Imgcreator.zmo.ai is a website for generating AI images that seems perfectly legitimate at first sight, but many users have recently been getting automatic redirects to it for no apparent reason. This has led to a lot of confusion surrounding the Imgcreator.zmo.ai site and even made some people think it’s something malicious.
Before we go any further, we must make it clear that Imgcreator.zmo.ai is technically not harmful. It does have some bad user reviews due to misleading and non-transparent subscription plans and practices, but it’s still mostly a legitimate site.
However, if you are getting random redirects to it and don’t know why, it’s possible there’s something unwanted in your browser (such as a browser hijacker) that you need to remove. This is why many people refer to it as the “Imgcreator.zmo.ai virus”. We also came across user reports stating the redirects are caused by legitimate extensions.
Therefore, the focus in this post will be to help you remove any hijacker or extension that might be triggering the redirects.
How to Stop Imgcreator Zmo AI Redirects and Popups
As we said, the likely cause behind the imgcreator zmo ai redirects/pop-ups is a browser hijacker attached to your Chrome (or other) browser. The other likely reason is if the site itself has gained notifications permission inside the browser. In either case, the way to solve the problem is the same – clean your browser from any extensions that might be causing the redirects and restore its settings.
SUMMARY:
| Name | Imgcreator.zmo.ai |
| Type | Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Stopping the Imgcreator.zmo.ai redirects is typically very easy to do if they are caused by a regular extension that doesn’t try to take over the browser. However, if you have a hijacker on your hands, such as Boyu.com.tr or Skyjem, you may need to perform some extra steps to take care of the problem. In both cases, the troubleshooting process begins in the same way.
Start by going to your Chrome browser, click the three dots in the top-right, and see if there’s a “Managed by your organization” message at the bottom of the Chrome menu. If there is, that means a hijacker has enforced a third-party policy in your browser and you won’t be able to remove it before that policy is gone. In this case, directly go to the next section of our guide, where we show how to remove any third-party policies, and then return to the steps here.
If there isn’t a “Managed by…” message, the redirects are probably caused by a legitimate extension and not a hijacker, in which case you can directly proceed with the next steps:
- In the Chrome menu, open Extensions > Manage Extensions.
- Look at the list of extensions and remove the ones you’ve installed most recently. Also uninstall any of the following if you have them:
- Ad Speedup
- L.O.C.
- Dark Reader
- Return Youtube Dislike
- Multiple Twitter Accounts Switcher
- Something else that can also help you figure out which extension is triggering the redirects is checking the end of the URL address of Imgcreator.zmo.ai. This indicates what extension is triggering the redirect. For instance, if the URL ends in ?ref=tw32b, the refers to the Multiple Twitter Accounts Switcher extension.
- Next, go to your Chrome settings (Chrome menu > Settings) and open Privacy and Security.
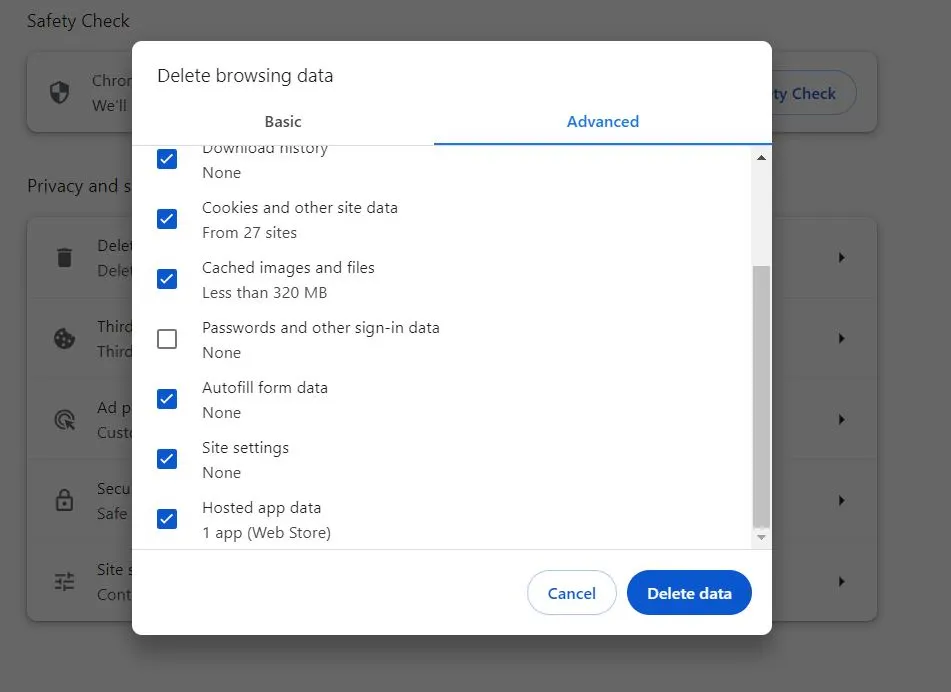
- Click on Delete browsing data > Advanced, set an appropriate time period that goes back prior to the start of the redirects, check all boxes except Passwords, and click Delete Data.
- Then scroll down to Site Settings and open it. Check the Allow section of each type of site permission for Imgcreator.zmo.ai, prod-backend.adspeedup.com, or any other suspicious sites, and remove them.
- Once you think you’ve deleted all extensions that might be causing the redirect, restart Chrome and see if the problem is resolved.
If you are no longer getting the suspicious redirects, you can start re-installing the removed extensions one by one. The idea is to see when the redirects start again and thus figure out which exact extension is the culprit.
Stop the Imgcreator.zmo.ai Chrome Redirects by Removing the “Managed by your organization” Policy
If you have the “Managed by your organization” message in your browser and you aren’t allowed to remove one or more of the extensions installed in it, you are most likely dealing with a browser hijacker. You’ll be able to remove it and put an end to the Imgcreator.zmo.ai pop-ups and redirects only after the rogue policy is removed. Here is how you can do this:
- Go to the Start Menu, type “Edit Group Policy” and press Enter.
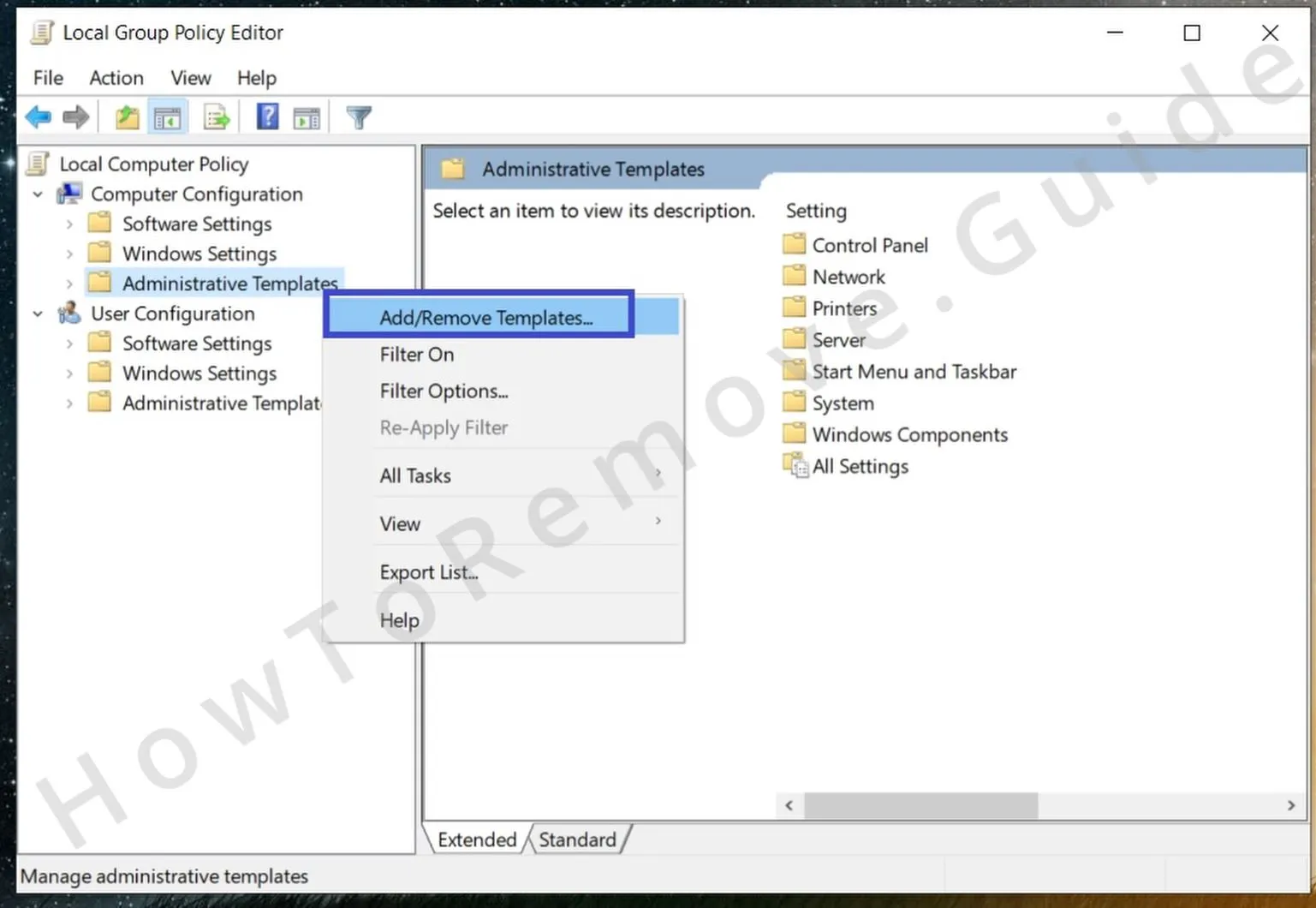
- Expand Local Computer Policy > Computer Configuration, right-click on Administrative Templates, and select Add/Remove Templates.
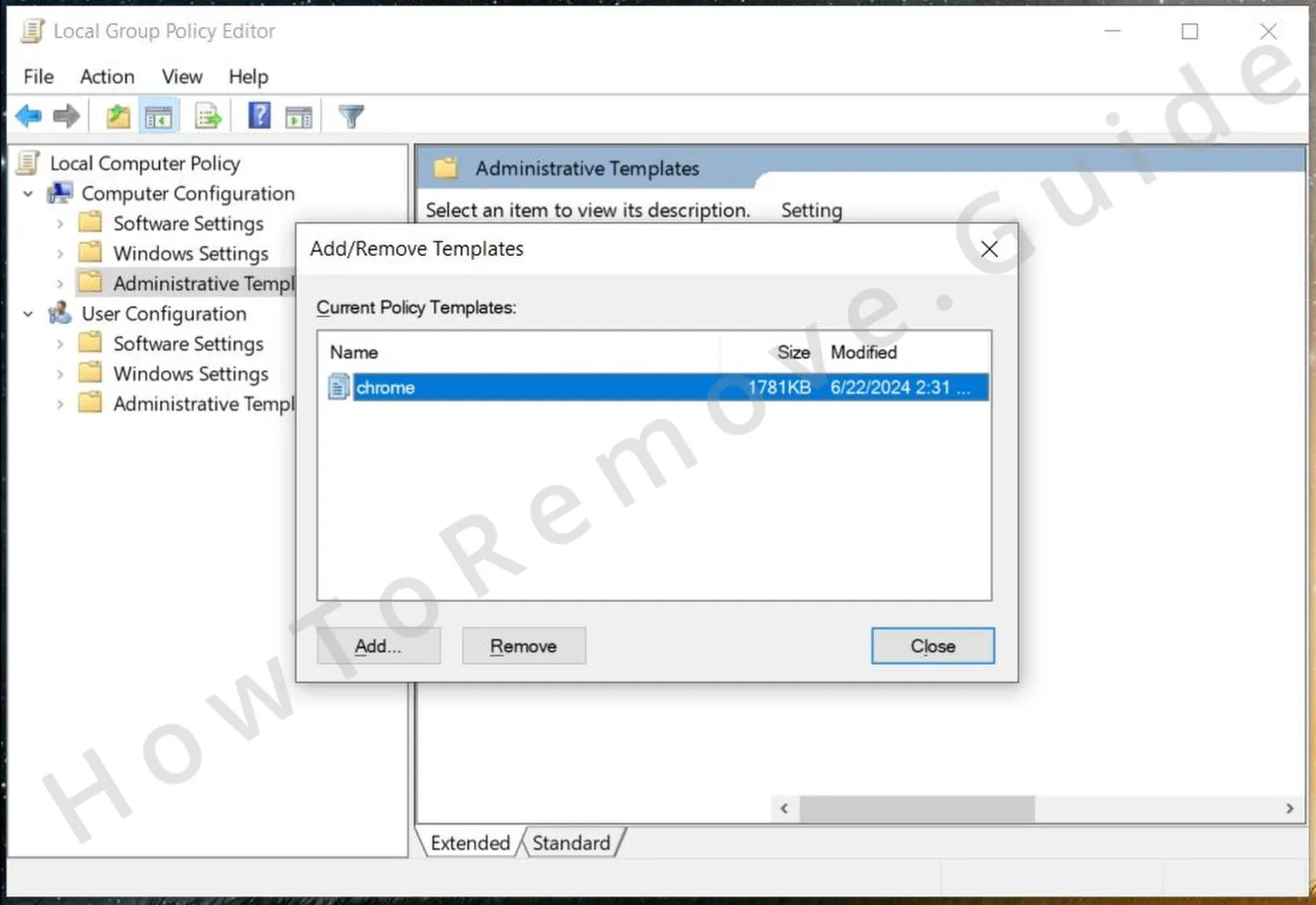
- Remove any items shown in the list that opens and then close it and close the Policy Editor.
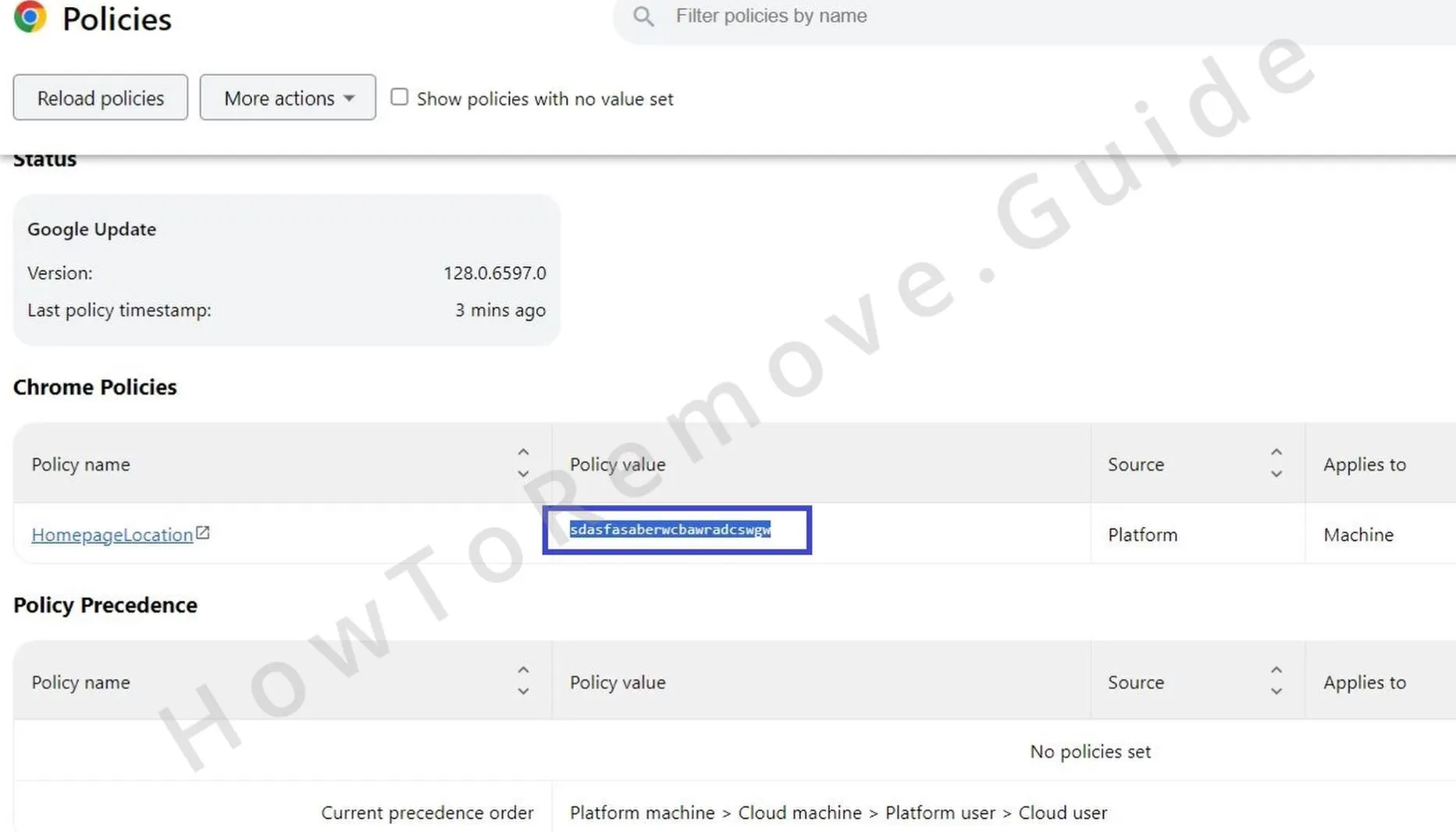
- Now go to your Chrome browser, type Chrome://Policy in the URL bar, and press Enter to go to that page. If you are in another browser, replace “Chrome” with the name of that browser (for instance, “Edge://Policy” for MS Edge).
- Look at the lost of policies and if you see one that has a long sequence of random letters as its value, copy it and save it somewhere (notepad, sticky notes, etc.).
- Then go to the browser’s menu > Extensions > Extensions Manager, turn on Developer Mode (top-right), then copy the ID of the extension (or extensions) that you want to remove, and save those IDs too.
- Now search for the Registry Editor in the Start Menu and open it as Administrator.
- The press Ctrl + F, paste the policy value that you saved earlier, and search for it.
- If an item is found, delete the registry key (folder) where it’s contained and search again. Delete the next thing and rinse and repeat until no more results appear. Then do the same thing with any other policy values and also with the saved extension ID or IDs.
- Also go to the following keys in the registry and delete them (the bolded key at the end):
- HKEY_CURRENT_USER\Software\Google\Chrome
- HKEY_CURRENT_USER\Software\Policies\Google\Chrome
- HKEY_LOCAL_MACHINE\Software\Google\Chrome
- HKEY_LOCAL_MACHINE\Software\Policies\Google\Chrome
- HKEY_LOCAL_MACHINE\Software\Policies\Google\Update
- If you are using a different browser, look for keys with their names in those same directories and delete them.
- Once you’ve done all that, we also recommend that you download the Chrome Policy Remover and run it as an administrator. You’ll be warned by windows, but don’t worry, the tool is safe. Simply click More Info > Run Anyway to start it. Then an automatic script will run and once it’s done, all Chrome policies will be removed (doesn’t work for other browsers).
Once you’ve cleaned the rogue policy from your browser, go back to the start of this guide and perform the steps there to delete any unwanted extensions and reset the permission settings of the browser so that you don’t get any more Imgcreator.zmo.ai redirects.
Is Imgcreator.zmo.ai a Virus Site?
We thoroughly researched the topic about Imgcreator.zmo.ai and so far, it seems that this site is safe and won’t expose you to danger. However, as we said at the start, there are many user complaints about it concerning its pricing, subscription plans, and non-transparent practices. Some users go as far as to say it’s a scam site because of all those factors.
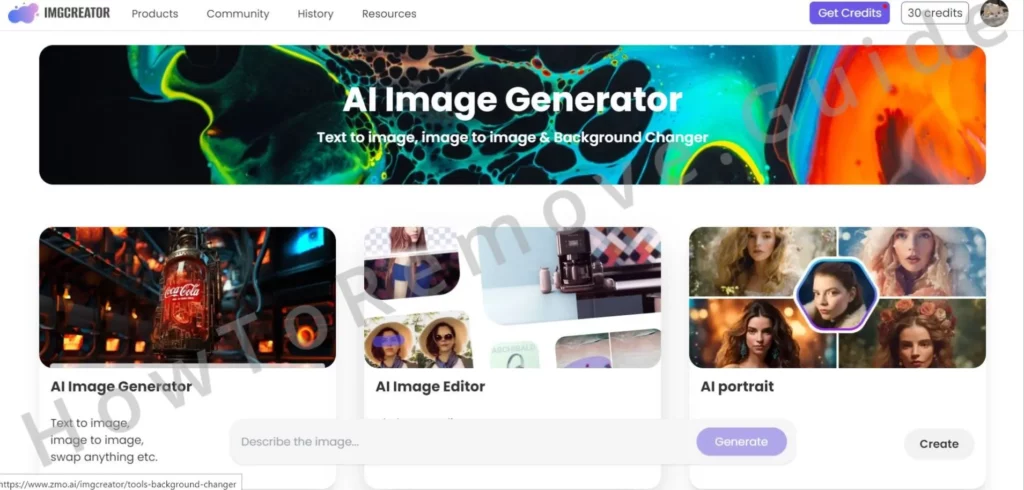
That being said, despite its flaws, it does provide the functionality of creating AI images. It also doesn’t spam you with ads or attempt to download anything suspicious on your PC. Obviously, getting sudden redirects to it can be frustrating and get you worried about the safety of your system and privacy, but those concerns should be directed at the cause of the redirects and not the site itself.
But as you can see from our guide, a lot of times, the redirects would be caused by some legitimate extensions with high ratings on the Chrome Web Store, such as L.O.C., Dark Reader Return, and Youtube Dislike. Some extensions even let you opt out of the redirects in their settings.
This obviously doesn’t mean you should ignore the redirects and what’s causing them, because, as we said, it could also be a hijacker. Maybe Imgcreator.zmo.ai isn’t a dangerous site, but if you have a hijacker in your browser, you may also start to get redirects to more questionable and unsafe web addresses. Therefore, we still strongly advise you to look through your browser and remove anything unwanted with the help of our instructions or the professional anti-malware tool available on this page.

Leave a Reply