I made a split-screen video
If “I made a split-screen video” has invaded your computer, you are dealing with a very dangerous Trojan horse virus. “I made a split-screen video” may cause irreversible damage to you and your system, so it is crucial that you remove it as soon as possible.
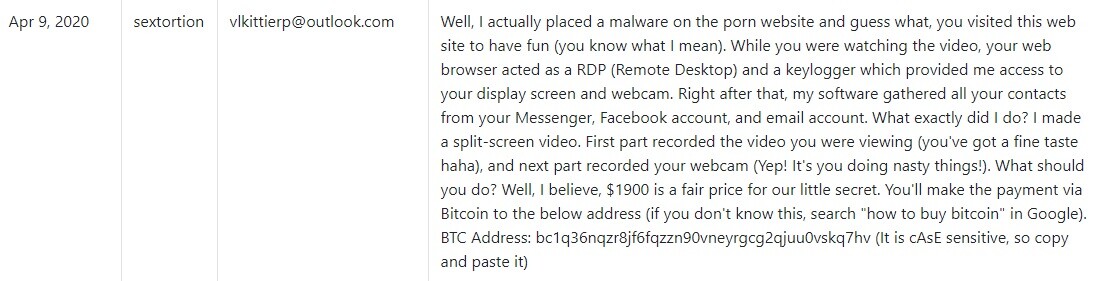
The “I made a split-screen video” Email
Many of our users complained that they received an Email with the following message:
I know, xxx, is your password. You don’t know me and you’re thinking why you received this e mail, right?
Well, I actually placed a malware on the porn website and guess what, you visited this web site to have fun (you know what I mean). While you were watching the video, your web browser acted as a RDP (Remote Desktop) and a keylogger which provided me access to your display screen and webcam. Right after that, my software gathered all your contacts from your Messenger, Facebook account, and email account.
What exactly did I do?
I made a split-screen video. First part recorded the video you were viewing (you’ve got a fine taste haha), and next part recorded your webcam (Yep! It’s you doing nasty things!).
What should you do?
Well, I believe, $1900 is a fair price for our little secret. You’ll make the payment via Bitcoin to the below address (if you don’t know this, search “how to buy bitcoin” in Google).
BTC Address:
bc1qzl2qlywq8fzfm49e7mvsuz4yvpdwpzfqs5g85r
(It is cAsE sensitive, so copy and paste it)
Important:
You have 24 hours in order to make the payment. (I have an unique pixel within this email message, and right now I know that you have read this email). If I don’t get the payment, I will send your video to all of your contacts including relatives, coworkers, and so forth. Nonetheless, if I do get paid, I will erase the video immidiately. If you want evidence, reply with “Yes!” and I will send your video recording to your 5 friends. This is a non-negotiable offer, so don’t waste my time and yours by replying to this email.
Trojan horse viruses are notorious for their very wide range of malicious capabilities. And this has contributed to making them the most numerous malware category out there. A whopping 80-90% on average of all malware attacks are owed exactly to Trojans, so you are more likely to land a Trojan horse virus than any other type of malicious code.
And this has come to be because they can perform very many different tasks on the infected computer. On the other hand, Trojans have also gained a reputation for being sneaky and almost completely unnoticeable. It’s not uncommon for variants like “I made a split-screen video” to sometimes remain in the system doing their dirty business completely undisturbed for weeks, months and even years at a time. This makes it highly difficult to detect Trojans, especially if you don’t have a powerful enough antivirus tool on your computer.
But the good news is that, since you’re here, you’ve already managed to discover “I made a split-screen video” on your PC. And that means you’re already halfway through the process of dealing with this issue. Now all you have to do is remove the virus and we can assist you in this with our detailed removal guide below. Just be advised that this malware has a tendency to disguise itself as and hide among system files, so caution is necessary. If you fear accidently deleting the wrong file, you might want to use our automatic removal tool instead.
I made a split-screen video. First part recorded the video you were
We won’t cover all the potential harmful effects that “I made a split-screen video. First part recorded the video you were viewing” may have on its victims’ computers, but we’ll briefly outline the most common ones. For instance, there’s outright system corruption, there’s data theft that can be achieved through various means such as keystroke logging and others. This means that theoretically the cybercriminals behind “I made a split-screen video. First part recorded the video you were viewing” could potentially gain access to sensitive information like passwords, logins, online banking credentials, etc.
In addition, a Trojan horse virus like this one may also be used to exploit your system’s resources and serve the hackers in various ways. Your computer could be made to mine cryptocurrencies for them, for instance, send out spam, infect other users, etc.
Now, what’s important to know when it comes to preventing such attacks is the methods used to distribute Trojans. And spam messages tend to be the leading source for this, as well as other types of malware. Therefore, be very critical of any incoming emails or social media messages, especially those containing attachments and/or links. Similarly, malrvertisements have become a highly common Trojan distribution method. These are basically online ads that have been injected with malicious code like “I made a split-screen video”. And upon clicking such ads, users automatically download the Trojan or whatever malware was in them. And for this reason we usually recommend that users abstain from interacting with online ads.
SUMMARY:
| Name | “I made a split-screen video” |
| Type | Trojan |
| Detection Tool |
Remove “I made a split-screen video” Email Malware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment