.Leto Virus
.Leto Virus is a dangerous computer threat labeled as a Ransomware cryptovirus. .Leto Virus can encrypt your files and demand a ransom for their decryption.
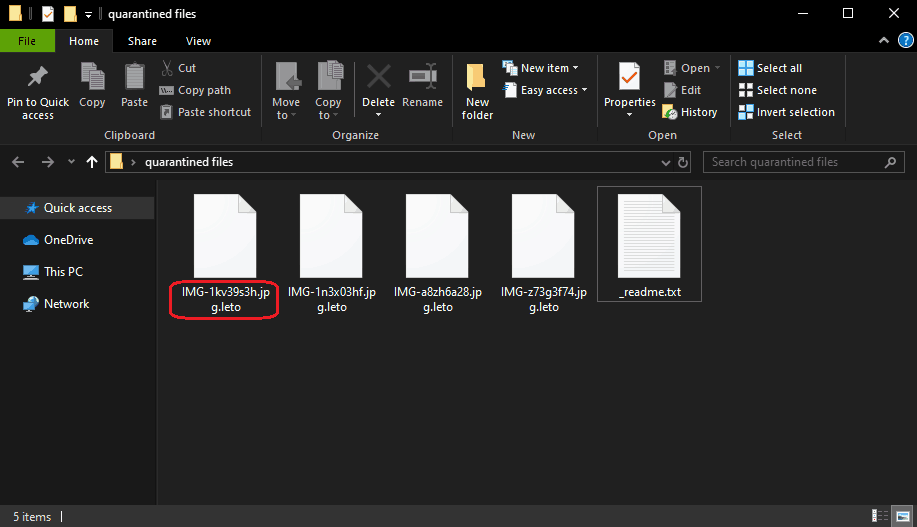
When the .Leto Virus is finished encrypting your files they will look like this.
This is both an act of invasion of privacy, and a criminal act. Because of viruses like this one, users can lose some of their most valuable files without ever being able to retrieve them. And losing digital information can sometimes be fatal for companies or people who own businesses.
However, we will try to help you deal with the ransomware that has compromised you as much as we can. For that, we have published a removal guide below this post with the needed steps to remove the .Leto Virus. The guide will also provide you with some alternative ways to restore the encrypted files. While we can’t promise the latter is going to work perfectly, it won’t cost you a thing to try it out.
The .Leto Virus
The .Leto Virus is a malicious program designed to encrypt your data. The .Leto Virus does that in order to later blackmail you for your data’s release.
The main agenda of the threat is to extort money from the owner of the infected computer, who obviously needs to access their files. This is a dirty tactic, and a highly illegal one, but, sadly, the new ransomware versions are some of the most difficult types of malware to deal with. The growing popularity of threats like .Leto Virus, .Bora and .Reco is due to the fact that they are notoriously difficult to detect.
The .Leto Virus file encryption
The .Leto Virus file encryption process is nearly undetectable while underway. Once the .Leto Virus file encryption is complete, only a unique decryption key can unlock it.
Once all the targeted files are locked, the hackers require a ransom in Bitcoins, which is the most popular of all cryptocurrencies to date, and is also almost impossible to trace. Just because in the virtual world there’s a lot of criminal activity going on, however, it doesn’t necessarily mean you should be left at the mercy of every threat. Ransomware is a pressing issue, but leading cyber-security experts are actively researching and working on new solutions. As per the information available, malvertisements are the most effective method to distribute cryptoviruses like .Leto Virus. The malvertisements are fake online adverts (usually in the form of banners, and pop-ups) that download the virus to your device automatically when you click on them. With this in mind, it would be wise to avoid interacting with any questionable online advertising materials, because you really can never know what might be hiding behind them.
Spam emails are the second most likely source of ransomware infections. Normally the infected email would hold an attached file, like a Word or a PDF report, and that file would have a Trojan Horse virus hidden inside. Once the file is opened, the Trojan activates in the system, and then it automatically downloads the Ransomware cryptovirus.
Detecting the infection at the time of contamination may not be possible, but having it removed is of great importance if you want to continue to use your machine. As far as the encrypted files are concerned, we encourage our readers to use personal backups or give a try to alternative file-recovery methods such as those in the removal guide below before considering the ransom payment.
SUMMARY:
| Name | .Leto Virus |
| Type | Ransomware |
| Detection Tool |
Remove .Leto Virus Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

my all file extension are showing .leto all important documents please help me to recover my files…..
dide you find a solution bro I have the saim problrm
PLEAS HELP ME i CANT DYCREPT MY FILE PLEAS HAW I CAN DYCREPT MY FILE