*Ldhy is a variant of Stop/DJVU. Source of claim SH can remove it.
Ldhy File
If you’re having trouble opening important files on your computer, like family videos or important work documents, and you see them labeled as Ldhy files, it might mean that you’ve been targeted by the Ldhy ransomware. Even though these files look fine, they’ve actually been transformed into a kind of secret code that your computer can’t understand anymore, making them impossible to use. The ransomware has turned them into locked files, keeping you from getting to them. The only way to get these Ldhy files back to how they were before is to pay a ransom to the operators of the malware for a special key called a decryption key, which is supposed to undo the secret code and make your files usable again.
How to decrypt Ldhy ransomware files?
Decrypting Ldhy ransomware files is a challenging process that often requires specialized decryption tools or the unique decryption key held by the attackers. While some security researchers may develop decryption solutions for specific ransomware variants, including Ldhy, there is no guaranteed method to decrypt the files without paying the ransom. It’s important to avoid paying, as it supports cybercriminal activities. If you’ve been affected, disconnect the infected device from the network, keep a backup of the encrypted files, and consider seeking assistance from cybersecurity professionals to explore potential recovery options.
How to remove Ldhy ransomware virus and restore the files?
Ldhy Virus
The Ldhy virus is like a sneaky new member of the Ransomware family, which is a type of harmful software that’s been spreading a lot lately. This ransomware quietly infects computers using different tricks like spam emails and malicious links. If your computer gets infected with the Ldhy virus, your antivirus might not even notice because the malware won’t destroy your files or delete anything. But here’s the tricky part: the ransomware uses encryption to lock up your files and ask for money to unlock them. It’s like putting a secret code on your data and only giving you the access if you pay up. The worst part? You will realize your computer has this virus only after it displays a scary ransom-demanding note on your screen.
Ldhy
Unlike other types of malware that can damage your computer and make it totally unusable, Ldhy doesn’t destroy your system totally. Here’s what typically happens when you get infected. First, the ransomware looks for certain types of files on your computer, like documents, pictures, and more. Then, it makes encrypted copies of these files and then, a message pops up on your screen telling you to pay money if you want your files back. It’s like a digital hostage situation! Lately, lots of people have been asking for help to get rid of Ldhy, Cdxx or Cdcc from their computers. If you’re one of them, scroll down to the guide section where you will find instructions on how to remove it.
.Ldhy
The .Ldhy ransomware encryption is a special code that transforms your files into an unreadable format using complex cryptographic algorithms. This unique encryption makes your files inaccessible without the corresponding decryption key held by the attackers. Decrypting the .Ldhy ransomware encryption can be extremely challenging and often requires advanced knowledge of cryptography, which is beyond the reach of most individuals. Cybersecurity experts and law enforcement agencies occasionally develop decryption tools for certain ransomware variants, but the success of decryption largely depends on the specific ransomware strain and the strength of its encryption. In many cases, decryption without the proper key is practically impossible, emphasizing the importance of prevention and data backup to mitigate the devastating effects of a ransomware attack.
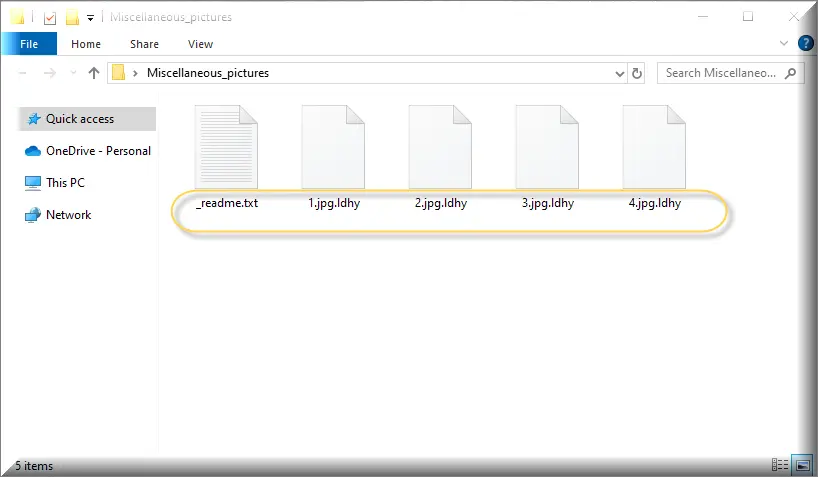
Ldhy Extension
If you see the Ldhy extension, it’s a sign that you should seek help immediately. If your computer is targeted by this harmful software, you might be thinking about paying the ransom. But remember, paying doesn’t guarantee you’ll get your files back, and it might encourage the cybercriminals to ask for more or continue their actions. Even if you receive a decryption code, it might not work. Instead of giving in to their demands, it’s better to focus on getting rid of the infection and exploring other solutions to recover your Ldhy extension files. This way, you won’t support the illegal money-extortion practice and can potentially find safer ways to retrieve your data.
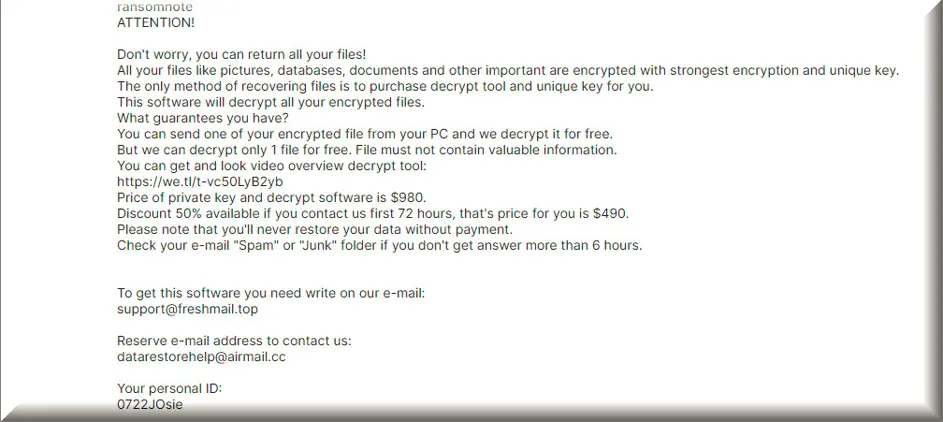
Ldhy Ransomware
When you’re hit by the Ldhy ransomware, a scary ransom demanding note appears on your computer screen. It tells you that your important files are locked up and you have to pay money to get them back. The note usually gives instructions on how to pay the ransom, often in a cryptocurrency like Bitcoin, and threatens to delete your files if you don’t pay within a certain time. If you ever see such a note, it’s important to stay calm and not pay the ransom. Paying doesn’t guarantee you’ll get your files back, and it only encourages the cybercriminals to keep doing this. Instead, focus on removing the Ldhy ransomware from your computer and look for ways to recover your files without giving in to their demands.
What is Ldhy File?
Simply put, an Ldhy file is a regular file like documents, images, or videos that has been locked by the Ldhy ransomware, making it impossible to open without a special key. You can recognize an Ldhy file by its different file extension or changed name. Decrypting this file, however, isn’t easy – it’s a tricky process that can lead to losing important data and causing problems for you, whether you’re an individual or a business. Sometimes experts or law enforcement can help recover files without paying the ransom, but it’s better to prevent this situation by having strong online security measures in the first place.
SUMMARY:
| Name | Ldhy |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
*Ldhy is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Ldhy Ransomware

Rebooting the compromised system in Safe Mode is described in the first step of this guide. The elimination of the malware from your computer will be much easier if you do this, that’s why we recommend you start with clicking on the Safe Mode link and completing the instructions listed there.
Before you reboot your computer in Safe Mode, though, make sure that this page is saved in your browser’s bookmarks, so you will not have to search for the Ldhy removal instructions again after the system boots up.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ldhy is a variant of Stop/DJVU. Source of claim SH can remove it.
Due to its secrecy, Ldhy is a variant of ransomware that is difficult to detect. A threat like this might cause substantial damage to the system, since it may go unnoticed for long periods of time.
So, if this ransomware infects your computer, one of the most difficult challenges you’ll have to deal with is finding and stopping its harmful processes from operating.
In order to ensure the safety of your computer, we suggest that you carefully follow the instructions outlined below.
Press CTRL+SHIFT+ESC at the same time on your computer’s keypad. Navigate to the Processes tab in Windows Task Manager.
Right-clicking the process and selecting “Open File Location” from the fast menu should be used to inspect any process that uses excessive CPU and memory, has a strange name, or otherwise seems suspicious.

You may use the free online scanning tool below to verify the files associated with the process to ensure that they are clean of any potentially dangerous code.

If the scanner identifies a hazard in some of the scanned files, you can use the right-click menu to first end the related process. After that, return to the dangerous files and delete them from their original locations.

Next, we’ll explain to you how to disable any startup items that may have been installed by the malware on your PC.
Select System Configuration from the search results by typing msconfig in the Windows search field. After that, open the Startup tab to see if there are any new entries:

Unchecking any startup items that appear to be associated with the ransomware is what you should be aiming at here. Pay attention to any extra startup components that may be running on your computer, but aren’t related with any of the programs that typically start when the system boots up. Uncheck their checkmarks if you find enough information to show that they should be deactivated, and make sure you make no modifications to software that is part of the operating system or is trustworthy.

*Ldhy is a variant of Stop/DJVU. Source of claim SH can remove it.
In order to remove the ransomware and prevent it from reappearing or leaving malicious components behind, you must delete any dangerous registry entries you discover in your registry editor.
To open the Registry Editor, type regedit in the Windows search field and hit Enter. To find ransomware-related files in the Registry Editor, use the CTRL and F keyboard keys combination and type the name of the danger in the Find box, then click Find Next. You can delete dangerous entries by right-clicking on them.
Attention! Only the ransomware-related registry entries should be removed. If you continue to make changes to the registry, you risk damaging your system and the installed applications. Ldhy and other viruses may be eliminated from your computer’s registry by using a professional malware cleaner like the one linked to on this page.
When you’re finished, close the Registry Editor and check the places indicated below for any additional hazardous files and sub-folders. To access each one, type it into the Windows search field and press Enter.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Carefully search for any harmful-looking files or subfolders that have been added recently to each of the locations. The content of the Temp folder should be deleted to remove any potentially hazardous temporary files from your system.
The next step is to check your system’s Hosts file for any changes that might be malicious. To do that, you need to first open a Run box on the screen. The Run dialog box may be opened by pressing the Windows and R keys together. Using the Run box, enter the following command and click OK:
notepad %windir%/system32/Drivers/etc/hosts
Please let us know if the Hosts file contains a number of dubious IP addresses under “Localhost”, as seen in the sample image below. Any other modifications you detect in your Hosts file should also be reported, so please let us know about them in the comments section below if you see anything strange. If you have any questions or concerns, please don’t hesitate to contact us.


How to Decrypt Ldhy files
Various approaches of decrypting encoded files may be used when it comes to recovering from the consequences of a ransomware attack. These approaches and the available alternative file-restoration methods depend on the variant of ransomware that has infected the system. To identify the type of Ransomware you’re dealing with, look at the file extensions that have been added to the end of the encrypted files.
New Djvu Ransomware
STOP Djvu is one of the most recent Djvu Ransomware versions. If the extensions of your encrypted files end in .Ldhy, you may be infected with this Djvu ransomware variant.
There may be hope for those who have had their data encrypted by this ransomware if the encryption that has been applied has been based on an offline key. The URL below provides access to a decryption tool that may be of help.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Decryption
Simply click “Run as Administrator” on the downloaded file and then “Yes” to proceed with the decryption process. Be sure to read the short instructions and license agreement displayed on your screen before continuing. To begin the decryption procedure, click the Decrypt button.
Keep in mind that this tool may be unable to decode data encrypted using unknown offline keys or online encryption. If you have any questions or you come across issues, please let us know in the comments section below.
Important! Make sure your computer has been inspected for ransomware-related files and potentially hazardous registry entries before attempting to decode the encrypted data. In order to eliminate the dangerous files related to Ldhy, please use the online virus scanner and the anti-virus software recommended on this page.

Leave a Comment