.Horse
.Horse is a ransomware infection that is very harmful and can keep various digital files hostage. Virtually any operating system can be compromised by .Horse and the malware can encrypt the information stored in it.
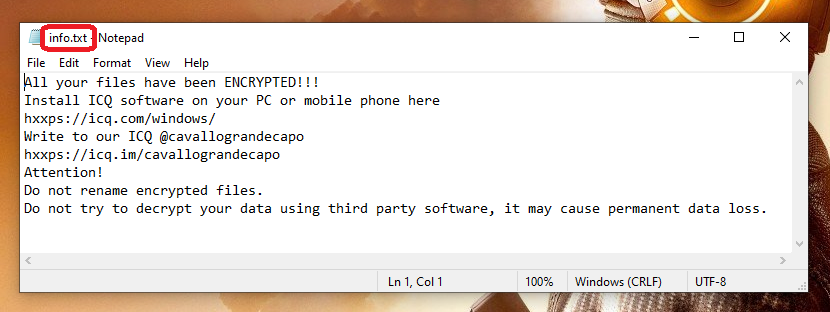
Once the .Horse Ransomware has encrypted all of your files you will find this message in a .txt file.
Viruses based on ransomware are terrible malware pieces used for extortion purposes. In this article, we will focus our attention on a new threat called .Horse, which is a representative of the ransomware cryptovirus subcategory. This infection can secretly encrypt the files that it detects on the infected computer, and then demand a ransom in exchange for decrypting them.
The .Horse Ransomware
One of the key things which makes the .Horse virus so destructive is that users cannot identify and stop the operation of the ransomware until it completes its mission and that is virtually in all cases of infection. This is because most security programs typically fail to identify the process of encryption of the .Horse virus as malicious.
.Horse does not destroy files, remove or damage anything on the PC. Many antivirus programs, however, seek precisely such actions and may not consider an ongoing file encryption process in the background as something harmful. Unfortunately, this enables ransomware viruses to execute the hidden file encryption process without interference and, after this process is completed, they automatically generate a message requesting ransom on the computer of the victim.
If this cryptovirus has secretly infected your system, you will probably need some assistance in order to cope with the attack and the catastrophic consequences that might have followed. That’s why we’ve published some useful information on the options you may choose from in the event that .Horse has locked your data. Below you will also find a detailed removal guide and a professional removal tool which can help you remove the infection, as well as some tips on how to recover some of your files without paying a ransom to the hackers.
The .Horse file encryption
The .Horse file encryption is a complex code that keeps your files inaccessible. The hackers behind the .Horse file encryption demand a payment (in Bitcoin or some other cryptocurrency) in return for a decryption key that can undo the applied file encryption.
Unfortunately, the safety of your machine and your data is not guaranteed in any way until the ransomware infection is removed. In many cases, fulfilling the hackers’ ransom demands leads only to money loss as the crooks disappear without sending any decryption solution in return.
This is why many security professionals, including our “how to remove” team advise the victims of threats like .Horse to seek alternative file-recovery solutions and to remove the malware with trusted security tools. As soon as they do so, they will be able to start using their computer as before and will be able to connect backup sources and other devices that may help them restore some of the encrypted data from copies.
Of course, new ransomware infections like .Horse may be difficult to deal with if you are not a professional. That’s why below we have published a detailed removal guide with step-by-step instructions and some file-recovery suggestions, as well as a reliable removal tool for self-help.
SUMMARY:
| Name | .Horse |
| Type | Ransomware |
| Detection Tool |
.Horse Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Comment