One of the most devastating kinds of malware is the infamous Trojan horse type. Having such a virus on your PC can be a real pain in the neck, since it can cause all sorts of issues. Trojans are known as being extremely versatile and hackers can use them for a wide variety of malicious and harmful tasks. Today, you are about to be introduced to Emotet Malware, which is one of the latest Trojan horses. You will learn what it can potentially be used for as well as what you can do in order to detect it if it gets on your computer. Since many of this article’s readers have probably come here because the virus has already invaded their PC, we can also help you remove it and bring things back to normal. There is a removal manual below where you can find instructions on how to eliminate the malicious virus so go there and complete the steps if you need to.
Emotet
Emotet is a Trojan threat that can collect personal or professional information about the victim through espionage. In many cases, Emotet can keep tack of the victim’s keystrokes on their keyboard or hack into their webcam and microphone to record them.
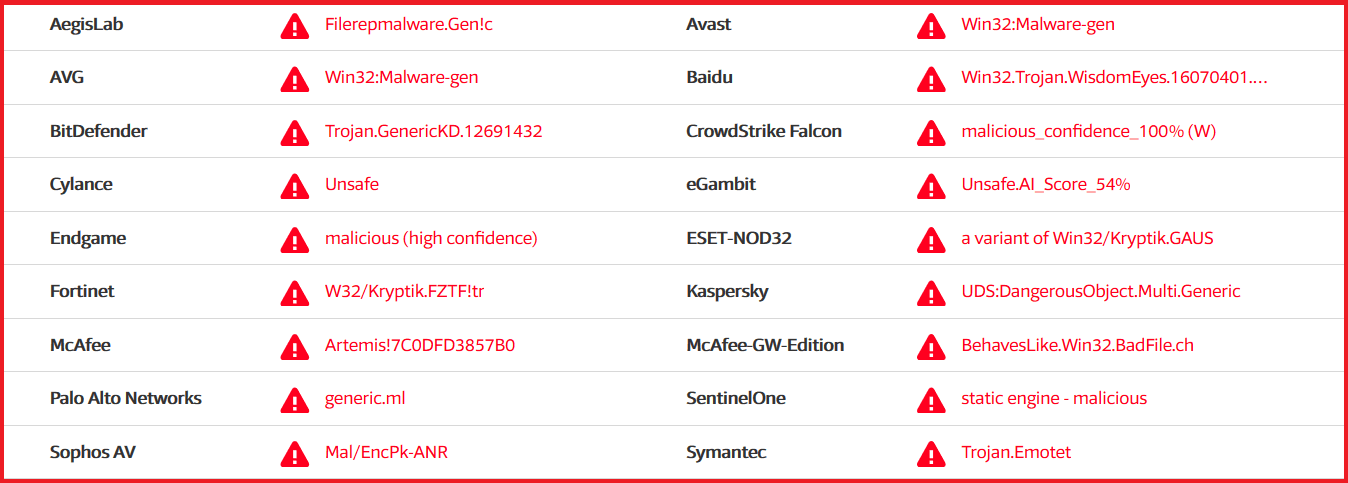
After running multiple VirusTotal scanners we can see the nature of Emotet.
As was already stated above, a typical Trojan horse virus can be employed in a number of different ways depending on what the cyber-criminal is trying to achieve. Here are a few examples of the tasks that a virus like Emotet Malware might be used to execute:
- System damage – Harming one’s PC is a very common use of a Trojan horse virus. It can potentially cause the machine to crash and stop responding, trigger system errors or mess with the OS files which could lead to all kinds problems. Trojans are one of the most destructive types of malware and the damage they can inflict might even render the PC utterly unusable.
- Surveillance/spying – Trojans can also be used to spy on their victims and there’s no shortage of methods to do that either. The keylogging technique can be used to monitor what the user types on their keyboard and there’s also the possibility that the hacker uses the virus to directly see what’s happening on the user’s PC screen. In addition to that, the webcam can also be used to stalk the virus’ victim without the latter realizing that their webcam is actually being used.
- Spreading malware – Viruses the likes of Emotet can also be used to infect the user’s PC with other types of harmful software (for example, Ransomware). Once the Trojan enters the PC and is run/installed under elevated privileges, it could provide other viruses with a gateway into the infected computer.
- Taking over the PC – Another thing that many Trojan horses are capable of is taking control over the attacked machine’s system. Once the malware infects the targeted computer it might be able to start using its resources for the hacker’s benefit. For example, the virus might force the infected machine to send out spam e-mails to other users or mine bitcoins for the cyber criminal who’s using the virus.
There are many other potential uses of a Trojan horse virus. The ones mentioned above are only some of the most commonly encountered ones. Truth being told, as long as Emotet or any other similar virus has gained elevated privileges on your PC, it would most likely have unlimited access and would probably be able to do with your PC whatever it is commanded by the hacker. That is why Trojan horses are so widely spread and such a big problem.
The Emotet Malware
Emotet is classified as a Trojan Horse which will secretly oversee the user’s activities and will also remotely control certain aspects of the computer. If you are infected with Emotet your system can also lead to loss or corruption of digital data and system records.
When it comes to detecting Trojan horses, having reliable antivirus software on your PC with its latest updates installed is crucial. Spotting a virus of this type by simply trying to notice its symptoms can be really difficult since oftentimes the signs of the infection will be reallyб really subtle or non-present at all. This is why you need a good security tool to help you detect any potential malware of the Trojan рorse type. As far as the potential symptoms are concerned, the most typical ones are frequent BSOD (Blue Screen of Death) crashes, random system errors, slowed-down PC productivity, RAM and CPU spikes, any unauthorized system changes, overall odd PC behavior. Note that not all Trojans cause thуse symptomsб which is why it is still necessary to have an antivirus program.
Anti-Trojan horse precautions
It should be fairly obvious by now just how important it is that you keep your PC safe and well-protected against computer viruses the likes of Emotet. If you want to ensure that your machine does not get infected by any Trojan in the future, be sure to read, remember and employ the following tips and guidelines:
- Keep away from any web-addresses that seem to be suspicious and that could be potentially illegal and harmful.
- Do not open or interact with the contents of any e-mails or Facebook/Skype messages that could potentially be spam.
- Keep your Windows firewall and antivirus program constantly enabled and never forget to install the latest updates to your OS and antivirus (if they do not get automatically installed).
- Be careful with any web-ads, browser notifications and online offers that might seem shady and obscure. Do not click on anything in your browser that you cannot fully trust.
- Change the settings of your browser so that you are always asked for permission before a new file gets downloaded. One way to do that is to set your browser to always ask you to provide a download directory instead of using an automatic/default one or all downloads.
SUMMARY:
| Name | Emotet |
| Type | Trojan |
| Detection Tool |
Emotet Malware Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment