*Ithh is a variant of Stop/DJVU. Source of claim SH can remove it.
Ithh File
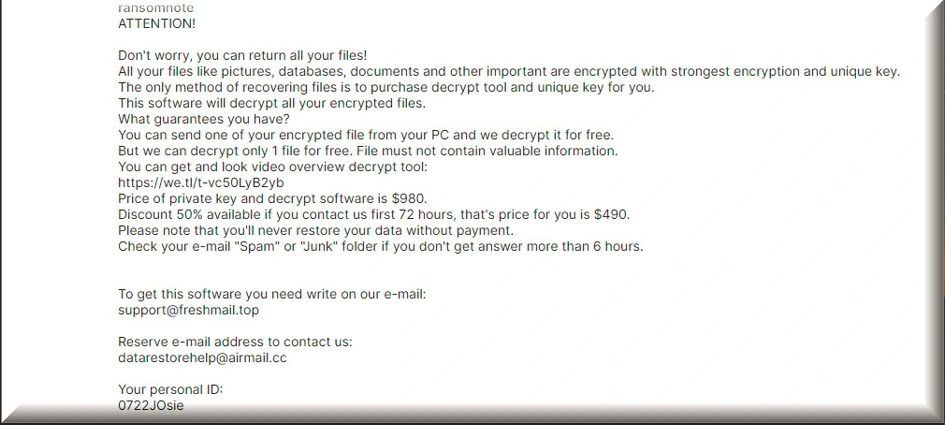
The Ithh file is a new ransomware infection that can wreak havoc on your computer, but knowing how to detect, remove, and mitigate its impact is crucial. Recognizing the signs of the ransomware attack on your personal computer is critical for a timely response. One of the most telling indicators is the abrupt encryption of your files, leading to unfamiliar file extensions. If you encounter difficulties opening files or applications, accompanied by error messages indicating file corruption or inaccessibility, it’s a strong indication of the Ithh file attack. Additionally, be attentive to any ransom-demanding notifications on your screen or inside the folders with encrypted files, as these are messages from the hackers who want a payment.
Decrypting Ithh ransomware files is a complex endeavor, but it is possible in some cases. Certain cybersecurity experts may develop decryption tools capable of unlocking files encrypted by specific ransomware strains. However, it’s important to note that the effectiveness of these tools may vary and not all ransomware variants may have official decryption methods.
How to remove Ithh ransomware virus and restore the files?
Removing the Ithh ransomware and restoring the encrypted files is a challenging process that requires you to consult with cybersecurity experts or specialized self-help resources that may assist you in finding decryption tools for your specific ransomware strain. If you want to effectively remove the ransomware, rely on trusted antivirus and anti-malware software to scan and eliminate the malware. Restoring your files from personal backups is the easiest way to replace the encrypted data.
Ithh Virus
Persional computers can fall victim to the Ithh virus through several common entry points, one of which is phishing emails with Trojanized content. These deceptive emails often contain malicious links or attachments that, when clicked, trigger the Ithh virus download. Another risky behavior that can invite ransomware to your system is when you decide to download software or files from unverified sources, such as unofficial websites and torrents. Neglecting to update your operating system and software can also leave vulnerabilities that ransomware attackers can exploit. Additionally, weak or reused passwords can be a gateway for unauthorized access, facilitating ransomware infections.
Ithh
In the unfortunate event that your personal files become encrypted by Ithh, Ptrz or Ptqw it’s crucial to remain calm and follow a well-structured response plan. Under no circumstances should you consider paying the ransom, as it’s a risky endeavor that may result in the loss of your money. Instead, our recommendation is to promptly report the incident and search for professional assistance from cybersecurity experts or self-help guides and online resources specialized in ransomware recovery that offer trusted decryption tools or strategies. If you have backup copies of your encrypted files, once you clean the infected computer from Ithh, you can use them to restore your data and eliminate the effect of the ransomware attack.
.Ithh
Paying the ransom to recover your .Ithh files is generally ill-advised for several compelling reasons. Firstly, there’s no guarantee that the cybercriminals will provide a functional decryption key, leaving you with no assurance of data recovery despite making the payment. Secondly, paying the ransom directly supports criminal activities and encourages attackers to persist in their malicious endeavors, putting more individuals and organizations at risk. Furthermore, paying the ransom does not guarantee your safety from future attacks, as cybercriminals might perceive you as an easy target for further extortion. Instead of resorting to payment, it’s wiser to search for professional assistance for the recovery of your .Ithh files, and focus on preventive measures.
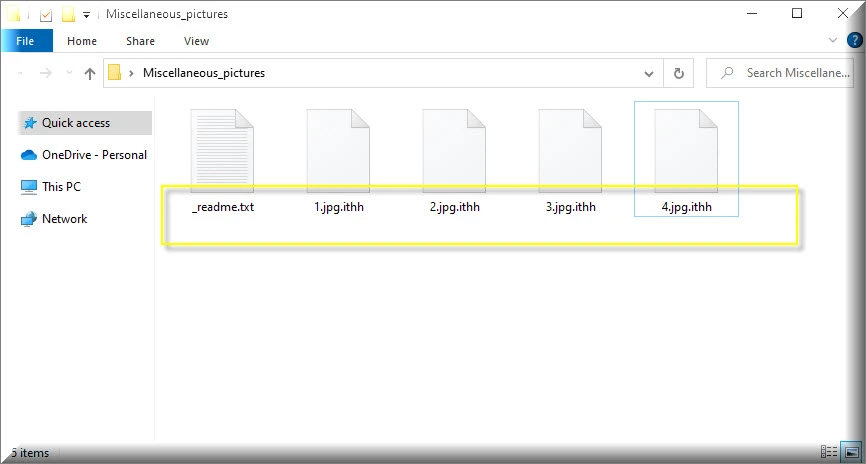
Ithh Extension
The Ithh extension is an extra part added to your files by the Ithh ransomware, signifying that they have undergone encryption and are now inaccessible without a decryption key. It’s important to note that the specific extension added to your files can vary depending on the ransomware variant employed by cybercriminals. Each ransomware strain may use a different extension to identify its victims, making it crucial to recognize the unique extension associated with a particular attack. This diversity in extensions is a deliberate tactic employed by cybercriminals to maximize their anonymity and make it challenging for victims to identify and counter the attack. Therefore, identifying the Ithh extension is a fundamental step in dealing with the ransomware infection effectively.
Ithh Ransomware
An Ithh ransomware attacks is not only unpleasant, but also can lead to identity theft and other cybercrimes. This is because the Ithh ransomware often serves as a precursor to more extensive data breaches. Once cybercriminals gain access to your system, they may pilfer personal data, including financial information and personal documents, which can then be exploited for identity theft or financial fraud. Paying a ransom to cybercriminals can exacerbate the situation by encouraging their criminal activities and doesn’t ensure the safe recovery of your files. Moreover, it might place you on their list of individuals willing to pay, making you a recurrent target for future attacks, thus intensifying the risk of identity theft and other cybercrimes.
What is Ithh File?
An Ithh file is basically a regular file that has been subjected to a process called encryption by malicious software known as the Ithh ransomware. This Ithh file encryption essentially locks the file, making its contents unreadable and inaccessible without the decryption key, which is held by the cybercriminals responsible for the ransomware attack. This can result in data loss, disruption of your daily activities, and putting sensitive information at risk. Paying the ransom is strongly discouraged, as it supports criminal activities and does not guarantee the successful recovery of your files. Instead, focus on prevention through robust cybersecurity practices and regular backups to mitigate the risks associated with ransomware attacks.
SUMMARY:
| Name | Ithh |
| Type | Ransomware |
| Detection Tool |
*Ithh is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Ithh Ransomware

The first thing that you will need to do is a computer restart. Therefore, bookmarking this page in your browser before that is highly recommended and will ensure that you can instantly reload it as soon as your computer reboots.
You should now restart your computer but not in the regular way. Instead, you need to reboot it in Safe Mode to limit down the number of processes and apps only to the most necessary ones. This will make your job of detecting and removing the traces of the ransomware much easier.
Once the system reboots, return to this page for the remaining Ithh removal steps. Click on the Start menu button (bottom left) and type msconfig in the search bar.
After that, press Enter to open the System Configuration window. Then click on the Startup tab at the top of the window.

Then, if you see that Ithh has added harmful Startup Items to the list, you should best remove their checkmark to deactivate them. However, make sure you don’t uncheck legitimate system entries and entries related to your trusted programs. In case of doubt, you can research the startup items online and decide what to do with them based on the information that you discover.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ithh is a variant of Stop/DJVU. Source of claim SH can remove it.
Next, open the Task Manager (CTRL + SHIFT + ESC) and click on the Processes Tab to see whether there are any active malicious processes that might be operating in the background.

This block contains unexpected or invalid content.Attempt Block Recovery
Right-clicking on a suspicious process will open its menu, where you need to select Open File Location. Use the free online virus scanner provided below to check the files of that process for malicious code.

An infected process may be recognized just by the presence of a single potentially harmful file during the scan. As a result, your next step should be to stop the running processes and remove the malicious files from the computer.

In the third step, you’ll need to use the WinKey and R key combination from the keyboard and open a Run window. Inside that window, copy and paste the following line and click the OK button:
notepad %windir%/system32/Drivers/etc/hosts
A file named Hosts will open in Notepad. Make sure you scroll the text of the file down to Localhost and check what is written below. If you see any malicious IP addresses in the file, let us know by leaving us a comment. What you should be on the lookout for is shown in the following image:


*Ithh is a variant of Stop/DJVU. Source of claim SH can remove it.
The most difficult step that will help you to fully remove the ransomware is finding and deleting any dangerous registry entries that Ithh may have added there.
Attention!Inexperienced users should avoid making any changes to the Registry and, instead, use a professional removal tool (such as the one recommended on this page) to clean the system of any malicious files that may be lurking there.
If you still want to use the manual method, start the Registry Editor by typing Regedit into the Windows Search field and pressing Enter.
Next, when the Registry Editor opens, press CTRL and F together and type the name of the ransomware in the Find window. After that, click the Find Next button. The Registry should then be searched for entries with that name, and if any are found, they should be deleted since they may be connected to the virus.
Checking a few more system locations where malicious files might be hiding is also a good idea. We recommend you type the following lines into the Windows Search Field one by one and search them for items that were created around the time the ransomware attack occurred:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in the Temp folder, and keep an eye out for suspicious-looking files or subfolders in the rest of the locations.

How to Decrypt Ithh files
In order to recover from a ransomware attack, great attention must be given to the ransomware variant that has infected you, as the methods needed to deal with it may be different. The extensions added to the files encrypted by the ransomware might help identify its variant.
First, however, you need to make sure that the ransomware infection has been completely eliminated from your machine. We recommend you to use the manual removal guide provided above, a professional anti-virus program, an online virus scanner or a combination of all of the above, to ensure that Ithh has been completely removed from your computer.
As far as your encrypted files are concerned, there is a program below that may help you recover your data if Ithh is the variant that has infected your computer.
New Djvu Ransomware
STOP Djvu, a new strain of the Djvu Ransomware, is attacking people in a global scale. The .Ithh suffix makes it easier to identify this particular variant from other malware that use the same technique.
As we all know, new variants of ransomware may be extremely difficult to deal with but, there is still hope if an offline key was used for encryption of the files encoded with Ithh. What is more, there is a decryption tool that you may use to try to recover your data. You may download the decryptor to your computer by clicking the link below and then clicking the Download button on the page.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
The decryption process
Run the decryptor as an administrator and hit the Yes button to start the file. Take a few minutes to through the license agreement and the instructions on the screen before moving further. Next, click the Decrypt button in order to decrypt your information. Please be aware that files encrypted with unknown offline keys or files encrypted online may not be decrypted by the program.

Leave a Comment