This page aims to help you remove Jorge Rimac Email Virus. Our removal instructions work for every version of Windows.
Jorge Rimac
Jorge Rimac email is another example of so-called sextortion email.The cybercriminals behind Jorge Rimac’s email claim to have personal information or naughty videos of the affected user and require payments in cryptocurrency to prevent them from being made public.
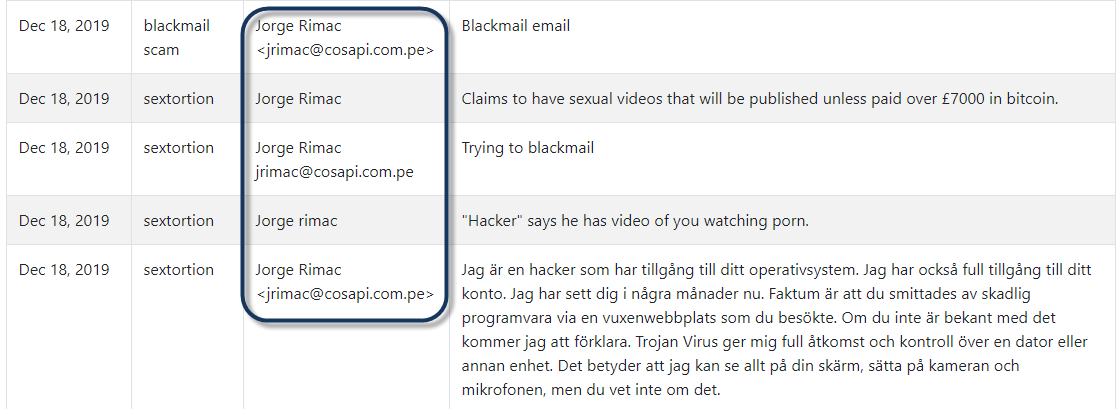
Jorge Rimac hacker scam complaints
There are a lot of different Trojan horse infections but the common thing between them is that hackers use them to stealthily invade the systems of web users and initiate various malicious activities in them. The Trojans’ methods of infection are very sophisticated and typically invisible. Web users may get infected from software packages that have been injected with the Trojan’s malicious code, or from spam email messages, attachments, and malicious links. In addition, some Trojans are also known to exploit any vulnerabilities in the operating system and/or in the software that has been installed on it. That’s why investing in a reliable antivirus program is still one of the best ways to keep your system safe from threats such as Jorge Rimac. If you have already been infected, however, stay with us because, in the next lines, we will tell you what to do so as to safely remove this malware from your computer.
What can a Trojan horse be used for?
One of the most problematic characteristics of the Trojan threats is that they can be used for different malicious purposes and in many different ways. For instance, a threat like Jorge Rimac can serve as a tool for targeted system corruption. It can locate and corrupt specifics files stored on your computer and even delete important system files that can lead to total OS destruction.
Besides, a Trojan like this one may function as a data collection tool under different circumstances. It may secretly collect information about your location, your online and offline activities and even capture screenshots of the things on your screen. On top of that, this malware can keep track of your keystrokes every time you type your passwords, login information, credentials to bank accounts, and other sensitive information and then transfer those records to remote servers controlled by hackers.
One of the most frightening abilities of the Trojan-based infections is to spy on their victims. Once inside the system, such threats can turn on your web camera and microphone without your knowledge and basically share all your conversations with the hackers or capture embarrassing videos and audios of you which can later be used for blackmailing and even physical abuse. But probably the worst of all possible uses of the Trojans is for the distribution of other malware. An infection like Jorge Rimac can secretly invite a Ransomware, a Spyware, or another virus inside the already compromised computer by acting as a backdoor to the system. That’s why the moment you detect a Trojan on your system, you should immediately remove it before it has managed to insert other infections or perform some of the above-mentioned activities without your knowledge. If you don’t know how to safely remove Jorge Rimac, the guide below contains all the necessary steps, as well as a professional security tool for a full system check.
SUMMARY:
| Name | Jorge Rimac |
| Type | Trojan |
| Detection Tool |
Remove Jorge Rimac Email Hacker Scam
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment