Entertainment.exe may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Source of claim SH can remove it.
Entertainment.exe
Trojans like Entertainment.exe are widely known to be among the most dangerous types of malware that users may face. Despite the public’s understandable concern, however, many people remain unaware of the specific dangers posed by infections of this type.

When infected with a Trojan horse application like Entertainment.exe, users often panic and have no idea what to do. Therefore, in this article, we will not only explain the specifics of this malware but also provide you with a detailed guide that can help you remove it. We have also included a link to a professional removal program that will get rid of Entertainment.exe for you quickly and effectively.
Once a Trojan has infiltrated a system, it is quite difficult to identify it, since the malware hardly causes any noticeable symptoms. In some rare occasions, however, your computer may become sluggish, unresponsive, or crash for no apparent reason, which may serve as an indication of malicious activity in the background.
Entertainment.exe is an example of malicious software that might provide hackers access to your data and lead to a variety of problems inside the compromised computer. Due to its versatility, it is very difficult to predict what the Entertainment.exe infection is up to on your machine.
What harm can Trojans do?
One of the most malicious uses of Trojan viruses is theft of sensitive data. Entertainment.exe and other threats like Altruistics have been known to use a number of techniques to get access to users’ private information. Your social media, banking, shopping, and other account credentials, as well as your credit card and personal details, could all be targeted. Aside from stealing different types of data, Entertainment.exe is a danger that may be used to delete certain files or wipe off everything that is stored in the infected system.
And this is not everything. Such a Trojan may be used by hackers as a tool for espionage. With its help, the crooks may eavesdrop on you using your camera and microphone. In this way, they can potentially learn your physical location, view your online activity, and listen in on any conversations you may be having, both in person and online. They may also hack your passwords and personal information through techniques such as keystroke logging and screen-sharing.
Other dangerous uses of a Trojan infection include the distribution of spam or malicious software through exploitation of the resources of your infected computer. Trojans may even be programmed to mine cryptocurrencies on your machine and send it to the hackers. Furthermore, viruses like Entertainment.exe might allow other forms of malware to infect your system through a backdoor.
Now that you know just how many problems Entertainment.exe may create, you should follow the steps in the removal guide below to get rid of the Trojan and learn how to be safe.
Protecting your computer against Trojans and other forms of malware is essential if you want to avoid a face-to-face confrontation with them in the near future. If you want to stay away from online dangers, consider the following safety recommendations:
- Use a top-notch, up-to-date anti-malware program.
- Do not postpone installing system updates when they become available
- Try to avoid the most common online virus sources by keeping your system up to date and using a firewall. That includes adult-oriented sites, torrent and file-sharing sites and other questionable platforms for free and unreliable software.
- Be wary of opening spam emails since they might contain viruses, and stay away from questionable email attachments.
SUMMARY:
*Source of claim SH can remove it.
How to Remove the Entertainment.exe virus
To remove the Entertainment.exe virus, users must first clean their systems from rogue programs and disable any rogue processes after which they must restore any system settings modified by the Trojan.
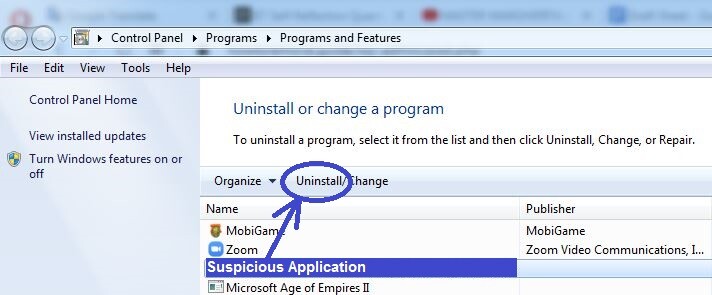
- The first step is to check the Programs and Features list for potentially harmful program installs and remove anything that may be unwanted.
- The next thing to do is disable any malware processes in the Task Manager.
- Thirdly, the user must restore the DNS settings as well as revoke changes made to the Hosts file and Startup Items list.
- The last thing that must be done to manually remove the Entertainment.exe virus is to delete any harmful/rogue items from the System Registry.
To learn more about how each of the steps above needs to be performed as well as to get some extra tips, please read the extended version of the guide shown below.
Extended Guide
System restarts will be required to complete the guide and so, to find this page more easily after the computer starts back up again, it may help if you bookmark it in your browser.
Step 1
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Source of claim SH can remove it.
If there are any questionable programs in your computer, those must be uninstalled because one of them could be what infected the system with XXX.
You can see all program installs by going to Start Menu > Control Panel > Uninstall a Program. In that list, look for items that were installed not long before the presence of XXX on your computer became apparent. If you see a suspicious or unfamiliar program installed in that time period, select it, and then select Uninstall. After that, complete the uninstallation process while also making sure that no data related to the program is allowed to remain on the computer.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Source of claim SH can remove it.
Now you must find the Trojan Horse processes and stop them. To look for malware processes that are currently running on your computer, press Ctrl + Shift + Esc to start the Task Manager and check its Processes tab. In that tab, you will see all currently active processes – the one (or ones) coming from Entertainment.exe are likely to be using high amounts of CPU power and RAM memory, so first focus on the most resource-demanding processes. See if among them, you notice any items with odd or unusual names and if you do, look up those names.
If any of the suspected processes is malicious, you should be able to quickly find online reports from reputable sources confirming that. If this happens to be the case, you must go to the process-right-click on its name, and select the first option from the menu. This will open the file location folder of the process – you must now scan the files contained there to see if any of them is a threat. We recommend using the powerful malware-scanner shown right below – it is free, and you can use it directly from the browser without need to install anything.


If the scan finds malware in any of the suspected process’ files, then you must immediately go back to the process and quit it (right-click on the process > End Process). After that, make sure to delete its location folder. If that can’t be done at the moment because one or more files in the folder can’t be removed, delete the others and go to the next step. When you are done with the whole guide, you should be able to delete what remains of the file location folder so make sure to do that.
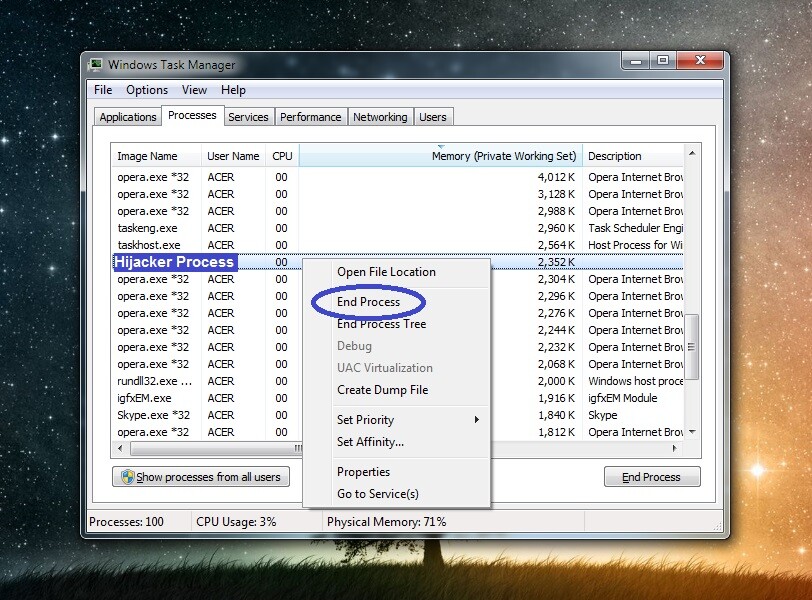
Note: If you are convinced that a given process is malicious, you should quit it and erase the file location folder even if none of the files from that folder get detected as threats.
Step 3
For the remainder of this guide, your PC should stay in Safe Mode to prevent the malware from interrupting your progress.
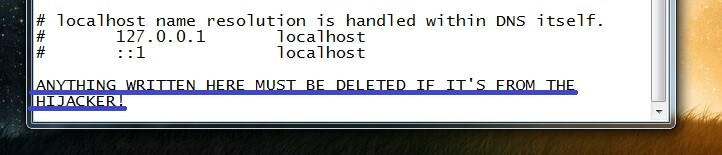
Step 4
Open Run by pressing the Ctrl and R keys and copy past this line: “%windir%/system32/Drivers/etc/hosts” in the window that pops-up. Press the Enter key and when a text file named Hosts appears on your screen, explore the text in the file and see what’s written towards its end. If the file hasn’t been manipulated by the virus, the last thing written in it should be “Localhost“. In case there’s anything after that, copy it and post it in the comments on this page. We will reply to your comment soon after, telling you if what you’ve sent us is from the Trojan and whether you should remove it from the Hosts file.
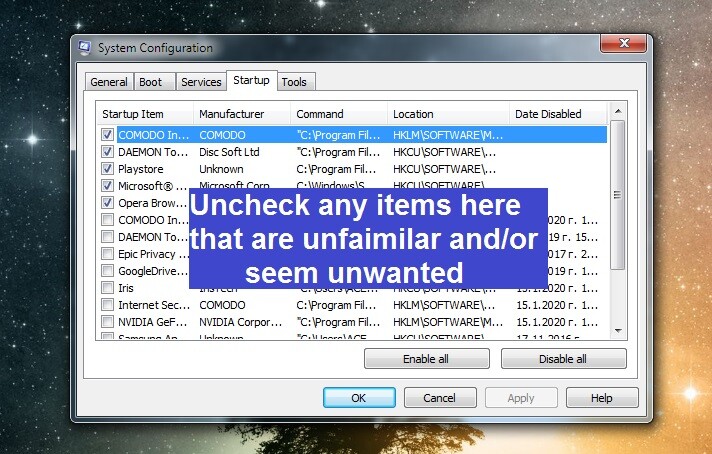
Next, type msconfig in Run, press Enter again, and check the Startup tab for suspicious or unfamiliar entries. If you see anything that should probably not be there, disable it and click OK.
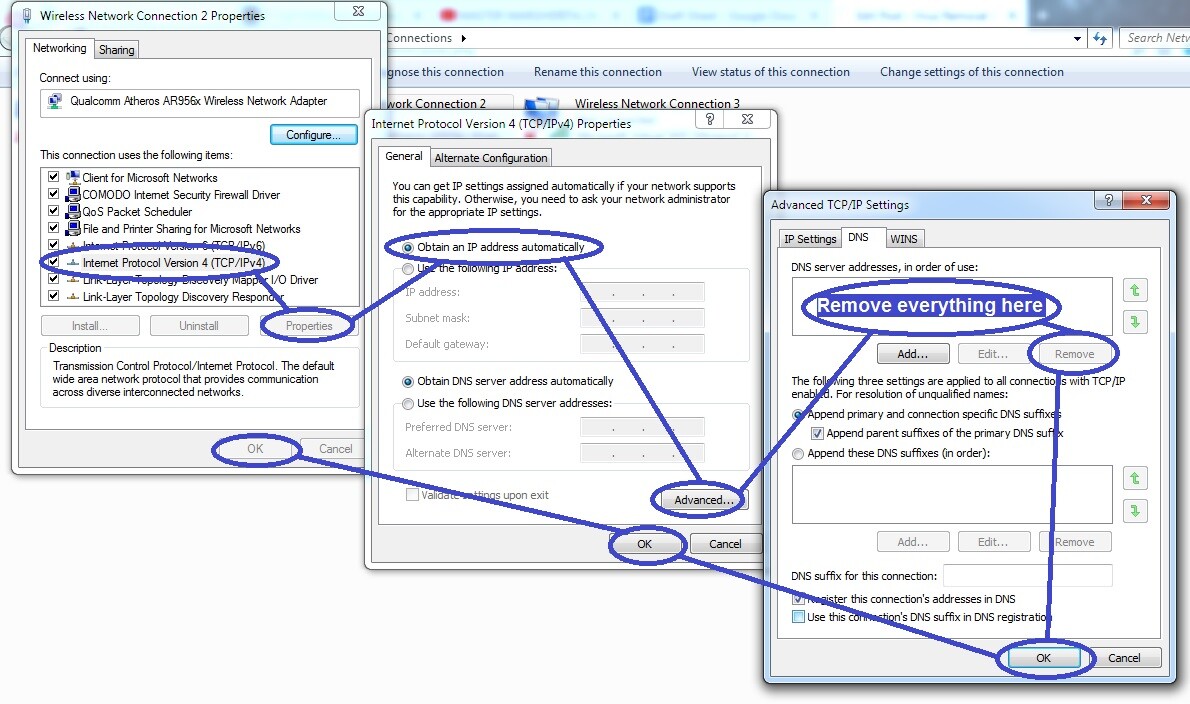
The third thing you must type in Run is ncpa.cpl. Go to it and when a window with the network connections you have used with that computer shows up, right-click on the one that you the PC is connected to at the moment. Then select the Properties option and in the next window, click on Internet Protocol Version 4 from the list.
Select Properties from that window and in the next one enable the Obtain an IP address automatically and the Obtain DNS server automatically settings if they are currently not selected. After this, you must open Advanced, check the DNS tab for any listed IPs and if such IPs are shown in the list, you must delete them and then save whatever changes you have made by clicking OK on everything.
Step 5
WARNING: This step requires making changes in the system Registry by finding malicious items and deleting them. It’s crucial that you do not delete anything else or this may destabilize the system and cause damage to it. To prevent this from happening, if you aren’t certain about an item, tell us about it in the comments instead of directly deleting it, and we will tell you what to do.
Start the Registry Editor from the Start Menu, by typing regedit, hitting Enter, and then clicking on Yes. Then evoke the search box of the Registry Editor by selecting Find from its Edit menu and when that shows up, type Entertainment.exe in it and initiate the search. If there are related items, the search will only show the first one of them – you must delete that one and search again to see if there are more and to delete them too.

One last thing you must do in the Registry Editor is find the directories listed below in the left panel of the Editor and search them for sub-folders with weird names that seem out of place among the rest. For instance, anything with an overly-long name that appears to be just a random sequence of letters and/or numbers should count as suspicious. Such items should be deleted, but it’s best to first tell us about them through the comments section so that we can confirm that you should indeed eliminate them.
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
Step 6
If the manual steps shown above didn’t help you delete the virus, then the best course of action is to try finding and deleting the virus with a removal tool that specializes in dealing with this sort of threats. One such tool that we strongly recommend to our readers can be found linked on this page – using it will allow you to find all malware data and delete it without risk for the system, and it will also enhance the computer’s protection so that no more Trojans or other malicious threats are able to successfully attack you.


Leave a Reply