I have succeeded to gain a total access to all your devices
“I have succeeded to gain a total access to all your devices” is a very dangerous malicious threat capable of causing an array of harm on infected computers. “I have succeeded to gain a total access to all your devices” belongs to the Trojan horse virus category and should be handled with caution if detected.
Threats like Trojans, ransomware, spyware and similar nasty viruses are not the only security threats that you may encounter while surfing the web. There are also a lot of scams that try to trick unsuspecting users and involve them in shady cyber-criminal schemes.
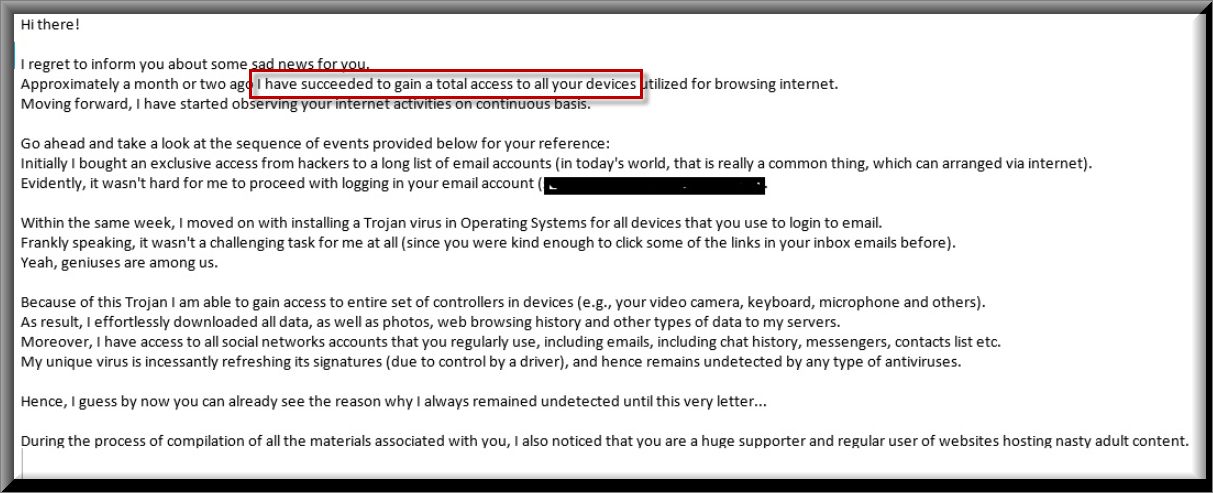
Many of our users reported to us about an ongoing email spam with the following message:
Hi there!
I regret to inform you about some sad news for you.
Approximately a month or two ago I have succeeded to gain a total access to all your devices utilized for browsing internet.
Moving forward, I have started observing your internet activities on continuous basis.Go ahead and take a look at the sequence of events provided below for your reference:
Initially I bought an exclusive access from hackers to a long list of email accounts (in today’s world, that is really a common thing, which can arranged via internet).
Evidently, it wasn’t hard for me to proceed with logging in your email account (“I have succeeded to gain a total access to all your devices””I have succeeded to gain a total access to all your devices”xx@”I have succeeded to gain a total access to all your devices””I have succeeded to gain a total access to all your devices”xx.com).Within the same week, I moved on with installing a Trojan virus in Operating Systems for all devices that you use to login to email.
Frankly speaking, it wasn’t a challenging task for me at all (since you were kind enough to click some of the links in your inbox emails before).
Yeah, geniuses are among us.Because of this Trojan I am able to gain access to entire set of controllers in devices (e.g., your video camera, keyboard, microphone and others).
As result, I effortlessly downloaded all data, as well as photos, web browsing history and other types of data to my servers.
Moreover, I have access to all social networks accounts that you regularly use, including emails, including chat history, messengers, contacts list etc.
My unique virus is incessantly refreshing its signatures (due to control by a driver), and hence remains undetected by any type of antiviruses.Hence, I guess by now you can already see the reason why I always remained undetected until this very letter…
During the process of compilation of all the materials associated with you,
I also noticed that you are a huge supporter and regular user of websites hosting nasty adult content.
Turns out to be, you really love visiting porn websites, as well as watching exciting videos and enduring unforgettable pleasures.
As a matter of fact, I was not able to withstand the temptation, but to record certain nasty solo action with you in main role,
and later produced a few videos exposing your masturbation and cumming scenes.If until now you don’t believe me, all I need is one-two mouse clicks to make all those videos with everyone you know,
including your friends, colleagues, relatives and others.
Moreover, I am able to upload all that video content online for everyone to see.
I sincerely think, you certainly would not wish such incidents to take place, in view of the lustful things demonstrated in your commonly watched videos,
(you absolutely know what I mean by that) it will cause a huge adversity for you.There is still a solution to this matter, and here is what you need to do:
You make a transaction of $1340 USD to my account (an equivalent in bitcoins, which recorded depending on the exchange rate at the date of funds transfer),
hence upon receiving the transfer, I will immediately get rid of all those lustful videos without delay.
After that we can make it look like there was nothing happening beforehand.
Additionally, I can confirm that all the Trojan software is going to be disabled and erased from all devices that you use. You have nothing to worry about,
because I keep my word at all times.That is indeed a beneficial bargain that comes with a relatively reduced price,
taking into consideration that your profile and traffic were under close monitoring during a long time frame.
If you are still unclear regarding how to buy and perform transactions with bitcoins – everything is available online.Below is my bitcoin wallet for your further reference: 16bHkVFULVmxTGVi2XKpwzkt5KrRnThzPg
All you have is 48 hours and the countdown begins once this email is opened (in other words 2 days).
The following list includes things you should remember and avoid doing:
> There’s no point to try replying my email (since this email and return address were created inside your inbox).
> There’s no point in calling police or any other types of security services either. Furthermore, don’t you dare sharing this info with any of your friends.
If I discover that (taking into consideration my skills, it will be really simple, because I control all your systems and continuously monitor them) –
your nasty clip will be shared with public straight away.
> There’s no point in looking for me too – it won’t result in any success. Transactions with cryptocurrency are completely anonymous and untraceable.
> There’s no point in reinstalling your OS on devices or trying to throw them away. That won’t solve the issue,
since all clips with you as main character are already uploaded on remote servers.Things that may be concerning you:
> That funds transfer won’t be delivered to me.
Breathe out, I can track down everything right away, so once funds transfer is finished,
I will know for sure, since I interminably track down all activities done by you (my Trojan virus controls all processes remotely, just as TeamViewer).
> That your videos will be distributed, even though you have completed money transfer to my wallet.
Trust me, it is worthless for me to still bother you after money transfer is successful. Moreover, if that was ever part of my plan, I would do make it happen way earlier!We are going to approach and deal with it in a clear manner!
In conclusion, I’d like to recommend one more thing… after this you need to make certain you don’t get involved in similar kind of unpleasant events anymore!
My recommendation – ensure all your passwords are replaced with new ones on a regular basis.
Unfortunately, the use of online scams, phishing emails and false claims has turned into a lucrative business for some people with malicious intentions and, recently, there have been a lot of reports about the increasing number of different schemes and criminal tactics. For instance, a viral email Bitcoin scam campaign has been spreading around lately and has been causing panic and frustration for a large number of people.
If you are one of the victims targeted by this particular scam, then you most probably have received a scary email message in your inbox that claims there’s a dormant Trojan horse infection inside your computer. And if you don’t pay a certain amount of money (in Bitcoin) to the hacker behind the infection, they threaten to activate the Trojan and mess with your system. Emails with this scenario are typically nothing but a scam that shouldn’t be taken at face value. Their aim is to scare users and make them pay money to some self-proclaimed hackers without any actual reason.
However, sometimes, these messages may contain some real infections and if you open or interact with them, you may get compromised by a real Trojan horse without knowing it, such as “I have succeeded to gain a total access to all your devices” and Geek Squad Email. That’s why you have the full right to be worried that there may indeed be malware in your system if you have clicked on one of them recently.
Rushing to fulfill the ransom demands of some anonymous crooks and believing their messages, on the other hand, is not advisable. In fact, we believe it is a much better option to simply scan your computer for malware with the help of a trusted security program and try to remove any potential hidden threats that the scan detects.
Beware of emails that spread malware!
Being spammed with dozens of emails that ask you to pay ransom in order to prevent hidden malware from causing harm to your system is a common cyber-criminal scam. A ruse that only aims to scare people and generate quick money for the crooks behind the scheme. And while there is no real reason to believe any of the statements in the messages or send any money to anyone, you still should not overlook the fact that threats like “I have succeeded to gain a total access to all your devices” could be found inside such messages and a real infection may occur without your knowledge.
Like most Trojan-based pieces of malware, this one can be very stealthy and can lie dormant without any visible symptoms until the hacker decides to activate it and to attack the system. For this reason, if you have recently been bombarded with email scam messages and have interacted with them, it is very important that you ensure your PC is clean and there is nothing malicious on it which could cause you harm when you least expect it. In this regard, below we have prepared a detailed removal guide and a professional scanner tool that can help you to check your system and remove “I have succeeded to gain a total access to all your devices”.
SUMMARY:
| Name | “I have succeeded to gain a total access to all your devices” |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | There may not be any visible symptoms when a Trojan horse compromises your system. |
| Distribution Method | Spam is a common method of distribution along with malicious ads, infected email attachments and pirated content. |
| Detection Tool |
Remove “I have succeeded to gain a total access to all your devices” Bitcoin Email Virus
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment