LAB BOT
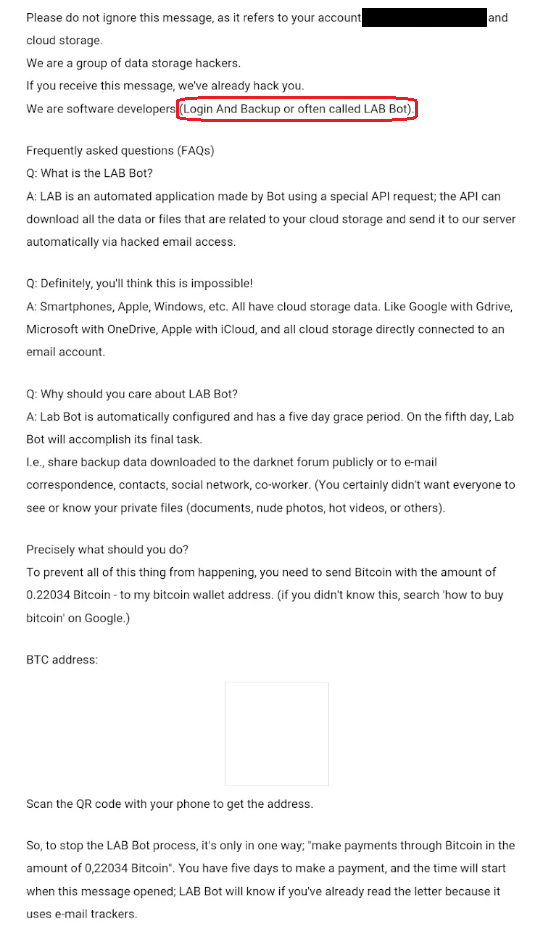
LAB BOT is a bitcoin scam received by email. This is also known as a sextortion email scam – the goal of an email like this is to scare the user into thinking he has been hacked. In most cases this is not true but just a hoax.
The LAB BOT Virus is a scam distributed by email.
Trojans such as LAB BOT get created for a variety of criminal purposes. After they infiltrate a computer, these threats can secretly launch a lot of criminal activities. Here, we will mention some of the most popular potential actions that an infection like LAB BOT may perform, but we will also provide you with a guide that can help you remove the Trojan from your system. That’s why, in case you need assistance in deleting the infection, we suggest you bookmark this page and carefully follow the instructions below.
The LAB BOT Scam
LAB BOT is a scam attempt via email. The email distributed by LAB BOT will contain a hacking threat towards the user and will demand payment in cryptocurrency, however this is usually just a trick.
Listing all the possible harm that a Trojan horse such as LAB BOT would require a separate article. This is because the Trojans are very versatile pieces of malware that can be programmed to perform almost anything malicious you could think of. There are no limitations to the criminal deeds a threat like LAB BOT can be used for and what the virus would do in your specific case depends on the hackers who control it. If the crooks decide that they need some information from your computer, they can program the Trojan to steal that information without your knowledge. They may also set their malicious creation to keep track of your activities, copy your login credentials, bank account details, or passwords and use them to access your online profiles or drain your bank accounts.
If you have a webcam or a mic on your computer or laptop, the Trojan can hack into them and allow the hackers to see you and hear your conversations. It can also allow them to record embarrassing videos and audios of you which can later be used to blackmail you or harass you in a number of ways.
The worst aspect about Trojans like LAB BOT is that they could deliver other viruses such as Ransomware and Spyware inside the compromised computer without the user having any idea about it. They even have the ability to turn your machine into a “bot” – a computer secretly controlled by remote attackers and used to send spam, distribute malware, or perform targeted attacks on other machines.
How can a Trojan be removed?
The Trojan horses are extremely harmful computer threats that can hide well in any computer system. They can mimic regular system processes and camouflage as legitimate-looking programs. Therefore, detecting and removing them can be quite a time-consuming task if it has to be done manually. A good antivirus program, however, can easily locate such malware and deal with it in a fast and reliable manner. That’s why the first thing you should do to guarantee your system’s safety is to invest in a good anti-malware program. If updated on a regular basis, such a program will be responsible for the overall computer security and will be able to stop not only Trojans but also ransomware, worms, spyware, and other harmful software.
SUMMARY:
| Name | LAB BOT |
| Type | Trojan |
| Detection Tool |
LAB BOT Email Scam Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment