I am not going to neglect
“I am not going to neglect” is a highly dangerous malicious program that belongs to the class of Trojan horse viruses. “I am not going to neglect” is capable of inflicting all sorts of harm on the contaminated machine, so it must be removed as soon as possible.
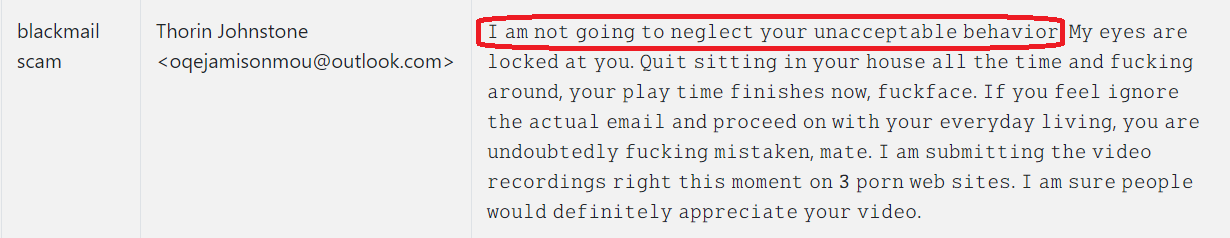
The “I am not going to neglect” Email is made to scare people into sending money.
Trojan horse viruses are notorious for their harmful abilities and the sheer versatility of those abilities, as well. These are perhaps the most multifunctional of all malware types out there, and this has made them by far the most favorable tool for hackers and cybercriminals around the globe. And the statistics speak for themselves in that regard. An estimated 80%+ of all malware attacks are done by Trojans.
But in addition to being so uniquely flexible, Trojans like “I am not going to neglect” are also very well known for their stealth. Trojan horse infections typically run without the display of any symptoms, which makes them incredibly difficult to detect. In addition, these threats hide masterfully and can disguise themselves as important system files and processes.
This is a point worthy of mentioning, especially when it comes to the removal of “I am not going to neglect”, as it may be confused with actual system files. Therefore, we should warn you that the manual removal of this virus might require a slightly higher level of tech-savviness. If you feel you will be comfortable with the execution of the steps in our removal guide, please proceed to those. And if you would rather have the process handled automatically, we also have a professional removal tool that you can make use of.
The I am not going to neglect Email
If recently you have received the I am not going to neglect Email the first thing you should do is delete it. Such Email is distributed to numerous users and is created into tricking someone into sending money.
Due to the fact that “I am not going to neglect” is among the latest Trojan horse variants to be reported to us by users, there’s still insufficient data on it to pinpoint exactly what the hackers behind it are using it for. However, we would like to still outline the most common things that malware of this type is designed to do.
Namely, one of the usages that has started to gain momentum in recent years is cryptocurrency mining. Trojan horse viruses can be set to exploit the resources of the infected PC in order to mine and send cryptocurrencies to the cybercriminals. Alternatively, those resources can be put to work for other purposes, such as distributing spam, for example.
Trojan horse viruses are very commonly also used as backdoors for other malicious code, in most cases – ransomware. With that in mind, it may be a good idea to perform a full system scan after you’ve deleted “I am not going to neglect”, just to make sure it hasn’t introduced other viruses to your machine.
Then there are perhaps the more harrowing options of being spied on and having your data stolen. This may pertain to personal information that relates to your identity (social media accounts, social security number, government issued documents, etc.). Or it may also be information that has to do with your online banking account and payment details, where the criminals may find a way to steal money from you.
As you can see, there’s a long list of possibilities and this one is by no means exhaustive. So preventing future attacks of this kind is as important as getting rid of the current infection with “I am not going to neglect”.
SUMMARY:
| Name | “I am not going to neglect” |
| Type | Trojan |
| Detection Tool |
Remove “I am not going to neglect” Email
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment