*Hhuy is a variant of Stop/DJVU. Source of claim SH can remove it.
The Hhuy File
The Hhuy file is a piece of malware from the Ransomware family, similar to Hhaz and Nbwr, that likes to cause trouble by encrypting user data and keeping it hostage for a ransom. The creators of this threat use fake emails to spread it around, making the emails look real and friendly. But, guess what? If you open that email, you might get a nasty surprise. The same is valid if you love downloading files and software from unfamiliar websites or can’t resist those catchy pop-up ads, so be cautious. Those might be tricks to get the Hhuy file on your computer. If you have already been infected, stay with us to find out how to remove the ransomware and restore your files.
How to decrypt Hhuy ransomware files?
Decrypting files encoded by the Hhuy ransomware is a formidable challenge because the various strains of ransomware utilize distinct encryption methods, and some employ exceptionally robust codes that are very hard to decrypt. There may be tools that may assist in unlocking these files. Nevertheless, it’s imperative to recognize that the effectiveness of such tools is not guaranteed. Opting to pay the ransom, however, carries other substantial risks. There’s no guarantee of file recovery, and it inadvertently sustains the illicit activities of cybercriminals.
How to remove Hhuy ransomware virus and restore the files?
The Hhuy ransomware can be removed by using dedicated computer programs or by engaging cybersecurity experts for assistance. However, it’s important to be aware that, even after the malicious software is successfully removed, your files might still remain inaccessible due to encryption. Hence, when facing this malware, it is recommended to seek guidance from cybersecurity professionals or available manual removal and file-recovery solutions. However, it’s essential to prepare for the potential outcome where complete file access restoration may not be attainable.
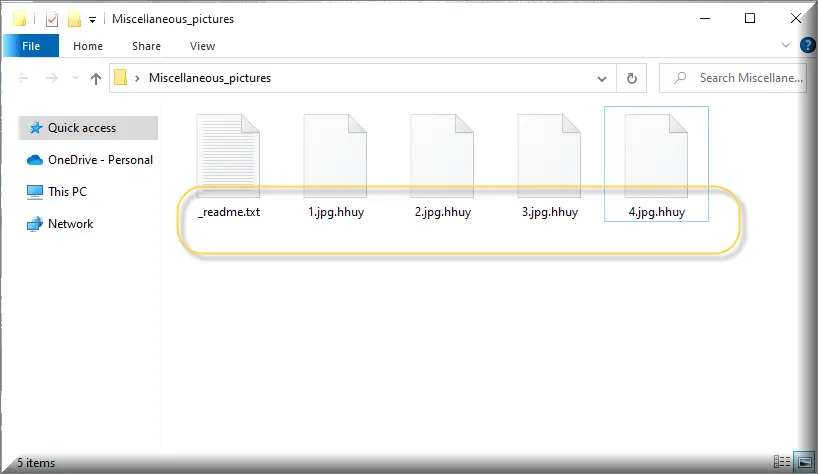
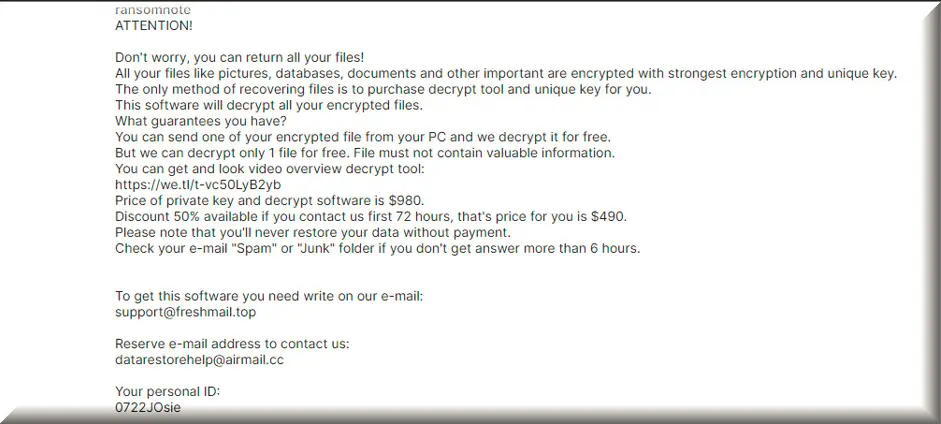
The Hhuy virus
Have your files turned unrecognizable overnight? When the Hhuy virus sneaks in, it holds your data hostage, usually encrypting it, so you can’t access it. Odd extensions might appear on your files, replacing familiar ones. And then there’s the undeniable sign: the digital ransom note. Whether it’s a pop-up or a text file dumped on your desktop, it screams demands—usually a payment in exchange for your file’s freedom. Speeding computer processes may also slow down, as the sneaky Hhuy virus gobbles up resources. If you can’t access familiar programs or documents and a mysterious message is demanding payment, this ransomware could very well be the culprit.
Hhuy
Determining the impact of the Hhuy attack is important if you want to deal with the ransomware quickly and effectively. Check for files that have unfamiliar extensions; these are likely the ones held hostage. Delve into your system’s logs, which can chronicle the ransomware’s journey and highlight other potential compromised areas. A complete system scan, using the latest antivirus definitions, will further clarify the situation. In addition to these steps, consider using the removal guide below or reaching out to law enforcement agencies or cybersecurity experts to report the incident and seek professional guidance on mitigating the effects of the Hhuy ransomware attack. Their expertise can be valuable in understanding the full extent of the breach and creating an effective response strategy.
.Hhuy
Paying a ransom to regain access to your .Hhuy encrypted files is fraught with uncertainties. The cybercriminals who deployed the ransomware on your computer are not bound by any code of ethics, and there’s no assurance that they will provide the .Hhuy decryption key even if you comply with their demands. Furthermore, paying the ransom fuels criminal activities, enabling cybercriminals to target more victims. It’s also worth noting that some countries have made ransom payments illegal due to their association with criminal organizations. Given these risks, it is strongly advised to explore alternative solutions, such as consulting with cybersecurity experts or law enforcement agencies, before considering ransom payment.
Hhuy Extension
Even though the Hhuy extension that is attached to your files is tricky to remove, you can deal with it without resorting to ransom payments. Paying cybercriminals is risky, and there’s no guarantee you’ll regain access to your files. So, it is much smarter to remove the Hhuy ransomware by running a comprehensive scan using reputable antivirus or antimalware software. Remember that this process eliminates the malware, but doesn’t automatically decrypt your Hhuy extension files. You can recover your files from backups, if available, or search for decryption tools designed for the specific ransomware variant you’re dealing with. Seeking assistance from cybersecurity professionals is also a viable option.
Hhuy Ransomware
Protecting your computer or network from future Hhuy ransomware attacks is vital and is not as complex as you may think. All you should do is create routine backups of your crucial data and store them securely. This enables you to recover files without paying ransoms. Also, keep your operating system and software applications updated to address potential security holes that the Hhuy ransomware can exploit. Be cautious when opening email attachments or clicking on links, especially from unknown sources, and consider using email filtering tools to block malicious content. By adopting these basic measures, you can significantly diminish the likelihood of succumbing to ransomware attacks in the future.
What is Hhuy File?
The Hhuy file could represent a beloved photo, an essential document, or even an archive – essentially, a file type commonly found on your system. However, the main difference lies in its encryption, making it utterly inaccessible. While the road to recovering your encrypted file after a ransomware attack may seem steep, it’s by no means insurmountable. Several backup solutions can be your savior. For instance, if you’ve diligently stored your critical files on a personal external hard drive, you can retrieve a recovery copy of that Hhuy file from it. Alternatively, offline storage options, such as DVDs, Blu-ray discs, or trusty USB drives can also be sources of valuable unencrypted file copies.
SUMMARY:
| Name | Hhuy |
| Type | Ransomware |
| Detection Tool |
*Hhuy is a variant of Stop/DJVU. Source of claim SH can remove it.
Hhuy Ransomware Removal

To prevent Hhuy from starting any malicious processes, your computer must be in Safe Mode for the rest of this guide. To reboot in Safe Mode, please follow the instructions from the link and after that, get back to this page.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Hhuy is a variant of Stop/DJVU. Source of claim SH can remove it.
Using the Task Manager, you need to end all Ransomware processes and remove their associated folders. To do that, use the Ctrl + Shift + Esc keyboard shortcut and go to Processes. Look for processes with strange names or processes that consume an excessive amount of CPU and Memory when launched. If any of these entries look questionable, do a Google search to see if there are any complaints of them being a danger. Next, right-click and access the folders for those processes (Open File Location).

Use the free scanner we’ve provided below to scan all files in those directories. It is important that a process be terminated if one or more of the files in its folder are deemed to be harmful by a scanner.

If the scanner detects malicious files in the processes, go to the Task Manager, right-click on the related process, then press End Process. After that, remove the files associated with that process from the system.

Use the Start Key and R key combination to open a Run box on the screen. In it, copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
This will open the Hosts file in Notepad. Look under Localhost to see whether there are any suspicious IPs mentioned below. If you find anything disturbing, copy them all and post them in the comments section. In the event that we detect a danger, we will tell you what to do.

After that, enter msconfig in the Start Menu search field, press Enter to open the System Configuration window, and check out which startup items are enabled on your system.

Look through the startup entries and deactivate the ones you aren’t familiar with and/or those that appear to be untrustworthy, then click OK to finish the process.

*Hhuy is a variant of Stop/DJVU. Source of claim SH can remove it.
Open the regedit.exe app by typing its name into the Start Menu search field. To open the program, Windows will ask for your permission. Click Yes to continue.
Afterwards, click Edit at the top of the Registry Editor window to begin searching for entries associated with the Ransomware, then click Find, type Hhuy in the search field that appears, and click Find Next again to continue searching. The detected item should be deleted. If the search returns other Hhuy-related items in the results, they should also be carefully removed. You may need to repeat the search until you have removed all traces of Hhuy from your system.
In the Start Menu search field, type “Folder Explorer Options” then enter the Folder Options settings and select the View option. Make sure the Show hidden files, folders and drives option is enabled by checking the checkbox.
Then, in the Start Menu search field, type each of the following locations below and press Enter.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
The files in the newly opened folders may then be sorted according to the date they were created. Remove anything that has been added around the time the Ransomware infection occurred. Also, select everything in the Temp folder and delete it to remove any temporary files from the system. Simply click Ctrl + A to select all files in Temp, then hit Del to remove them all to make this process faster.

How to Decrypt Hhuy files
Even for experts, dealing with the implications of ransomware data encryption may be difficult. However, there are some file-restoration tools that may allow you to decode encrypted data. To have success with them, though, you first need to determine what variant of Ransomware you’re dealing with. Look at the end of the encrypted files and their file extensions to obtain this information.
A new Djvu Ransomware
STOP Djvu Ransomware is the latest Djvu ransomware variant that you may encounter. This particular threat distinguishes from others because of the .Hhuy file encryption that it add to the encrypted data.
Fortunately, there is a file-decryption tool included in the link below that may help you retrieve data encoded by this particular ransomware variant. It may be downloaded by clicking on the link provided.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
Run the decryption tool that you’ve downloaded as an administrator, then select “Yes” to start it. Please read the included instructions and the related license agreement carefully before starting. The decryption process will begin when you press the Decrypt button.
If you need to decode files encrypted using unknown offline keys or online encryption, proceed with caution, as this tool may not be able to decode them. If you have any questions or concerns, please feel free to post them in the comments area down below.
Important! Before attempting to recover data that has been encrypted, make sure to thoroughly search your computer for ransomware-related files and harmful registry entries.
A Trojan or Rootkit may be preventing you from manually removing Hhuy from your computer, despite your best efforts to remove the Ransomware. If a computer is infected with Ransomware and other malware, it is typical for the two to work together. Anti-malware software that can remove all dangers is ideal in these situations because it prevents them from working together to help one another. We’ve included a link to one such effective removal program in this guide, and we highly recommend that you use it if you’re still having issues with Hhuy. If you have Hhuy-related malware on your computer, this page’s free online virus scanner and the recommended anti-virus software can help you remove it.

Leave a Comment