.Kvag
The .Kvag Virus is a very malicious cryptovirus part of the DJVU Ransomware family aimed at extorting money from you, much like Moka and Meds. .Kvag reveals its presence by displaying a ransom-demanding notification on the screen of its victims. If you have been seeking a way to remove this infection from your system and avoid the ransom payment the malware requires, you have come to the right page. And although this is one of the stealthiest types of malware, our “How to Remove” team would do its best to assist you with the removal of the infection. We’re even going to offer you some suggestions on how to restore some of your information without needing to send your money to the criminals responsible for all this.
The .Kvag virus
The .Kvag virus is an infection that can sneak inside your computer without being noticed. The .Kvag virus silently launches its file-encryption, and reveals itself with a ransom note after the encryption has been completed. Viruses like Kvag are undetectable for most security programs due to the specifics of the process they employ to complete their agenda. The Kvag file encryption isn’t something that will corrupt or delete the files – it simply locks them, but the files remain intact. Most antivirus programs are rarely suited to spot this kind of file-locking activity.
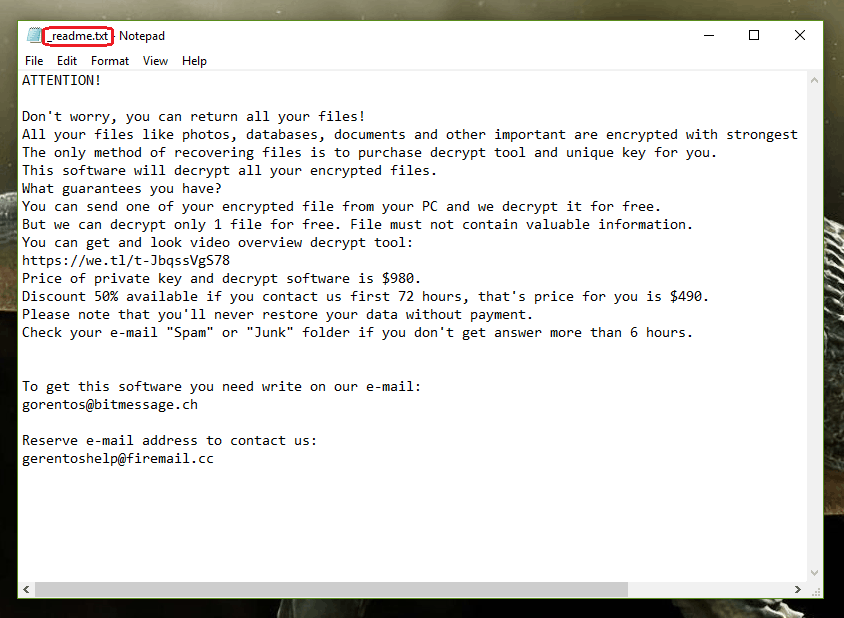
The .Kvag Virus will leave this message in a _readme.txt file when it is done encrypting your files.
Generally, the Ransomware infections are some of the most advanced forms of malware on the web. The hackers conceal them by using multiple social engineering techniques in order to infect as many users as possible. A Trojan Horse may sometimes help the Ransomware to discover a weakness in your system, and sneak in quietly. Malvertising and spam emails are also some of the most effective methods the hackers use to infect a large number of people, so clicking on such sketchy materials is not a good idea. Unfortunately, it is oftentimes difficult to predict if a given piece of content is safe or if it’s potentially hazardous, which is why you should generally stay away from sites that aren’t verified as reliable.
The .Kvag file encryption
The .Kvag file encryption is a special secret code that keeps your files inaccessible. The .Kvag file encryption can be decrypted using a special key, which is possessed by the hackers, who want you to pay for it. The encryption process used by threats like Kvag is what sets Ransomware from most other forms of malware. The Kvag Ransomware won’t damage the files it targets with its encryption and this helps it stay under the radar of many popular antivirus solutions. Although the files become inaccessible, they are left intact by the virus.
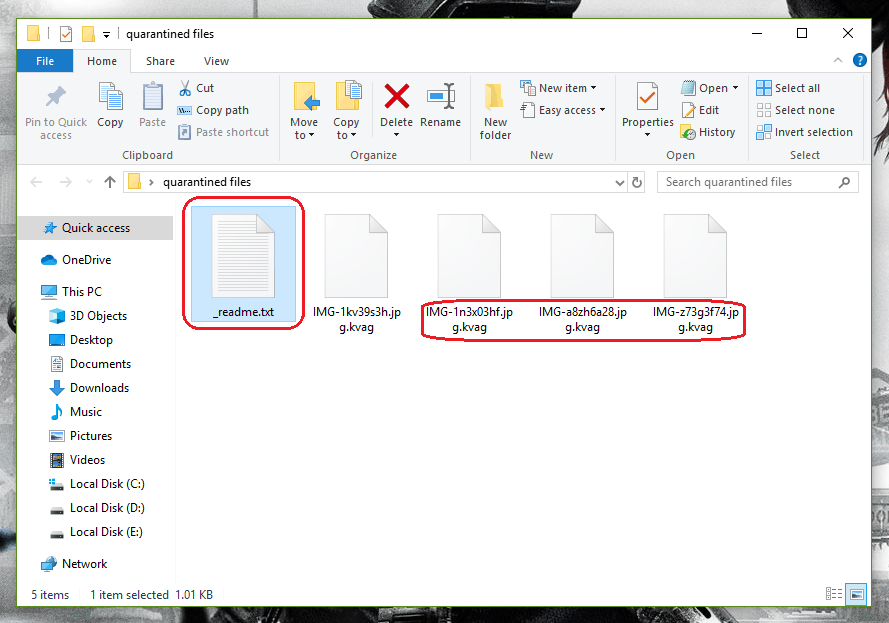
A screenshot of an encrypted .Kvag File.
When all the file encryption work is done, the hackers behind .Kvag do their best to provide you with sufficient information about exactly how you are supposed to pay them the ransom. On the screen of the infected computer, as well as in any folder with encrypted documents, you will discover a ransom note. Some hackers may even bring it to the next level, and launch a vocal message that can be very annoying. All this is done with the intention of intimidating the victims, and making them pay without much thinking.
How the .Kvag Ransomware Works
The .Krag ransomware, aside from actually encrypting your files and asking for ransom, also employs a trojan horse that can track your movements – including your contacts. With this, the .Krag ransomware can infect whoever you send files to. Avoid doing this.
You’ll most probably be promised to get a decryption key in order to restore your files right after you make the transfer of the ransom, but this is an “option” that often leaves the victims with nothing but empty pockets. And since the payment is generally given in Bitcoins, an untraceable online currency, the possibility of getting your money back is null.
As far as the decryption key is concerned, in many cases, there is nothing that could make the hackers send you the decryption key once they get the money. In fact, there are already a number of victims who have burned their money this way, and have been left with their files encrypted for good.
If you don’t want to be one of them, however, there is another alternative. We suggest you take the things into your hands and handle the infection on your own. You can start by following the instructions in the removal guide below, focusing on how to remove .Kvag first, and then exploring the file-recovery section, where potential alternative solutions can be found.
SUMMARY:
| Name | .Kvag |
| Type | Ransomware |
| Detection Tool |
.Kvag Virus Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

i want a free data recovery tool for .kvag virus ransomware please answer my questions
hi do you have a decripting tool for the files of kvag virus
I cannot solve my computer problem effected by Kvag virus all my file are extended. So i need help.
I found additional ip addresses, what do I do?
Send them here so that we can confirm they need to be deleted from the Hosts file. In general, there shouldn’t be any additional IPs there.
I have done according to this instruction but my problem still cannot solve.
Help me
If you are talking about the file-recovery, try the instructions from our How to Recover Ransomware guide.
Hello, I’ve founded some virus creator IP’s after run ‘regedit’ and ‘notepad %windir%/system32/Drivers/etc/hosts’ .
But now i don’t know how to remove then. Can you help me please?
Thanks!
Simply delete the IPs as you would delete normal text and save the changes. For the Registry entries, right-click on the entry, and then select Delete. Keep in mind, though, that you need to use an Administrator profile to accomplish that.
my files have extention kvag and can not open – i deleted the virus but but i can not repaier my file my file
please
if anybody know say to us
my email yasinazarshab@ yahoo. com
dear admin pleas accept this comments in ur website
tnx so much
it was too many file i found after searching appdata. should i delete them all?
In Appdata, only delete files that have been created after the malware infected your computer.
good morning
also i want free data recovery for kvag virus please tell me all data lost what can i do.
My laptop is in under .kvag virus problem can you please help me?
I cannot solve my computer problem effected by Kvag virus all my file are extended. So i need help.