[email protected]
[email protected] is a ransomware cryptovirus that is primarily distributed through spam, fake ads, malicious email attachments and cracked software. [email protected]’s criminal creators are using the software to encrypt user files and to request a ransom from the victims who wish to decrypt them.
[email protected] is placed in a .txt file in order to contact the group of hackers responsible for the encryption of your files.
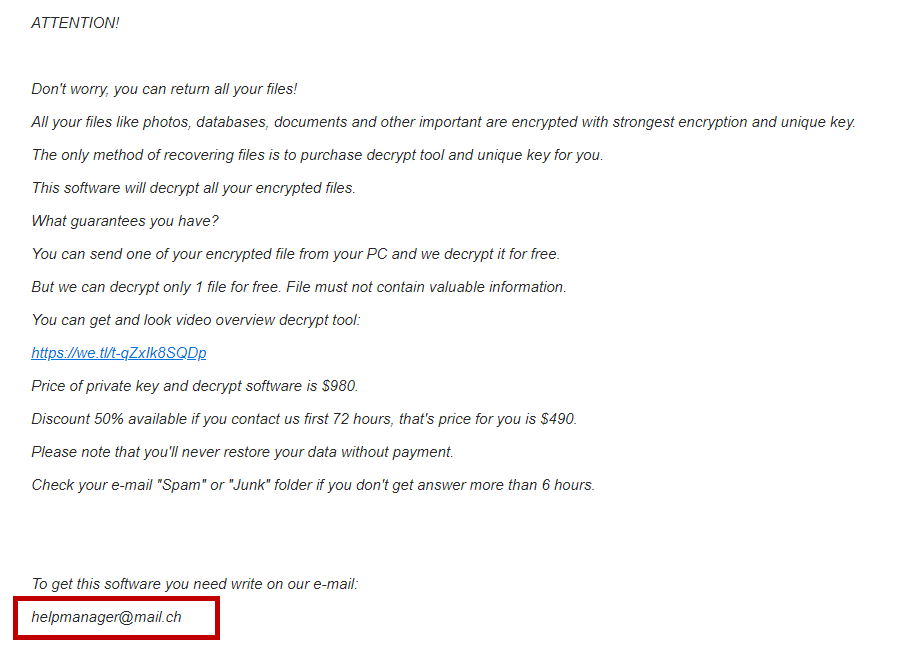
A scary ransom notification published on the screen of the infected computer announces the attack of this ransomware. This message normally contains ransom payment instructions and a kind of ultimatum from the hackers who threatened that that they will not provide the decryption key for the encrypted data, if no money is sent to their cryptocurrency wallet within a specified period. However, this ultimatum is mostly intended to frighten the victims so they pay the ransom money without having time to look for alternatives.
In reality, people infected with [email protected] or [email protected] may seek to get their files back free of charge, and even remove the ransomware cryptovirus from their computer. The removal guide on this page contains instructions that explain how to locate the infection, as well as some free suggestions on how to recover your encrypted files. Everybody who wants to test them should do so before even thinking of transferring money to the hackers behind the virus. We must, of course, inform you that there is no guarantee that the proposed methods of recovery will be effective in each case. Nevertheless, the ransom payment also cannot ensure that you will get the decryption key from the crooks. This is why the recovery is never certain and the ransomware threats are considered to be one of the web’s most malicious pieces.
The [email protected] virus
The [email protected] virus is a piece of malware that encrypts computer files without the users’ consent. The [email protected] virus targets commonly used digital files and places encryption to them so that they become inaccessible without a decryption key.
You could lose valuable information due to the attack of [email protected], especially if you don’t keep regular backup copies of your files. In fact, the malware modifies the encrypted file names and their extension, so that no application can recognize or read them.
Yet what’s worse than that is that the file encryption process that runs in the background of the system may be invisible for most antivirus applications. This ensures that the victims of the ransomware are unable to detect and stop the virus on time. So, after the encryption has been applied to their files, they have to confront the ransom-demanding message.
The [email protected] file encryption
The [email protected] file encryption is a secret process that converts digital files into unreadable data pieces. Usually, the [email protected] file encryption runs free of visible symptoms which is why most people cannot stop it until it’s too late.
Significant data loss due to the attack of ransomware like [email protected] can be best avoided if users periodically create backup copies of their files and save them on an external hard disk, cloud storage or another device that is not linked to a network or the current computer. In this way, they can access their data anytime and, even if they get attacked by a ransomware representative, they only will have to remove the virus and use their copies to recover the encrypted information without paying a ransom to anyone.
SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Detection Tool |
Remove [email protected] Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment