What is the Format Virus?
A new wave of Ransomware cryptoviruses (Ndarod, Access) has recently been unleashed upon the Internet and the victims of these infections grow in number with each passing day. If you are here because the files in your computer have become inaccessible after a cryptovirus named Format has placed its encryption on them, be sure to read the information from the current article in order to learn what you can do to liberate your computer from the presence of this threat and potentially recover some of the encrypted data without giving in to the hackers’ ransom demands.
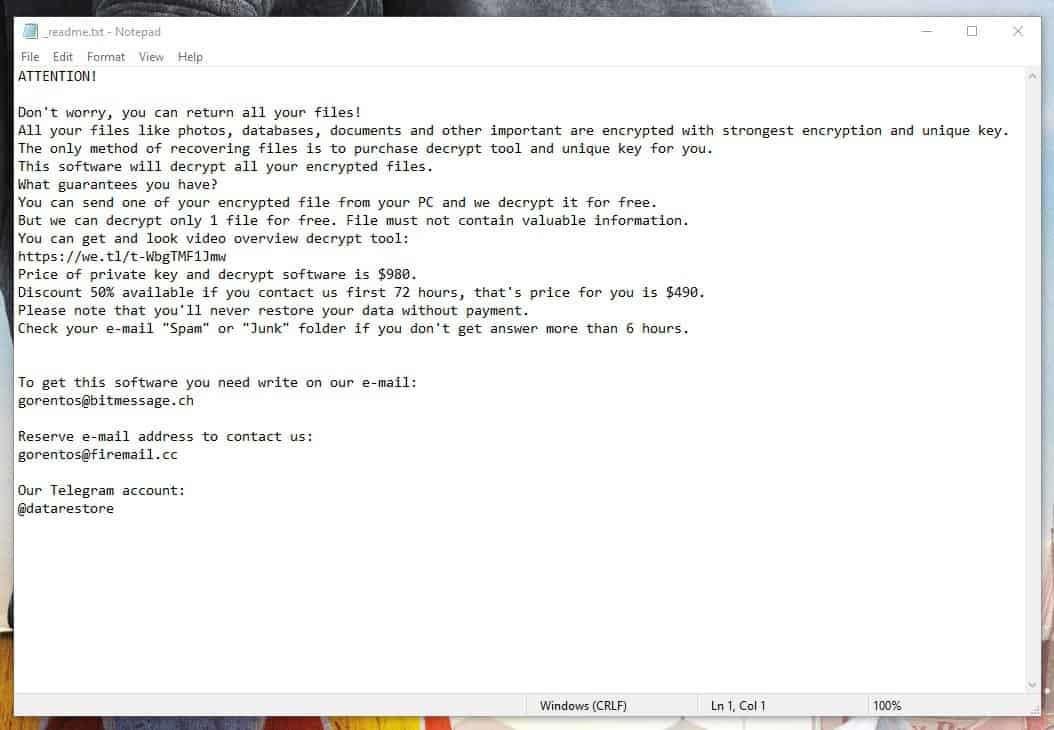
Speaking of ransom, you have probably noticed a banner message or a notepad file on your desktop after Format encrypted your files. This is the ransom-note that the virus generates in order to inform you about the steps you’d need to take in order to pay the ransom demanded by the hackers and (supposedly) receiver a decryption key in return for your money. This is pretty much how all Ransomware cryptovirus infections operate – they enter the computer in stealth and silence and begin to lock up the files without anybody noticing their malicious activity. Before the user knows it, the data in their machine is inaccessible and they are being blackmailed for the decryption key for the locked files that can make them accessible again.
Now, here is probably the place where we must give you our thoughts with regards to how viable of an option the ransom payment is. Typically, most security specialists say that paying the hackers is not a very good idea as it makes you risk your money without having any guarantee that you will get to open your files again even after you pay. We fully agree with this – there is simply no way of knowing whether or not the criminals behind Format would indeed send you the unique access key for your files or if they would instead take your money without helping you decrypt your data. Another possibility is if they send you some key but that key doesn’t work – there have been many examples of this happening and, of course, the users who experience it do not get their money refunded by the criminals. All things considered, the ransom payment option should really be seen as your last resort course of action and you should only consider going for it of nothing else seems to help and if the files that have gotten locked are really that important to you.
What you can do as an alternative to the .format files
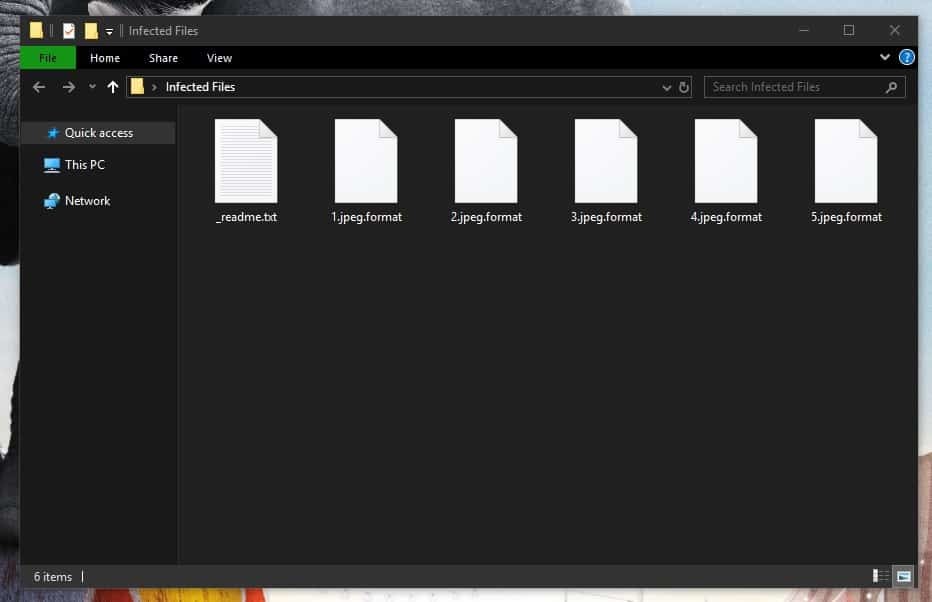
Our advice for you if you are struggling with the encryption from .format is the following – try out the guide from this page as it will help you with the removal of the infection. After the Ransomware is gone, try the suggested file-recovery options – they may not always work but they are still something you can try for free that may allow you to restore some of your locked data. Also, do not forget to check your other devices and cloud storages for any safe copies of your files – any backups that you may have, now would be the time to use them.
SUMMARY:
Format Ransomware Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply