet on your system and seek help to remove it because most victims can be totally clueless about the infection for months or even years.
Emotet targets Mac
According to researchers Emotet is a malware of the Trojan Horse variety. A threat such as Emotet is considered quite serious and should be regarded as a high priority risk.
And for that time, they can initiate a number of criminal activities. For instance, if the hackers decide, they can program the Trojan to delete all the information kept on your computer and destroy it forever. Not to mention that it is also possible for the crooks to wreck the victim’s operating system entirely. But Trojans are used more frequently for things like espionage and theft. By tracking your keystrokes and keeping track of your internet activities, threats like Emotet can obtain information about you, and this means having access to highly sensitive data, including passwords and financial or banking details. They can also allow the criminals to watch and even listen to you remotely by gaining access to your webcam or mic. They can even watch your screen and see everything you do while the computer is working. Therefore, the sooner you remove the infection from your system, the better the chance to save yourself from those frightening scenarios.
The Emotet Virus
Emotet has been labeled a Trojan Horse virus by security experts and should be removed as soon as possible. Emotet could be a harbinger of different security threats like keyloggers, fishing attempts and even ransomware.
Unfortunately, you may have been infected with this malware in many ways. Some of the most typical sources of Trojans are spam messages and infected attachments or links, as well as different pop-ups such that evoke false system update requests and alerts for virus infection. Such threats may also come in the form of attractive ads or “you won a prize” messages that request you to fill in your personal information. But don’t be foolish about that. If you don’t expect some correspondence or something about a particular email it is best to leave it intact and likely just delete it immediately. The same principle applies for any system/security software request – do not interact with it unless this is a valid notice from your software developer, as it may potentially carry some malware.
SUMMARY:
| Name | Emotet |
| Type | Trojan |
| Detection Tool |
Remove Emotet Mac Virus
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment