.Kasp
.Kasp is sophisticated malicious code, focused on extortion. .Kasp operates as a ransomware cryptovirus and tries to block you from accessing your data through encryption and pressures you to pay a ransom for decrypting the information.
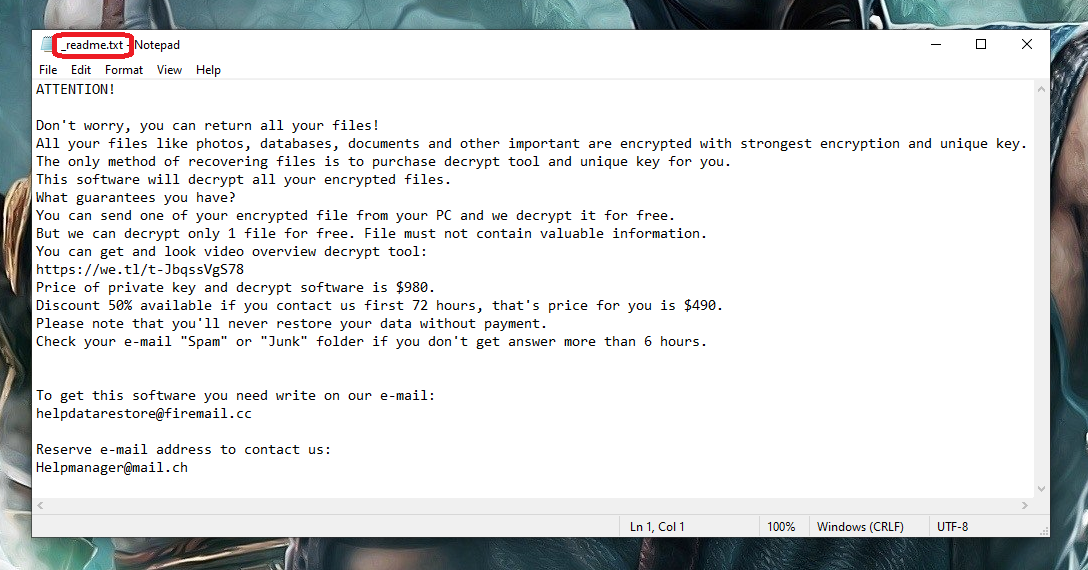
Once the .Kasp virus has encrypted your files it will create a _readme.txt file.
Ransomware infections like this one are notorious for getting distributed through illegal websites, Trojan backdoors, spam messages and pirated software. The most problematic and dangerous aspect of these infections is their ability to block the user’s access to their files or the entire system! After encrypting the machine or the files stored on it, this type of viruses may request a ransom from the victim by displaying a ransom notification. If you don’t want to pay the ransom demanded by the hackers, you should be ready to lose access to all the encrypted files or explore some alternative solutions.
The .Kasp virus
The .Kasp virus is an advanced ransomware threat categorized as a cryptovirus that targets user and system files. A computer infected with the .Kasp virus will have all its data locked with a secret encryption algorithm that can only be reversed with a special decryption key.
.Kasp and the other malicious programs based on Ransomware are distributed across the web in a variety of ways. Users should be particularly careful about these infections as they may be delivered through different spam emails and their attachments, or through social network spam posts. The so-called malvertising is another common method for distribution of these malicious apps. Some websites may have advertisements that lead to malware-infected pages and, if you click on these ads, you may get your computer infected by the ransomware virus without knowing it.
The .Kasp file encryption
The .Kasp file encryption is a special process of data protection which encrypts the file and renders it inaccessible to everyone who does not have a matching decryption key. Typically, the hackers behind the .Kasp file encryption virus offer to send you that key if you pay a ransom for it.
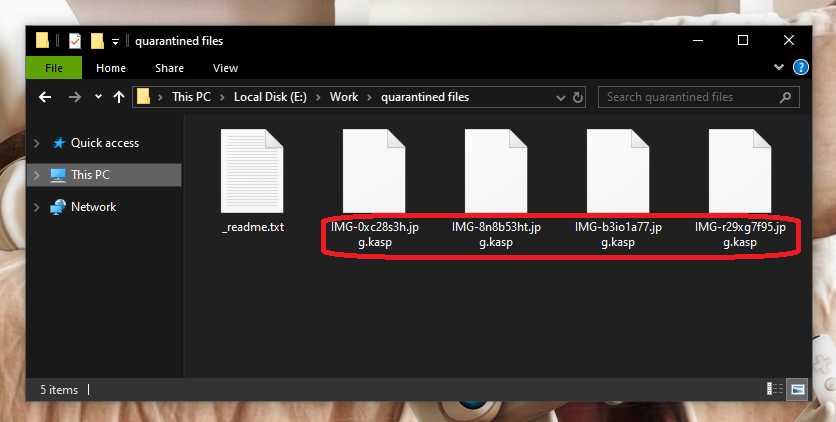
The .Kasp File encryption will begin as soon as it has infected your system.
Many victims of ransomware seek easy way to remove the virus and recover their encrypted files. Unfortunately, there is no universal solution that can guarantee a full recovery from the attack of the ransomware. Yet, there are some methods that may help you avoid the ransom payment and get back some of your files for free. That’s why, most security experts advise victims of threats like .Kasp, .Domn and .Geno to explore the available alternatives before even considering the ransom payment as an option.
In the removal guide below, we have listed some of the alternative solutions which you can try if you have been infected with .Kasp. As far as removing the ransomware is concerned, in the guide there is a link to a professional removal tool that can handle the infection quickly and safely.
Keep in mind that your strongest weapon in the fight against malicious software and viruses of this kind is the good old prevention. That’s why if you want to save your files from a possible file encryption, make sure you create backup copies that are stored on an external drive, cloud or another device. In this way, nobody is ever going to harass or blackmail you for your file access.
SUMMARY:
| Name | .Kasp |
| Type | Ransomware |
| Detection Tool |
.Kasp Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment