This page aims to help you remove the Hacker Team Virus. Our removal instructions work for every version of Windows.
Hacker Team
The Email sent out by the Hacker Team can infect your system and allow cyber criminals to see and record sensitive information that is found on the computer. The Hacker Team Email may provide the hackers with full remote access to a machine and let them modify, corrupt, or delete user files.
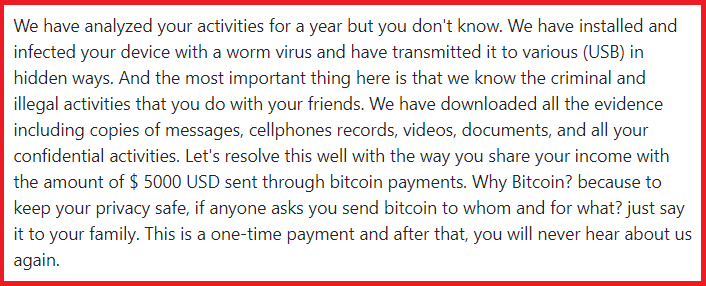
This is an example message sent by the Hacker Team.
Trojan Horse viruses are likely the worst type of malware out there. They are stealthy and can perform a whole variety of harmful and criminal deeds. Hacker Team is one of the latest additions to this class of malicious software and we have recently received a number of reports from users like you about this particular Trojan Horse. A key characteristic of Hacker Team is its ability to hide inside the computer over long periods of time and stay unnoticed while running various damaging processes in the background of the system.
Your system devices has been hacked
“Your system devices has been hacked” Email is a Trojan Horse capable of secretly monitoring the user’s activities as well as remotely controlling some aspects of the computer. The presence of “Your system devices has been hacked” Email in the system can also lead to loss or corruption of digital data and system records.
Our users reported a Bitcoin email scam that they have received, with the following message from the Hacker Team:
“【 Reminder 】 Your system devices has been Hacked 【 National Security Agency 】 Authority ****** Immediate action required: Your activity has been recorded. We have analyzed your activities for a year but you don’t know. We have installed and infected your device with a worm virus and have transmitted it to various (USB) in hidden ways. And the most important thing here is that we know the criminal and illegal activities that you do with your friends. We have downloaded all the evidence including copies of messages, cellphones records, videos, documents, and all your confidential activities. Let’s resolve this well with the way you share your income with the amount of $ 5000 USD sent through bitcoin payments. Why Bitcoin? because to keep your privacy safe, if anyone asks you send bitcoin to whom and for what? just say it to your family. This is a one-time payment and after that, you will never hear about us again.”
Therefore, the most pressing thing now is to detect and remove the infection from your machine before it can do more harm than it already has. For this purpose we have prepared a manual removal guide that you can find just below this post. For more professional assistance, you can also use the automatic removal tool from the guide which can scan the entire computer and safely remove Hacker Team without you having to manually tinker with important system files.
The Hacker Team Email
Some users have received emails from the Hacker Team who claim that your computer is infected by a virus of theirs and they have control over your system. The emails sent out by the Hacker Team are made to scare you into thinking your computer is infected
In one way or another, we’ve all heard of the Trojan Horse viruses, but not everyone knows what they can really do. In fact, there is no brief answer to this question. This type of malware is so versatile that it can be programmed to perform different malicious actions while on your computer and they all depend on the intentions of the hackers who are in control.
For example, a Trojan can be used to steal your computer’s data. If the hackers want to obtain specific digital files and confidential records, they can set the malware to target specific types of files and send them to remote servers. If the hackers want to gain access to your online accounts, passwords, or online banking details, they can set the Trojan to keep track of your keystrokes and record everything you type in with your keyboard.
The [email protected] Email
Users have been receiving scam emails from [email protected] and that your computer has been infected with viruses. Such [email protected] Email should not be trusted or replied, they are designed to trick the users into sending ransom money for deleting compromising files which actually do not exist.
An advanced infection like Hacker Team can also share yours screen with hackers and let them hack into your mic and webcam. In this way, the offenders can learn your location, stalk you, record your communications, and use the collected information for all kinds of criminal deeds. Furthermore, such a Trojan can turn your machine into a bot and exploit its resources to spread spam and malware. Besides, a threat like Hacker Team can act as a backdoor for another type of dreadful infections known as Ransomware. That’s why, if you’ve been infected with Hacker Team, apart from having it removed right away, it would be smart to scan your machine for other viruses as well.
If you don’t have an antivirus program on your computer, or your existing security program is unable to detect and remove Hacker Team effectively, we encourage you to use the professional removal tool fro this page. This is a powerful anti-malware tool that can deal with the Trojan automatically and will surely save you time and effort.
SUMMARY:
| Name | Hacker Team |
| Type | Trojan |
| Detection Tool |
Hacker Team Email Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment