*Source of claim SH can remove it.
F.txt
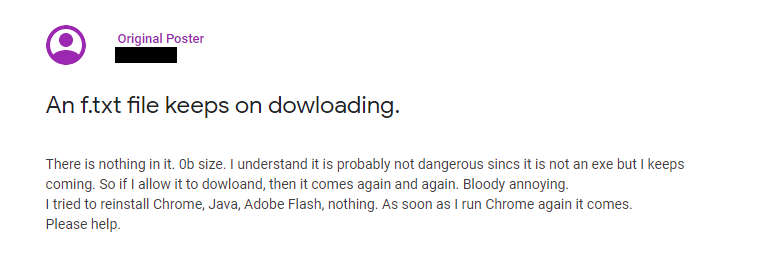
If your browser keeps wanting to download F.txt on your computer when you try to browse the web then this means that your system has been infected by a browser hijacker. F.txt does not pose any real danger, but it can lead to more serous malicious programs if it is not dealt with.
The positive news here is that the unwelcome adjustments and the irritating advertisements can be removed as soon as you uninstall the unwelcome program from your device. However, it can be quite challenging to uninstall a piece like f.txt if you have never dealt with this type of software before. Thus, in case you require some help, below we have published a free removal guide and a helpful removal tool for self-help.
The F.txt Download
The f.txt file being downloaded by your main browser all the time is a sign there is a browser hijacker application in your computer. In reality, browser hijackers such as f.txt are not as dangerous as many users may think.
A piece like f.txt, for instance, may replace the preferred search engine and may change the homepage URL with one of its own. The app may also start to cover every new tab that you open with various pay-per-click advertisements that redirect you to specific sponsored web locations.
The F.txt Virus
A browser hijacker such as F.txt is a program that is generally very different from a real piece of malware. Rather than seeking to harm your system, F.txt seeks to place aggressive online ads, pop-ups and banners on your screen. Thus, they often tend to attach to the system’s main web browser and mess with its settings.
You would still be able to open your browser if f.txt has happened to be mounted on it and connected to the internet, however, your web browsing activity may start to get interrupted by various web commercials.
Our guide is intended to support people who have installed f.txt on their machines and have failed to detect and successfully remove it from Chrome, Firefox, Edge and other commonly used web browsers. If you find the guidelines there too difficult to follow, though, or you simply are afraid not to delete something else by mistake, it is better to use the suggested professional removal tool that can scan your machine for f.txt and save you time and nerves in uninstalling the unwanted application.
Browser Hijackers should be treated with care
There is no need to be over concerned if you have detected a browser hijacker on your computer because such software doesn’t have the harmful abilities of a computer virus, a ransomware or a Trojan Horse. However, it is not a good idea to fully trust everything that the hijacker displays on your screen. .
When left to operate undisturbed, apps like f.txt may often take over the system’s default web browser and start an uncontrolled ads and websites promotional activity that may expose your system to danger. What we refer to here is that not all online advertising materials and pages are trustworthy and some may even redirect you to web locations where viruses and other malware may lurk.
Therefore, even if you decide that the discomfort of the constant advertisements streaming and the new browser components imposed by the browser hijacker can be managed, it is still a good idea to remove this software as prevention measure against exposure to random promotional web materials.
SUMMARY:
| Name | f.txt |
| Type | Browser Hijacker |
| Detection Tool |
*Source of claim SH can remove it.
F.txt Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Ah, thank goodness I stumbled upon this blog post! I recently downloaded a file called F.txt and now my computer is acting wonky. I was starting to freak out thinking it was a malware or virus, but now I see that it’s just a download removal guide. Thanks for sharing this helpful information, I’ll definitely follow the steps and remove that pesky file. ?