I need your 100% attention
I need your 100% attention is a Trojan horse virus that targets computers with the idea of secretly performing malicious activities in it. I need your 100% attention rarely causes any symptoms when operating on the compromised computer which is why it can complete its harmful tasks without being detected.
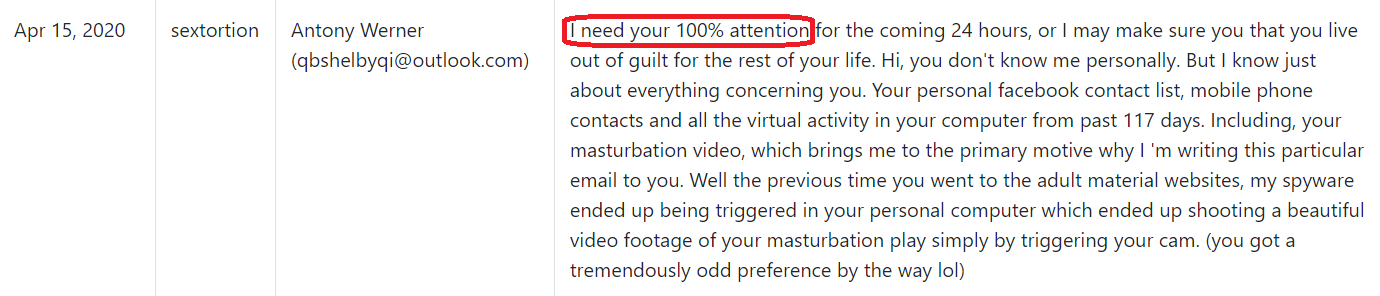
The “I need your 100% attention” Email
If you think that this awful piece of malware has sneaked inside your computer, we advise you to act quickly and do not allow it to run any longer to complete its malicious agenda. One quick and effective way to remove “I need your 100% attention” is to use the removal guide below and the professional removal tool attached to it. Before you follow the instructions, though, we highly recommend that you take a few more minutes to find out more about the features of this threat and to learn the specifics of the Trojan horse viruses so that you have a better chance to deal with the threat at hand without harming your system any further. Besides, the information in the next lines will help you keep your device, files, and virtual privacy safe in the future.
What can “I need your 100% attention” do?
Like a typical Trojan, “I need your 100% attention” can be used for a lot of criminal purposes which is why it is best to remove it as soon as possible. Unfortunately, it is difficult to tell you what the exact end goal of this infection is, since it is a new virus, and the details about what it is doing when it nests inside your machine are still not enough to reveal its agenda.
If not detected and eliminated on time, this malware may spy on your activities without your knowledge, collect personal information from your computer and transmit it to remote servers, steal sensitive data, passwords and login credentials and perform online banking crimes. One of the most common uses, however, is linked to the Trojan’s ability to insert viruses and other malware such as Ransomware and Spyware inside the infected computer. This can happen through existing system vulnerabilities (such as the absence of reliable security software or an outdated program) which the Trojan may exploit to sneak in other infections. This virus can even take control of certain functions of the machine and make it an automated bot that uses much of the device’s RAM and CPU power, to mine Bitcoins for hackers, send spam emails, or engage in DDoS attacks.
What are the potential symptoms of a Trojan horse infection?
While most infections of Trojan horses go unnoticed for long periods, some symptoms can still be seen, depending on what the virus attempts to complete. For example, when the Trojan uses your computer as a cryptocurrency mining machine, high rates of system resources are likely to be used, which leads to significant machine slowdowns and even potential crashes. Deletions and changes in your data plus unusual software mistakes and unresponsiveness to your commands may also suggest a possible infection with “I need your 100% attention” or another Trojan-based threat. Generally, any odd activities or modifications in your computer’s settings and performance that have not been approved by you might be possible indicators for a Trojan Horse infection, so be sure to search your device with a trusted anti-malware tool and remove any related files without fail.
SUMMARY:
| Name | I need your 100% attention |
| Type | Trojan |
| Detection Tool |
Remove I need your 100% attention Email
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment