Iphone-notification.com
Iphone-notification.com is an application of the browser hijacking type that can make unwanted modifications to your main browser. For instance, Iphone-notification.com can substitute the default homepage address with a new one and replace the search engine with one that generates sponsored results.
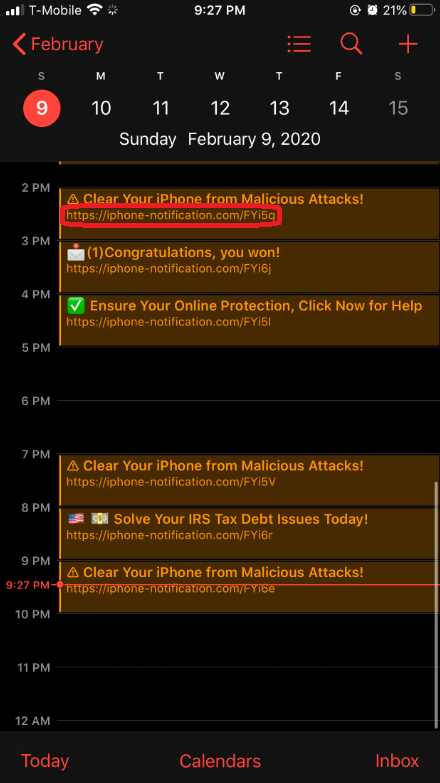
The Iphone-notification.com Virus will display pop up ads and messages
If you are interested in this article, strange alternations may have taken place inside your Safari,Chrome or Firefox browser. Many different ads might have started to pop-up all over your screen. New browser components may have been installed without your approval and you may have started to experience unwanted redirects to irrelevant websites. Fortunately, we have given detailed information on the software that stands behind these changes and, if you read the next lines, you will learn more about its activities and the methods that you can use to uninstall it.
Iphone-notification.com is the probable source of the above-mentioned browsing disturbance. This is a program that is a member of the so-called browser hijacker category of software. The browser hijackers are specifically designed to display ads in your browser, redirect you to certain locations on the web and, even change the homepage and/or the search engine of your browser. From that aspect, these programs are nothing but online advertising tools. The more pop-up ads and banners they display and the more you get to click on them while you surf the web, the more money the owners of the browser hijacker make. This is a well-known pay-per-click marketing strategy that is both very commonly used and completely legal.
Phone-notification.com
Phone-notification.com could be distributed via spam emails, torrents, and freeware sites, for example. Nevertheless, there is a more commonly used method to land a program like Phone-notification.com on your device and that is the software bundling. Software bundling is simply of putting together different software and lets the users install it all together with the help of one installation package. Normally, you can download the aforesaid packages free of charge from different free download sites, torrent sites, shareware sites, etc.
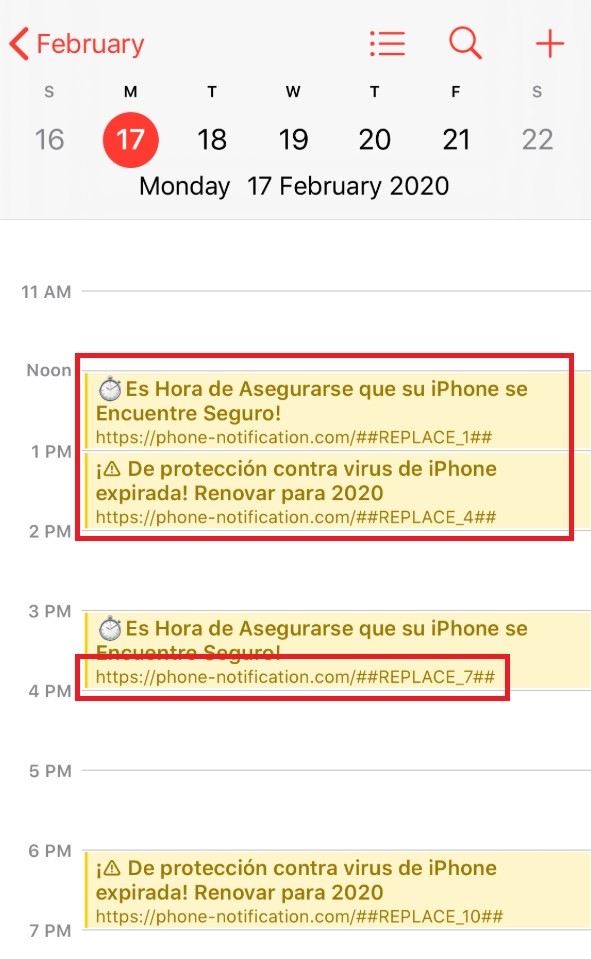
The Phone-notification.com Virus will display pop up ads and messages
If you simply download a software package, however, your device won’t automatically be contaminated with a browser hijacker. The installation of this annoying software happens only when the users run the default/automatic/quick setup and don’t pay attention to the customization options which give them the chance to disable some of the programs in the bundle.
That’s why if you want to keep programs like Iphone-notification.com away from your system, please always select installation options that provide the most information and control over the setup package that you are about to install. Typically, this is the Advanced or the Custom option. Forget the other options –automatic, fast, brief, default – regardless of how they are named, these options will install the entire bundle as it is, including the browser hijacker and some other potentially unwanted applications that may have been placed along with the program you desire.
Fortunately, even if you have installed Iphone-notification.com by mistake, the good news is that this program is not a virus, so you can easily remove it without having to face some serious negative consequences. Indeed, some of you may initially mistake the intrusive browser changes and the aggressive stream of ads as possible symptoms for a virus infection but that is not the case. Real malware like Ransomware or Trojans will not simply interrupt your web browsing with ads. It will encrypt your personal data, spy on you and even destroy the entire system if not removed on time.
The activities that Iphone-notification.com performs, however, are just annoying and not harmful. Yet, it might be a good idea to uninstall this software because you may sometimes be redirected to dubious websites that may contain real malware such as the above-mentioned Ransomware and Trojan horse viruses.
SUMMARY:
| Name | Iphone-notification.com |
| Type | Browser Hijacker |
Remove Iphone-notification.com Virus
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and clean up your phone’s calendar events if they are infected.
2. Find browser extensions related to the threat and how to remove them.
3. Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment