This page aims to help you remove the Kensaq Virus. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
The infamous ad-generating browser hijacker software type has recently had yet another representative added to its family. In this case, the name of the offender is Kensaq and we are here to tell you all you may need to know about it and also help you uninstall this app from your computer if that is what you are looking to accomplish.
The Kensaq Virus
Kensaq is regarded as a type of a browser hijacker. Threats like Kensaq are known to cause different problems like changing of the user’s designated home page or even the preffered browser of choice.
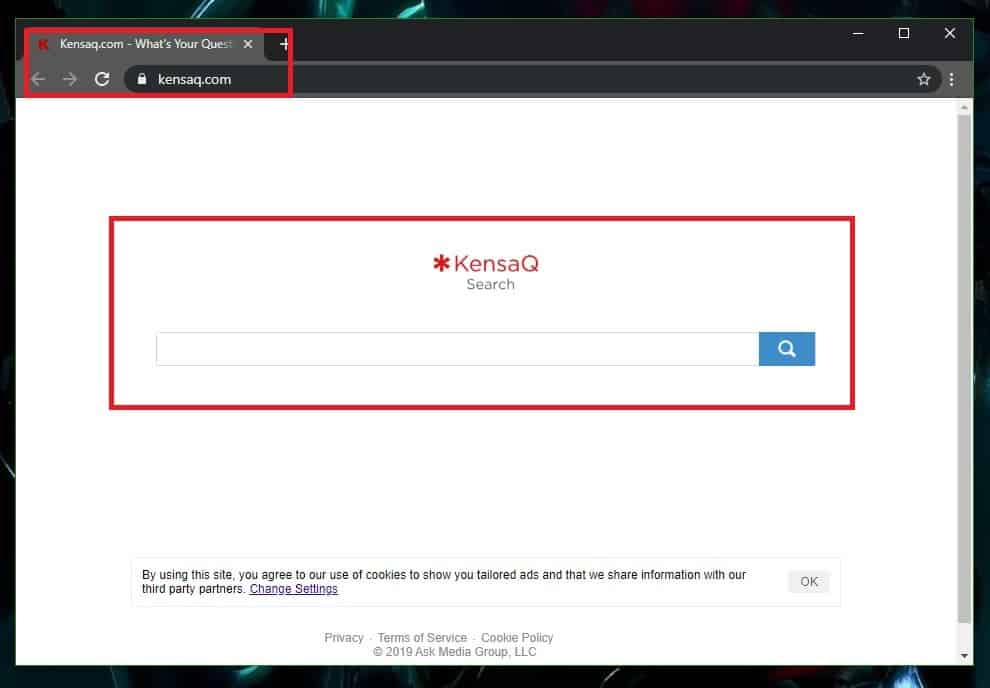
The Kensaq Virus will redirect your browser when you try to use it.
First and foremost, we need to start with the basics by telling you what a browser hijacker like Kensaq truly is. Is it a nasty virus like a Ransomware or like a Trojan Horse or is it just some regular program that just gets rap? Well, though there are different opinions on that, we’d say that Kensaq and hijackers in general are neither. They are apps that get attached to Chrome, Firefox and other browsers and add to them new homepages, new search engines and page-redirect services in order to accumulate money through advertising activities. In some cases, a browser hijacker (also called browser-redirect) may be presented to the user as some useful tool that they’d definitely want to add to their browser. And indeed, some browser hijacker-like apps may truly come with somewhat helpful features. However, the truth is that, in most instances, this category of software is seen as potentially unwanted by most experts in the field. The reason is, of course, the obnoxious ads and the oftentimes unwelcome changes in the browser that most hijackers impose without even consulting the user or asking about their agreement. Naturally, most users wouldn’t be happy with the presence of an app in their browser that does all this and doesn’t even provide an option to cease the irritating activities. That is precisely why we’ve made sure to give our readers a way out of this situation by adding a removal guide for Kensaq to this short write-up:
The Kensaq Search
We already pointed out that it cannot really be said that a hijacker app like Kensaq, that is more of an annoyance and not something more dangerous, is a virus or a software piece that can be compared to Trojans, Spyware, Ransomware and other highly dangerous and problematic malware categories. However, we also said that the hijackers aren’t exactly the same as regular programs and keeping such software in your computer may not be the best idea. Aside from the irritation coming from the banners, redirect, ads and, of course, the unauthorized modifications in your browser, you must also bear in mind that it may sometimes be risky to allow such software to freely operate in your system. You cannot know if the next ad displayed on your screen or the next page that Kensaq suddenly decides to redirect you to will not actually be linked with some hazardous site that may threaten the security of your machine. That is why we always try to emphasize the importance of quickly removing apps like Kensaq from the computer in order to prevent them from potentially showing unreliable content in your browser that may compromise the state of your online safety and privacy.
SUMMARY:
| Name | Kensaq |
| Type | Browser Hijacker |
| Detection Tool |
Kensaq Virus Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment