I require your complete attention
I require your complete attention falls into the category of the notorious Trojan horse viruses. Trojans like I require your complete attention are particularly versatile and can inflict a whole array of damage on the infected computer.
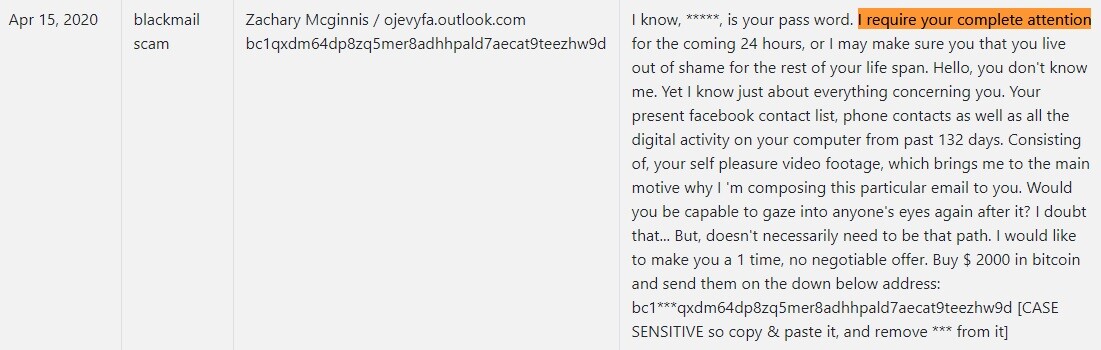
The “I require your complete attention” Email
But before we get into the gory details, we would first like to brighten this terrible instance up by congratulating you on actually discovering “I require your complete attention” in your system. Aside from being extraordinarily flexible, these malicious pieces are also infamous for their stealth. It’s not unheard of for Trojan horse viruses to burrow so deep into the OS that they remain hidden over long periods of time – sometimes even years.
Another piece of good news is that you have all the tools necessary to successfully handle this infection and remove “I require your complete attention” from your PC. Below is a removal guide that will walk you through the process. And if for whatever reason you don’t trust yourself around important system files and other vital components of your system, we recommend you use our professional removal tool instead. It will scan your system for “I require your complete attention” and any other malware that may be hidden inside, and will clean it of all infections.
What may “I require your complete attention” be up to?
With the vast amount of different malicious tasks that Trojans are capable of executing, there’s no way of knowing for sure what exactly “I require your complete attention”’s plan is for your system. But we can give you an idea about the most common usages for this type of malware so you have a better understanding of what you’re dealing with.
Malicious code of the Trojan horse type can, for instance, be made to spy on you and collect information from your PC. It can log your keystrokes and thus gain access to all the information that you type with the help of your keyboard. It may also tap into your microphone and webcam and allow the hackers behind it remote access to your computer. Furthermore, a virus like “I require your complete attention” can even hijack your traffic and redirect it to the cybercriminals’ servers. This way they can gain access to sensitive information such as passwords, login credentials, online banking details, etc.
In addition, a Trojan horse virus such as “I require your complete attention” can exploit your computer’s resources and put them to work mining cryptocurrencies for the hackers. In fact, this particular application for Trojans has become rather popular in recent years. Alternatively, your PC can made to act as a bot and infect other computers in its network. And it may even be made to send out spam, for example, as well.
So with this in mind, it’s important that you see to “I require your complete attention”’s removal as soon as possible to prevent it from causing any further harm. And to prevent such attacks in the future, make sure that your system isn’t vulnerable in any way. This includes having a working antivirus program with all the latest bells and whistles. But it also means regularly installing updates whenever those become available. Be sure to also practice safe web browsing habits and stay away from potentially dangerous content and web locations.
SUMMARY:
| Name | I require your complete attention |
| Type | Trojan |
| Detection Tool |
Remove I require your complete attention Email
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment