*Kitz is a variant of Stop/DJVU. Source of claim SH can remove it.
Kitz
Kitz is a malicious program that employ the process of encryption as a means of making targeted users incapable of accessing their own personal data stored on their computers. Kitz is categorized as ransomware is currently one of the most widespread ransomware cryptoviruses.
As you may already know, the process of data encryption is typically used to secure important files and render them inaccessible to anyone who is not authorized to have access to said files. Once the targeted files are locked through encryption, only users who have the unique secret decryption key for those files are able to open them, edit them and use them.
Now, this could be really helpful if your work involves handling sensitive and important data which you may need to keep safe and protected from unauthorized access of any form. However, there is actually a way to turn this otherwise very useful process of data protection against the users. You have likely already heard about ransomware – a malware category that is mainly used for money extortion and blackmail. One of the most advanced subcategories of ransomware are known as cryptoviruses, to which Kitz, Kifr or Kiwm belongs.
The Kitz virus
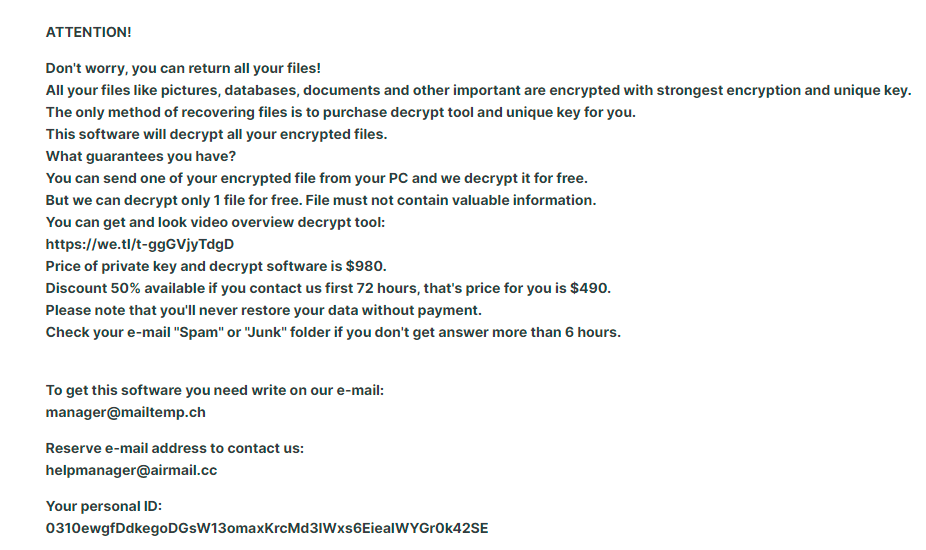
Once the Kitz virus enters your PC and detects what files you have on it, it would launch an encryption process that ultimately results in the full lockdown of the targeted files. Once that part of the malware attack is finished, the Kitz virus shows you a note that contains instructions on how to pay a certain amount of money to the hackers.
The money is required in order to “purchase” the decryption key for your files. Now, we do not advise you to do that in case Kitz or another ransomware has invaded your computer since you may simply waste the money and not get the correct (or any) decryption key. Instead, we recommend that you take a look at the removal instructions for Kitz down below and follow them to eliminate the infection.
The Kitz file
Once the Kitz file is removed, you will be once again able to use your computer safely, without worrying that any new files you create may get encrypted. The problem, however, is that the already encrypted data is likely to remain sealed even if the Kitz file is removed.

To unlock those files, you will need to take additional steps and this part is probably going to be rather tricky. You see, each cryptovirus is different and uses different encryption so what works for handling one ransomware virus may not work for another one. We have posted some general data recovery suggestions on our site that you can use for free but we can’t guarantee that they will be successful in all of the cases and for all of our readers. Nevertheless, we must still remind you that trying the alternatives is preferable since you would at least not be risking your money by paying the ransom to anonymous criminals who may easily decide that they will not actually send you the key that can unlock your data.
SUMMARY:
| Name | Kitz |
| Type | Ransomware |
| Detection Tool |
*Kitz is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Kitz Ransomware

If you want to successfully remove ransomware from your computer, you must follow the instructions in this article to the letter. First and foremost, make sure any external storage and USB drives connected to the infected computer are unplugged. After that, disconnect your computer from the Internet so that the ransomware cannot communicate with the malicious servers.
A good suggestion is to save this removal guide in your browser since your computer will need to be restarted, so you can easily return to where you left off by clicking on the bookmark. You can also open this Kitz removal guide on another device and follow the steps from there instead if that’s an option for you.
We also suggest restarting your computer in Safe Mode to guarantee that the removal process is completed in the most effective manner possible. To restart your computer in Safe Mode, click this link and then follow the on-screen instructions that appear. Upon rebooting the computer, return to this page and continue with the following steps.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Kitz is a variant of Stop/DJVU. Source of claim SH can remove it.
When you’re done with the first step and the computer has restarted in Safe Mode, open the Task Manager on the infected system and click on the Processes tab. Take a look at the list of currently running processes, and then sort them according to how much memory or CPU they use. Right-clicking on a process that looks suspicious and selecting Open File Location from the context menu, as seen in the image, will allow you to see the files related to that specific process:

Drag the contents of this folder to the scanner to check whether it includes any dangerous files that need to be removed:

To delete any potentially harmful files from the folder, you must first end the currently running process (Right-click on the process>>>End Process). You may then delete any files that have been marked as potentially harmful to your computer.

After pressing the Win key and R key simultaneously, type the following command in the Run box and press Enter:
notepad %windir%/system32/Drivers/etc/hosts
Notepad should open a file named Hosts on the screen. As soon as you see it, search for any IP addresses under “Localhost” that don’t look trustworthy and take note of them. Post any suspicious IP addresses in the comments section below, and we will let you know if there is anything you should be concerned about.

The System Configuration window is also a good location to check for files related to Kitz. To do that, go to Windows Search, enter “msconfig” and hit Enter. After that, look at the “startup” tab to see what items have been ticked.
Any startup items that you believe are related to the infection should have their checkboxes removed to prevent them from running at startup. If you’re unsure about anything, it’s always best to conduct some online research first.

![]()
*Kitz is a variant of Stop/DJVU. Source of claim SH can remove it.
Malicious software often hides its components in the registry, enabling it to remain on a computer for an extended period of time. Viruses may be prevented from being completely deleted and subsequently reinstalled by utilizing files from the registry when a system is restarted. If there are files that are connected to Kitz in the registry, you must delete them using the Registry Editor. Type regedit in the Windows search box and press Enter to open it.
You may use the CTRL and F keys on your keyboard to launch a Find box in the Registry Editor and search for files that are associated to the infection. To begin your search, type the threat’s name in the Find box and choose Find Next.
Attention! Inexperienced users may have difficulty removing ransomware-related files from the registry. Incorrect deletion of registry entries, on the other hand, might impair the general performance and stability of the system. That’s why, non-technical people who think their computer is infected with Kitz and want to remove it should use a virus removal application. An anti-malware program like the one on this website is a good option for protecting a computer against such threats.
As a precaution, you should also manually check the following places on your computer for additional ransomware files. Press Enter after typing each one’s name in the Windows Search bar.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Inspect the folders listed above carefully, but don’t delete any files unless you’re sure they’ve been compromised. Your computer will be free of any temporary data if you go inside your computer’s Temp folder, select everything, and then click the delete key on your keyboard.
![]()
How to Decrypt Kitz files
When dealing with data encrypted by ransomware, even specialists may sometimes find it difficult to decode the data. That’s why, when it comes to dealing with ransomware, inexperienced users may have a difficult time since the decryption methods used by different versions may vary. Because of this, it is vital to know which ransomware variant you’re dealing with. Look at the file extensions of the encrypted data to figure out what variant of ransomware has attacked your machine.
If the ransomware is still on your machine, it will swiftly encrypt any data you may be able to retrieve. Therefore, data recovery should not begin until the system has been properly checked for dangerous software, ideally with the assistance of professional anti-malware software.
New Djvu Ransomware
STOP Djvu is a new variant of the Djvu ransomware that is extorting money from its victims by decrypting a variety of files on the infected system. The .Kitz suffix is commonly added to the end of the files encrypted by this threat, and is a good indicator of the variant of ransomware that has attacked you. Using a decryptor, like the one listed below, may be an option to retrieve some of your data, especially if you’ve ensured that your computer is virus-free.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Read the license agreement and any instructions that come with your STOPDjvu executable file before decryption may begin. Remember that this program’s ability to decrypt your data is not guaranteed, particularly if the files were encrypted with an unknown offline key or an online encryption.
Antivirus software may be necessary if the manual techniques outlined in this page fail to completely remove Kitz. Any file you’re worried about may be manually scanned for viruses using our free online virus scanner. You can also leave a comment if you have questions regarding anything in this guide, and we’ll respond as soon as we can.

Leave a Comment