Hets
The Hets Ransomware virus is a specific type of malware, specialized in encrypting digital data and keeping it hostage for a ransom. The Hets virus targets different types of data, including work-related and personal files, databases, archives, and system records, and encrypts it using a military-grade encryption algorithm.
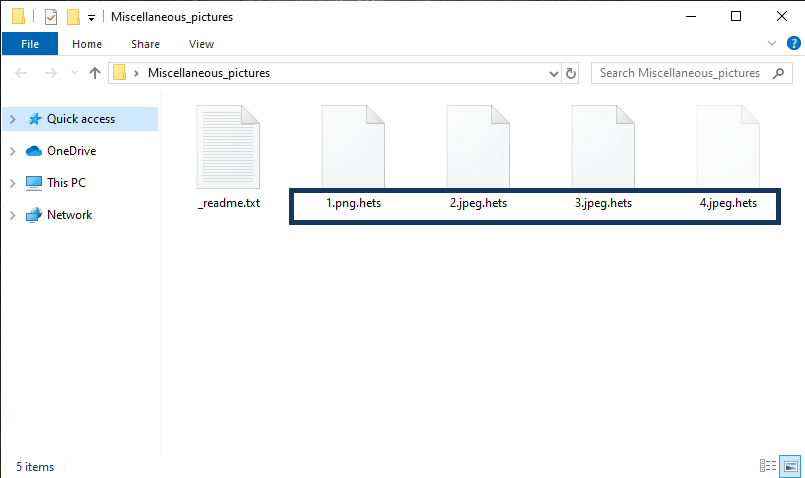
The Hets Ransomware will start encrypting your files the moment after infiltrating your system.
Hets is one of the nastiest types of malware that a web user might have to deal with. According to experts, this Ransomware can be classified as a cryptovirus which is one of the hardest forms of malware to remove. That’s why, on this page, we will discuss its characteristics and the possible solutions to its attack. With the constantly growing number of infected computers, Hets could possibly be an even greater threat than the other malicious software types and you probably are not the only one that has been infected by such a virus.
The Hets virus
The Hets virus is a Ransomware program that is created to extort money from you by encrypting your files and offering you the private decryption key in exchange for a ransom. The Hets virus generates an on-screen notification that contains instructions on how to make the payment and obtain the key.
Ransomware, in general, is one of the most unpleasant and fearsome types of malware programs in existence. The representatives of this category usually get distributed around the web with the help of different infected transmitters. Typically, a threat like Hets can infect your computer when you click on a suspicious hyperlink or download an infected attachment. However, it is not excluded that the Ransomware would be bundled inside some legitimate-looking file, offer, random pop-up or web link, which, once clicked on, can automatically deliver the infection into your system.
Regardless of the way you’ve caught the malware, once inside the system, it follows a specific agenda. Firstly, Hets infiltrates your machine and seeks particular file types. Then, once it finds the files, it encrypts them with a complex code that can only be decrypted with a private decryption key. At the end of the attack, it makes a ransom demand that you must pay to receive the access key. The whole process typically goes unnoticed. However, sometimes, especially on older and less powerful computers, the file encryption can take a significant amount of time and consume a lot of system resources. This is when you may have the chance to potentially detect the Ransomware inside your Task Manager. Ideally, there should be a questionable program process with an unknown name that uses the largest amount of RAM and CPU. Nevertheless, in most cases, the infection is only revealed after the encryption process has finished and the ransom notification has appeared.
The Hets file
The Hets file is a file encoded by the Hets Ransomware. The Hets file will remain inaccessible and will return an error message every time you try to open it until you apply the matching decryption key.
You may be in serious trouble because the hackers may never restore access to your personal files irrespective of whether you pay the ransom or not. Of course, if you’ve decided to transfer the money with the hope that the hackers will send you the decryption key for your files, this is a personal choice. The only advice we can give you is to first give a try to some free alternatives. Of course, we can’t guarantee that any other instructions will enable you to reverse the damage that Hets has caused. However, there’s also no reason to believe that giving your money to some anonymous criminals will magically fix everything. In many cases, this only inspire the cooks to continue their illegal activities and extort more money from you and other people. At the same time, if the Ransomware is not removed, it may keep encrypting every file you manage to recover, including the ones that could potentially be recovered with a decryption key.
SUMMARY:
| Name | Hets |
| Type | Ransomware |
| Detection Tool |
Remove Hets Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

My laptop file are encrypted by .hets how recover my all files please help
All steps done now what is the process to convet the data in original formate
Plz hello me I am Watting I loss my hill data I have some imp data plz
Help.me the solution
You can find file-recovery suggestions in our “How to Decrypt Ransomware” article.