Fips Parcel
Fips Parcel is malware that can monitor your activities on the computer and send the obtained information to the hackers who control it. Fips Parcel can access password details, login credentials, and other confidential information that can later be used for criminal deeds.
A Trojan is generally a highly versatile computer virus that can have many different purposes which is why such threats are typically considered unpredictable. Besides, Trojans can be spread in a number of stealthy ways and can be used to complete a wide variety of illegal activities one after the other. These two are very important characteristics that need to be taken into account when dealing with those threats.
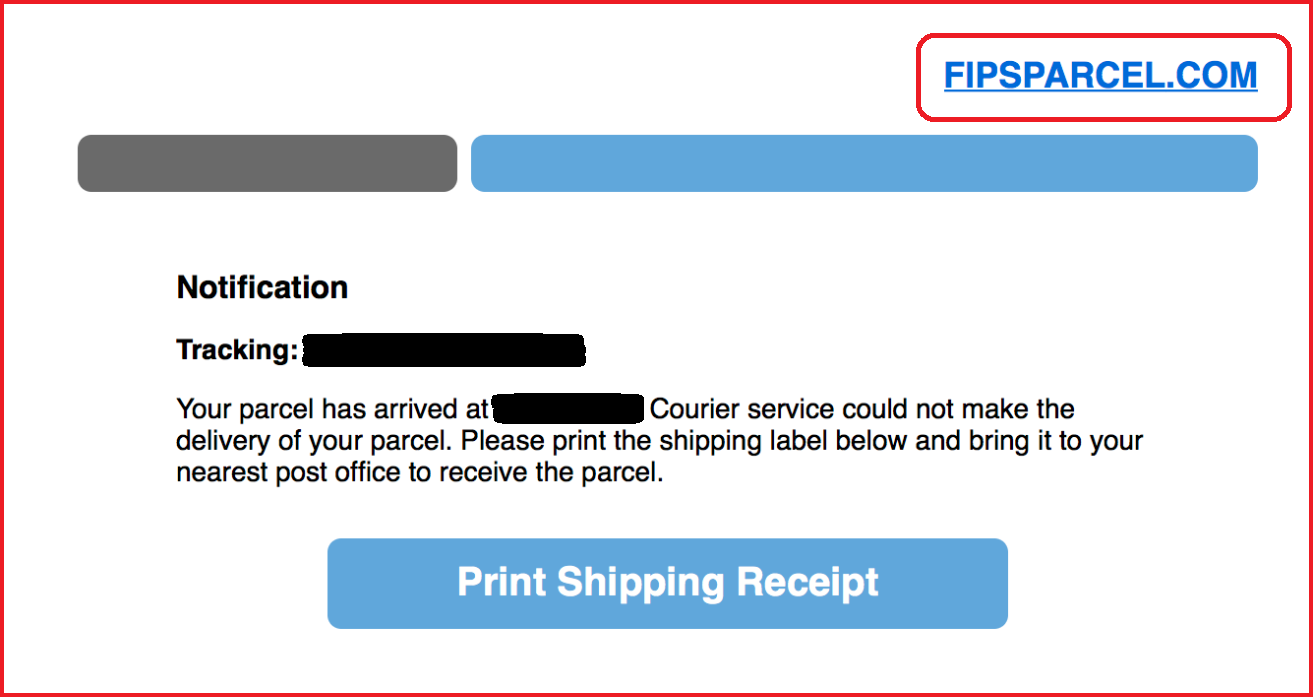
An infection like Fips Parcel, for instance, could be bundled with almost any type of web content – from torrents, to malicious spam emails, malvertisements, and illegal web sites, to all kind of spam messages, on-screen notifications and even fake security and software prompts. Whatever the delivery method is, the contamination typically occurs without any visible symptoms. This allows the malware to complete its malicious agenda without being disturbed and, sadly, this agenda could involve different illegal or highly destructive actions.
The Fips Parcel Virus
Most Trojans, including Fips Parcel, can be effectively used to destroy something stored on the infected computer or directly damage the device in such a way that only a system re-install may be able to repair it (sometimes not even that). The Trojan can target personal or work-related data and even some system files which may be essential for your machine’s normal functioning.
Another potential use may be for the so-called backdooring. In short, this function allows the Trojan to serve as a helper for other malware, such as Ransomware or Spyware, that allows the additional threats to enter the computer. In such a case, the Trojan’s goal is to scan your system and look for any existing weaknesses that could be exploited. A possible vulnerability, for instance, could be an outdated program. If such a weakness is found, your computer could be compromised by the Ransomware or Spyware without any visible symptoms that could indicate the infection.
The Fips Parcel Email
According to researchers, Fips Parcel is a virus of the Trojan Horse variety. Fips Parcel is distributed through malvertising, and other social engineering techniques, and could be used for banking theft, espionage, Ransomware distribution, and more.
Yet another possible aim of a Trojan like Fips Parcel may be to serve as a data extractor. Such malware can secretly collect details about your online bank accounts, your passwords, your social media accounts, and everything you type with your keyboard. The cyber scammers behind the infection can use this data to take advantage of your private information by making copies of it and using it to hack into your social media accounts, steal your identity or drain your bank accounts.
Fipsparcel
Fips Parcel is a malicious Trojan Horse that could corrupt your data and system, and exploit outdated software in order to download other viruses. Malware like Fips Parcel is oftentimes used for infecting more people with Ransomware.
Therefore, it is essential to remove the infection as soon as you detect it in order to prevent it from completing its job. The successful removal of a Trojan like Fips Parcel, however, could be rather challenging. That’s why our recommendation is use a detailed removal guide, such as the one below, and carefully follow its instructions. You may also need to use a specialized anti-malware tool or to update your existing antivirus program to deal with the threat effectively.
As far as prevention is concerned, make sure you never go to web sites that may be unreliable and that may contain questionable content. Stick to web locations you trust and keep away from spam, especially when it comes in emails with suspicious attachments or messages from unknown senders.
SUMMARY:
| Name | Fips Parcel |
| Type | Trojan |
| Detection Tool |
Remove Fips Parcel Virus
To remove the Fips Parcel virus from your Windows system, you need to find and uninstall any unwanted programs, stop the Trojan processes, and revoke any unwanted system changes made by the malware.
- First go to Programs and Features, look for suspicious and potentially unwanted programs, and uninstall what you find.
- Next, look for rogue processes in the Task Manager tool and quit the ones that may be linked to the virus.
- Thirdly, check the Hosts file, startup items, and system Registry for changes made by the Trojan and restore the default settings to remove the Fips Parcel virus.
- Finally, restart the whole system and see if the malware is gone. If you still see Trojan Horse symptoms, consider using a professional removal tool to resolve the problem.
The four steps shown above outline the Fips Parcel removal process but do not offer a detailed explanation of how to complete them. Therefore, if you need additional help with one or more of the steps, you can find a more in-depth explanation of how each of them should be completed in the advanced removal guide posted below.
Extended Guide
Some of the next steps will require a system restart, so, in order to not lose the current page, it may be a good idea to open it on another device and look at the instructions from there while you are performing the steps on your PC. Alternatively, you could bookmark the page in the browser to make finding it later easier.
Step 1
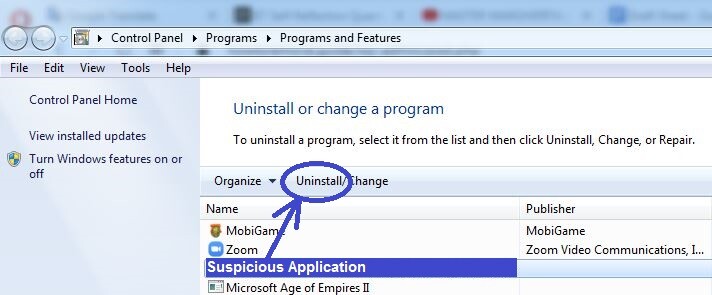
Type Programs and Features in the Start Menu and select the icon of the first result. The list of programs that you see on the newly-opened window shows all programs that are installed on your computer at the moment. Look for items that have been installed around the date you think the Trojan entered the computer. If you see programs installed at that time that you think are suspicious or that are unknown to you, it’s best to uninstall them from your computer.
In order to uninstall a suspicious program, select its entry from the list, then click the Uninstall button from the top, and follow the steps shown in the uninstallation manager. It is important to remember to make sure the uninstaller gets rid of everything, including personalized settings for the program you are trying to uninstall.
Once you finish the uninstallation of all programs, we suggest restarting the computer before continuing with the next steps.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
After the computer is restarted, go to the Task Manager by pressing together Ctrl, Shift, and Esc from your keyboard and click the tab labelled Processes, where you will see what processes are currently running on the computer. If you see entries with high CPU or RAM consumption that also seem to have unusual, unfamiliar, or suspicious names, use a reputable search engine (such as Google, Yahoo, or Bing) to try to find more information about them. In most cases, if the process in question is malicious, there will be lots of reports online addressing that fact.
If you find such reports during your research, especially if they are from reputable and trusted sources, right-click the process in the Task Manager, open the File Location folder, and scan the files there with the online scanner shown below. The tool is free and can be used directly from the browser without need for installation.


If a malicious file is discovered in the process file location folder, return to the process in the Task Manager, right-click its entry again, and click on the End Process option.
After you quit the process, delete the entire file location where its files are contained. It is possible that you won’t be allowed to delete that folder – if this is turns out to be the case, then delete whatever files you can from inside the file location folder and finish the rest of the guide. Once all other steps have been completed, you should be able to finally delete the file location folder in its entirety so return to it and try to delete it once again.
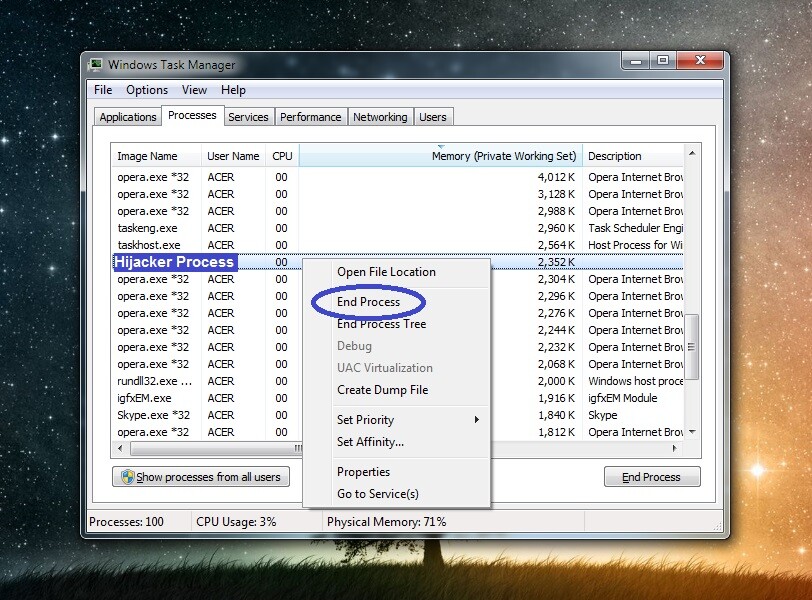
Important!: Even if no files are detected as malicious in the file location folder of the suspected process, if the information that you found online about that process seems reliable and reports that the process is linked to the malware, we still suggest quitting the process and deleting its folder.
Step 3
To make sure that no Fips Parcel processes are allowed to run in the system, (in case you didn’t manage to identify and quit all of them during the previous step), we suggest booting your PC into Safe Mode using the instructions from the linked page.
Step 4
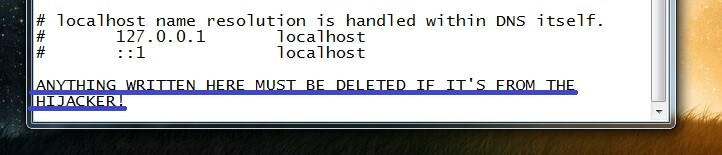
Evoke the Run window by pressing together Winkey and R and then type (or copy-paste) the following file location in the search field:
- notepad %windir%/system32/Drivers/etc/hosts
Click on OK or press Enter – you will be taken to a system notepad file named Hosts. In that file, you must check the bottom of the text and see if there are suspicious IP addresses listed there. Usually, anything written below “Localhost” counts as suspicious, but it is possible that legitimate third-party programs, and not malware, have made changes to the file. Therefore, you should send us any IPs you find at the bottom of the Hosts file and once we have a look at them, we will be able to tell you if they are malware-related. In case they are indeed from the Trojan, the IPs will have to be deleted from the Hosts file and then the changes to the file must be saved.
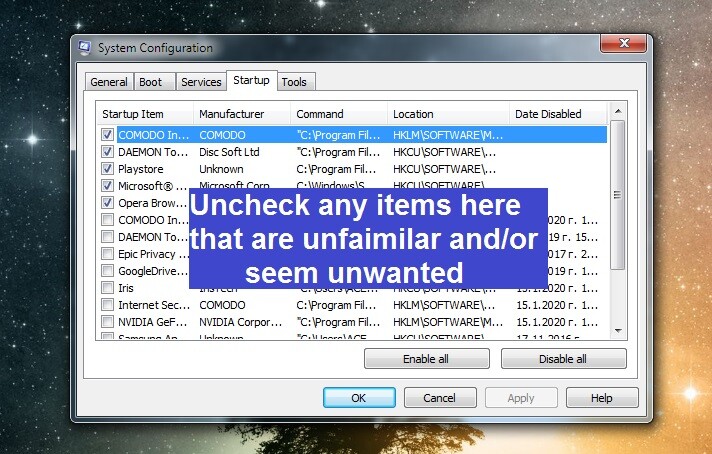
Once the Hosts file is taken care of, you need to return to Run, type msconfig in it, click OK, and then open the Startup tab in the System Configuration window.
There, look at the listed items and try to determine if any of them are not supposed to be there. The items in that list are apps and features that are launched automatically, without user interaction, when Windows loads.
If you see an item that you think is suspicious, related to the malware, or simply unneeded, remove the tick from the checkbox in front of it. Once you do this with all potentially unwanted items, click OK to apply and save the changes.
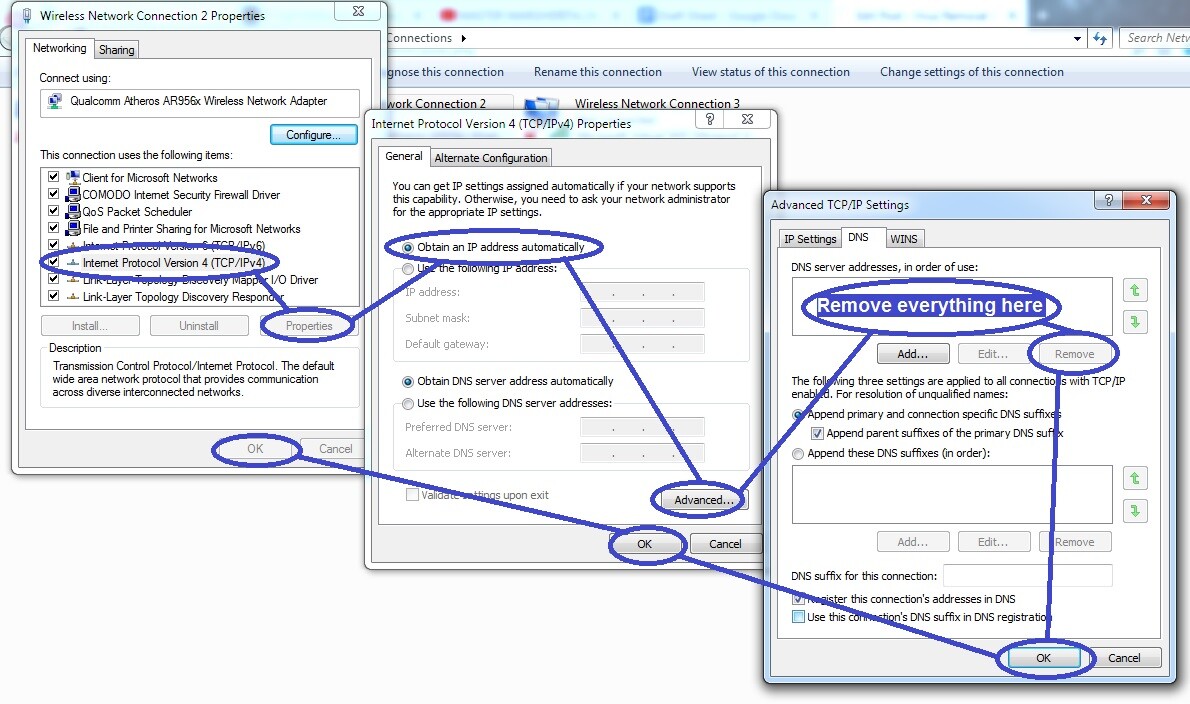
Open Run for a third time, type ncpa.cpl in it, click OK, and select with the right-click of your mouse the icon of the network that your PC is connected to at the moment. Go to the network’s Properties, and find and select an item labelled Internet Protocol Version 4 (TCP/IPv4). Next, click the next Properties button and check the Obtain an IP address automatically setting in the next window (if this option isn’t already checked). After you do that, go to the Advanced settings, open the second tab (DNS), and delete any IP addresses that may be shown in the list there.
After everything thus far is done, click OK on everything so that any changes you’ve made would be saved.
Step 5
Important!: To avoid further complications for your system, be sure to complete this step very carefully. Delete only the items you are certain are unwanted while completing the step. In case of uncertainty about a certain item (or items), contact us through the comments to ask us about said item(s) and wait for our reply before you decide whether to proceed with the deletion.
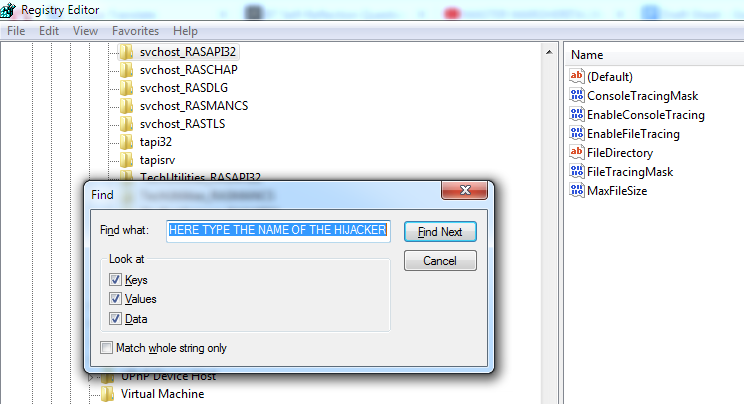
Go to the Registry Editor of your PC by typing regedit.exe in the Start Menu and pressing Enter. When a dialogue box appears on your screen asking for your permission, click Yes.
When the Registry Editor starts, click the Edit menu from the top, type Fips Parcel in it, and click the Find Next button. This will search for related items in the Registry Editor and show you the first found item. If an item does get found, delete it, perform another search, delete the next thing, and keep doing this until no Fips Parcel results are left in the Registry.
Next, manually find the following three Registry locations in the left panel of the Registry Editor window:
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
When you find each of them, carefully look at their sub-folders, looking for items that have unusual names – for instance, names that seem way too long compared to those of the other folders and/or ones that are composed of seemingly random sequences of letters and numbers.
If you find any such entries in those three Registry locations, delete them. If, however, you are uncertain they need to be deleted, remember to request our aid through the comments section.
Step 6
If nothing thus far seems to be helping, and you still think Fips Parcel is present on the computer, it is strongly recommended that you try using a specialized removal app to take care of the problem for you. In many cases, Trojans like Fips Parcel are able to deeply infiltrate the system making it very tricky to manually find and delete all malware data and settings. Therefore, we if you are still struggling with this malware even after you’ve done everything from this guide, we recommend that you try out the professional security tool posted here – it is a program that has been tested numerous times against viruses like Fips Parcel and will help you with the elimination of the threat as well as keep your system safe against future malware attacks.

Leave a Comment