Koti
Koti is what is identified by cyber security experts as a file-encrypting ransomware variant. This means that Koti applies encryption on the files of its victims to make them inaccessible.
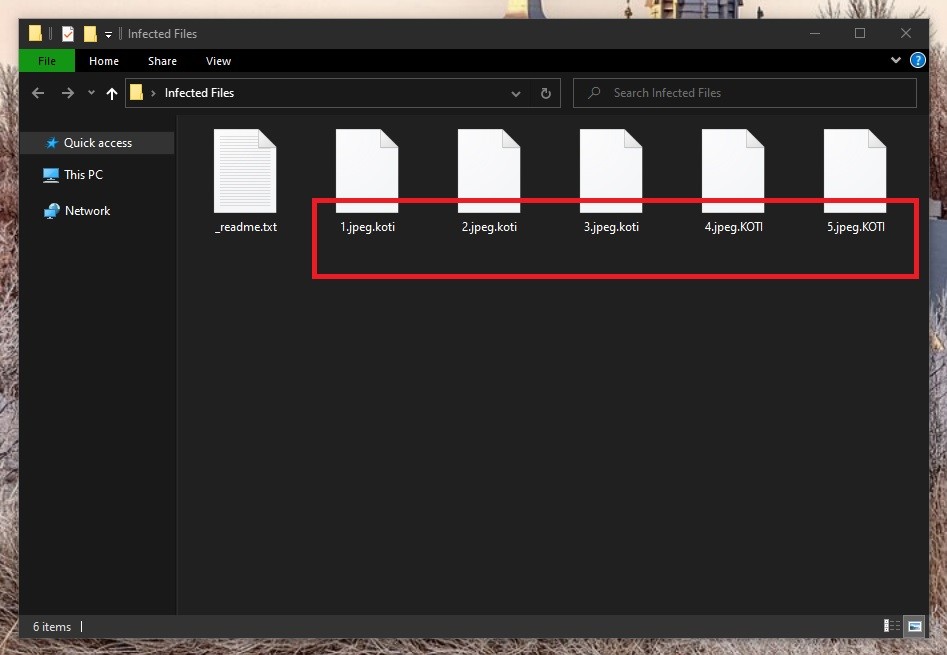
The KOTI virus file encryption
The idea here basically revolves around a classic blackmail scheme, in which the victims’ files are held hostage in demand for a certain amount of money as ransom. Hence, the name of this malicious software category. The files are in essence rendered unreadable to any type of software, and therefore once they’ve been encrypted, unless you’re in possession of a special decryption key, you won’t be able to use them.
In turn, this decryption key is what the criminals behind the ransomware promise to send their victims after they’ve complied with the ransom demands. However, whether or not they will indeed send you a key once you’ve paid them is still questionable. It certainly wouldn’t be unprecedented for the hackers to vanish and you to never hear from them again. And in some instances, even if you are sent a key, there’s no telling whether or not it’s the correct one. Each instance of encryption requires its own unique key, so mixups can and do happen.
With this in mind, it’s a much better idea to try and resolve this problem using alternative measures. For one, removing Koti is of crucial importance – regardless whether you choose to deal with the hackers or not. This will ensure that at least no new files or potentially recovered ones get encrypted henceforth.
But after you have taken care of this, there are a number of ways in which you can try to get ahold of your locked data. We’ve put together a detailed removal guide just below this post to help you effectively eliminate this ransomware virus. And in the second part of the guide, we have also included these alternative file recovery methods that you can try.
The Koti virus
The Koti virus is a malicious piece of software that is capable of working under the radar of most antivirus programs. The encryption used by the Koti virus is essentially not harmful and therefore it usually won’t trigger your antivirus software.
Furthermore, some of the more advanced ransomware versions can actually even disable your antivirus program – just to make sure that it won’t interfere with its dirty business. This, as well as the complexity of the encryption itself, has greatly contributed to ransomware being considered the most dangerous type of malware out there. And with the rates at which ransomware is growing in popularity, it’s up to each and every user to do everything in their power to withstand it.
Namely, try avoiding such infections by staying away from their probable sources. These mainly include pirated software, spam messages and fake online ads. But even more importantly, keep backups of your valuable files on a separate drive or cloud.
The Koti file extension
The Koti file extension is visible at the end of each encrypted file name. The Koti file extension is pretty much what ensures that no software can recognize the data format.
SUMMARY:
| Name | Koti |
| Type | Ransomware |
| Detection Tool |
Remove Koti Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Hi, I watched the video, and I have a couple of things that I would like you to help me with.
First, the startUp application you used to delete files I can’t find it in the search so I deleted them by searching everywhere and deleting recent files
Second, when i opened regedit.exe I couldn’t find the windows -> rename file “I couldn’t find it”
Third, at the last step when you reopen the device, when it opened the same errors where still there and my windows defender can’t remove these errors
Forth, so when I checked the damaged files nothing has changed
Question 1:what should I do next
Question 2: would formatting the local disks actually remove the virus without re-downloading new windows
P. S. My windows is 10 pro
And thank you for your consideration
Hi Doaa Abo-Alia,
One of the ways to find the startup folder is by opening the Run dialog box by pressing Windows key + R and after that type this exact line and click OK: shell:common startup
When you get to Regedit.exe you can open a search bar by pressing Ctrl + F to find the locations you need to check. Navigate to the directory shown in the video and while you are on that part a blue pop up will appear listing more locations you have to check by using the search bar.
By formatting any hard drive not containing your Operating System (OS) you will only lose your personal files which are encrypted and the virus will remain in your PC. For now the best thing you can do is remove the ransomware virus from your OS and transfer your encrypted files to a different hard disk to wait for a decryption tool to be released so you can try and recover them.
Please let us know if this information was helpful.