*Kruu is a variant of Stop/DJVU. Source of claim SH can remove it.
Kruu
Kruu is among the most dangerous viruses that you can possibly land. Kruu belongs to the malware category of ransomware and can prove to be incredibly harmful. You may have discovered the Kruu virus on your computer only after it displayed the notorious ransom note on the screen of your PC.
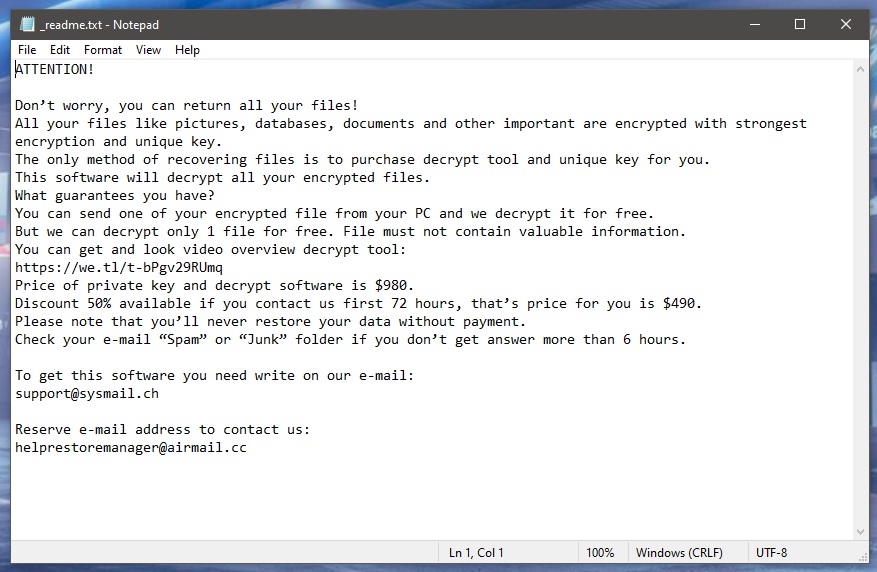
If so, then unfortunately it has already managed to complete the process of encrypting your most precious files and now you are faced with the consequences.
Ransomware like this can encrypt pretty much any file types, including images, audio and video files, documents, etc. The scheme is as simple as it is ingenious. The hackers behind ransomware viruses such as Kruu, Xcvf, Bbnm blackmail users into paying money so as to have their data decrypted. And normally, to make the “offer” more convincing, they don’t shy away from various scare tactics. For instance, you may have been threatened with a deadline after which the criminals promise to destroy the decryption key or even permanently delete your files.
What does one do in a situation like this? We would recommend exploring alternative file recovery options, such as the ones we have listed here. But whatever you do, the first and most important thing you must undertake is the removal of this malware. We have a set of specific removal instructions available for you just below this article.
The Kruu virus
The Kruu virus is extremely dangerous because of the complexity of its encryption. And that same encryption is what makes the Kruu virus immune to almost all antivirus software.

The thing is that the encryption process itself does not damage the files and is not in itself a malicious phenomenon. On the contrary, it is actually a security measure employed for data protection. But a handful of hackers have found a way to use this for evil.
This, along with the fact that the criminals enjoy full anonymity, has sparked a whole ransomware epidemic. Millions of variants just like Kruu are released every year and a very insignificant percentage of those are ever exposed and stopped. It’s a very lucrative criminal scheme that, unfortunately, still remains ahead of the cyber security game.
.Kruu file decryption
As complex as the ransomware encryption is, the .Kruu file decryption is more complex yet. There are no guarantees that the .Kruu file decryption that the hackers promise will work.
And with that in mind, it’s a good idea to leave the ransom payment as a last resort. Not to mention that the hackers may simply forget about you altogether even after you’ve paid.
But even if you do decide to go down that path, it’s vital that you first have Kruu removed from your system. Otherwise you will risk losing any decrypted or new files to the virus again – and this time probably for good. After that you can try to recover your files from system backups or from a cloud or external drive, if available. In addition, there are decryptor tools out there that may be able to help as well.
SUMMARY:
| Name | Kruu |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Kruu is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Kruu Ransomware

As the first step in this guide, please save these Kruu removal instructions in your browser as a bookmark. In this way, you don’t have to keep looking for the removal guide after each reboot of your system. Also, restart your infected computer in Safe Mode, so that only the most essential processes and apps are running before moving on to the next step.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Kruu is a variant of Stop/DJVU. Source of claim SH can remove it.
By pressing CTRL+SHIFT+ESC on your keyboard, you can start the Task Manager. Next, click on the Processes tab and manually check your system for processes that are not associated with any of your regular programs, as well as those which hog a large portion of your system’s CPU and RAM resources for no clear reason. When a suspicious process is right-clicked, select Open File Location from the pop-up menu to view its files.

Check any suspicious-looking files for malware using the free online virus scanners listed below.

Delete any potentially harmful files that were found during the scan. However, before deleting any files, use the quick menu to end the suspicious process by right-clicking on it and selecting End Process.

To complete the third step, you need to type msconfig in the Windows search bar and hit Enter. Once you’ve done that, System Configuration will open on the screen. Using the Startup tab, you’ll be able to see what apps are already running on your computer. It’s your responsibility to disable any Kruu-related startup items by removing their checkmarks.

The Hosts file can also be altered maliciously on a compromised computer. Therefore, after you are done with the settings in System Configuration, open the file and look under “Localhost” to see if any of your IP addresses are listed there.
Hosts can be opened by pressing Win and R at the same time, then typing the following in the Run box.
notepad %windir%/system32/Drivers/etc/hosts
After you paste the line above in the Run box, hit Enter and, if you notice any suspicious IP addresses in the file under Localhost, please notify us immediately. These IPs will be checked by a member of our team to see if they pose a security risk.


*Kruu is a variant of Stop/DJVU. Source of claim SH can remove it.
Malware authors are becoming more inventive in their efforts to evade detection by anti-malware programs, thus, they commonly insert harmful registry entries into the system. The Registry Editor can be used to see if any harmful files have been added to your registry. This can be accomplished by typing “Regedit” in the Windows search bar and pressing the Enter key. If your computer has been infected by ransomware, type its name in a Find box (CTRL+F) in the Registry Editor and then click Find Next to search for files associated with the virus.
Remove all search results that have a relation to the ransomware. The registry can be searched again for other files with the same name once the first result has been removed.
Attention! If you mistakenly remove non-ransomware-related files while clearing the registry, your operating system may be damaged. That’s why it’s important to use a trusted anti-virus program to remove potentially dangerous software and registry entries from your computer.
It’s also a good idea to check the following locations manually for any malicious entries. Type each one in the Windows search bar exactly as shown below, and press Enter to open it:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
If you find any suspicious files in these locations, remove them immediately. To clear out your Temp directory of all temporary files, simply press CTRL and A and press the Del key on your keyboard.

How to Decrypt Kruu files
Those who have had the ransomware removed must deal with the challenge of getting back their encrypted files. Depending on the type of ransomware that has infected your computer, the methods used to decrypt your data will also differ. By looking at the file extensions that are added to the encrypted files, ransomware variants can be easily detected.
Prior to any file recovery attempts, an anti-virus scan of the infected computer should be performed with a professional malware removal program (like the one on this page). If the scan finds no danger and confirms that you have a virus-free and ransomware-free computer, you can then test on on various file recovery methods and even connect your file backup sources.
New Djvu Ransomware
STOP Djvu, a new Djvu ransomware variant, has recently been discovered by experts. This new variant stands out from other types of malware by adding a special suffix of .Kruu to the encrypted files. Fortunately, an offline decryptor like the one at this link below can be used to decrypt encrypted files.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Click on the STOPDjvu.exe file and select “Run as Administrator” after downloading it from the link above. To begin decrypting your data, go over the license agreement and any brief instructions that came with it. Please be aware that this tool is unable to decrypt files that have been encrypted with unknown offline keys or online encryption.
If you find yourself in a bad situation, the anti-virus software on this page can quickly and easily remove the ransomware. You can also check your computer for suspicious files using a free online virus scanner.

Leave a Comment