I have video of you
“I have video of you” is what is known as a Trojan horse virus. As such, “I have video of you” can infect pretty much all operating systems, including all versions of Windows.
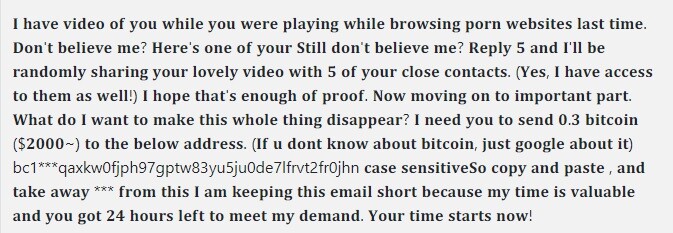
The “i have video of you while you were playing” Email
And once it becomes incorporated into your computer, this software will typically burrow very deep so it can remain hidden for as long as possible. With that in mind, you should also know that Trojans like “I have video of you” don’t tend to exhibit any kind of symptoms, which makes them an invaluable tool for hackers. As a matter of fact, this very quality of theirs is largely what has made them the most numerous malware category on the web. As it so happens, Trojans are responsible for some 80-90% of all malware attacks, depending on the source. But either way, the stats are quite impressive – and not in a good way.
Therefore, it’s quite lucky that you have managed to detect “I have video of you” and are now searching for a way to get rid of it. For this purpose we have designed a special removal guide that is free of charge and available to all “I have video of you” victims right on this very page. We must warn you that it is vital you follow all steps in the removal exactly as they are written, otherwise you risk deleting the wrong files and this may result in permanent system damage. If, however, you’d rather not risk it, we also have a professional malware removal tool available which will handle the process of eliminating this Trojan for you.
“I have video of you”’s capabilities
Another factor that makes Trojans irreplaceable to hackers and cybercriminals is their unique versatility. They are, so to speak, a Jack of many trades. In other words, a malicious piece of programming like “I have video of you” can be tasked with anything from data theft to data corruption, to system resources exploitation and even with spying on its victims!
It’s no joke, “I have video of you” could potentially give its owners remote access to your webcam and microphone, allowing them to watch you and eavesdrop on you without your knowledge. Similarly, this virus can also log your keystrokes, thus gaining access to your login details, passwords, pin codes and whatever other sensitive and private information that you can think of. In turn, this information can be misused in all sorts of ways.
You could fall victim to identity theft, your bank accounts can be drained, the hackers could take control of your social media, etc. Alternatively, as a very different example, malware like this can turn your computer into a bot and make it mine cryptocurrencies for the hackers. In that same line of thought, your machine’s resources may also be put to work for other purposes, like distributing spam or infecting other computers in the same network.
And the list goes on and on. What’s important is that you try and prevent such attacks before they occur henceforth. You can do this by making sure your system isn’t vulnerable (i.e. updating it on a regular basis and having a high-quality antivirus program) and by avoiding the most obvious malware sources such as spam messages, unsafe web locations, pirated and cracked content, etc.
SUMMARY:
| Name | “I have video of you” |
| Type | Trojan |
| Detection Tool |
Remove I have video of you Email
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment