www.Helpme.net
The online world is full of scammers that seek to make quick profit on the backs of users who aren’t careful or experienced enough to recognize the scam’s scheme. In the following lines, we will give you information regarding one particular Internet scam model that uses a legitimate and legal site called Helpme.net.
The scammers ask you to provide access to the computer using helpme.net so that they can fix your computer.
Down below, we will give you an overall idea about how the scam works in most cases so that you know how to avoid it in future. Generally, there three distinct phases/stages that this scam model needs to go through in order to be successful. The earlier you notice that there’s something fishy, the lesser the chance of you becoming yet another victim to this fraudulent scheme.
Phase 1 – contacting the user
The Helpme.net scammers first need to establish some form of contact with their potential victim. This can happen in a number of ways. For instance, some users have reported being deceived by a pop-up message to make a call to a person who had claimed to be a representative of Microsoft or of some other major company. The supposed tech operator would typically tell the user that there’s some issue with their PC (security vulnerabilities, malware infection, outdated software, etc.) that need to be taken care of and that the only way for this to happen is to follow the instructions that are given to the user. In other cases, the victim is forced to call a provided phone number (the number of the scammers) because their PC has gotten blocked due to expired Windows license or due to some other legitimately-looking reason. In such a case, a number is given to the user and once they call that number, they’d be in contact with the crooks that are pretending to be tech-support operators that can help with the removal of whatever is blocking their device.
Phase 2 – the Helpme.net website
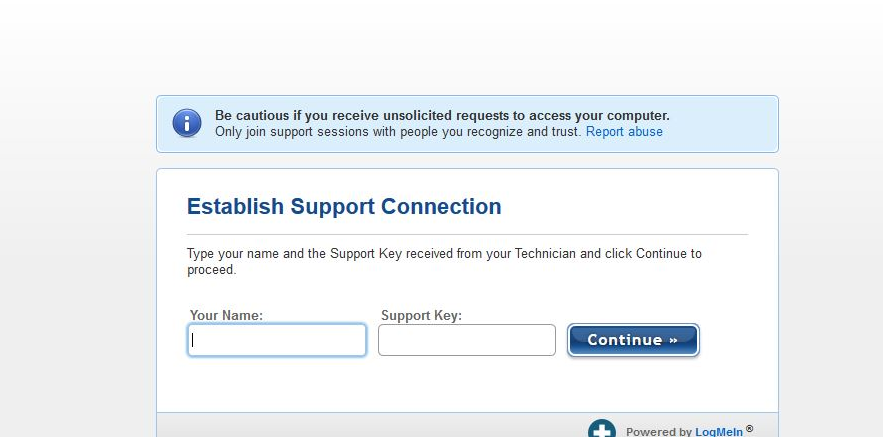
Once in contact with the scammer, the user is told to visit the Helpme.net website where they are greeted with two blank text boxes – one for the user’s name and one for a code that the user receives from the hacker. Once the request is filed, the user downloads a software tool called GoToAssist.exe. The purpose of this tool is to provide the scammer with remote access to the user’s PC allowing the online crooks to proceed with the next phase of their scheme.
Note that the Helpme.net site is actually a legitimate one and so is the GoToAssist.exe program. However, many web-scammers have found a way to exploit this online service and extort money from users by utilizing it.
Phase 3 – Remote access
Once the user downloads GoToAssist.exe from the Helpme.net site and runs it, they are prompted with a request. If they agree to the request, the crooks would gain remote access to the targeted PC similarly to how the well-known Team Viewer tool works. Once the remote access has been established, there are different things that the crook might try to do depending on the specific case. For instance they might run a scan with some fake malware-detector and tell you that they have found viruses on your machine and later tell you that you need to buy a license to some antivirus program that you’ve never heard about in order to eliminate the non-existent threat. In other cases, they might simple put a new password on your machine and ask you to pay them money if you want to be able to regain access to your machine. There are other possibilities as well but you get the idea. In most cases, such scammers do not seek to steal sensitive information such as banking account credentials, yet this is still within the realm of possibility.
If you get to this phase of the Helpme.net scam, you might still avoid further issues if you immediately block the remote access by closing the GoToAssist.exe program and then conducting a full system scan for any unwanted software that might have gotten inside your PC. Note that in case you initially received some sort of warning or if your PC got blocked by some odd message (as described in Phase 1), it is likely that you have recently downloaded some unwanted piece of software that has set in motion the whole scam scheme that we’ve just described. Therefore, it is a good idea to thoroughly check your PC for any sketchy programs and applications and the suggested anti-malware tool on this page can help you do that so give it a try if you want to.
Future safety
Always use your common sense when browsing the online world and never make any rash decisions out of frustration or panic as this is what such cyber-scammers typically rely on. Most of the components used in the Helpme.net scam model we’ve just described are actually legitimate so sometimes it might not be possible to detect the scam via antivirus programs. That’s why, you must always above all rely on your vigilance and attention if you want to keep your system, your virtual identity and your money safe.
SUMMARY:
| Name | Helpme.net |
| Type | PUP |
| Detection Tool |
Helpme.net Scam Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

I am able to access google from my Android phone, but not able to access my account from either of my HP laptops. I know my username/password. Is this potentially due to malware?
Hi Tricia,
do you encounter any form of pop ups or window redirection? Or in any case if you think you might be exposed to some kind of virus, i recommend you to download SpyHunter from this page. It has a free scanner and it will surely help you if you have any doubts.