*Lkfr is a variant of Stop/DJVU. Source of claim SH can remove it.
Lkfr File
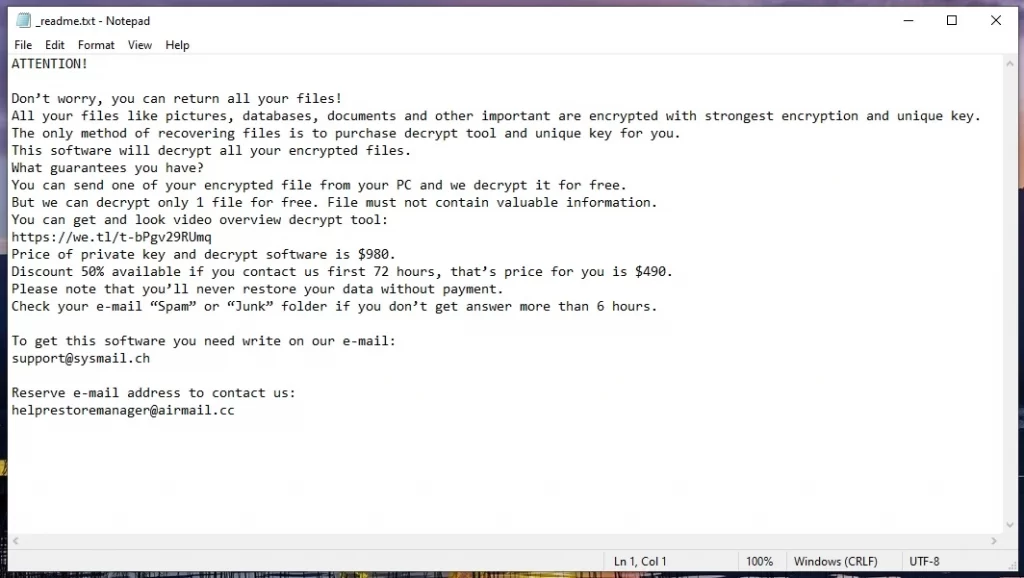
If you’ve stumbled upon this article because you have been faced with Lkfr file encryption, it’s important to carefully read the information that follows. Unfortunately, you’ve been ensnared by the clutches of a ransomware cryptovirus, a malicious digital exploit orchestrated by cyber criminals. The visible hallmark of this intrusion, the Lkfr file encryption, serves as a formidable tool used by the ransomware to selectively restrict access to important data stored within your systems. This encryption changes your files into an unusable bunch of digital data through a complex cryptographic code. The attackers promise to reverse the encryption and restore your files to their original state if you pay them a hefty amount of money as a ransom.
How to decrypt Lkfr ransomware files?
Decrypting the Lkfr ransomware files is a long process that requires disconnecting your infected computer from the Internet and detecting the specific ransomware variant that has encrypted your data; this paves the way for potential solutions, which include searching for online cybersecurity resources that could guide you through the intricate process of data retrieval. Once you’ve stumbled upon a fitting recovery method tailored to your ransomware variant, stick to the instructions or use the assistance of a powerful software or security professional.
How to remove Lkfr ransomware virus and restore the files?
To remove the Lkfr ransomware virus and restore the files, you need to be armed with powerful antivirus software. Use it to run a thorough system scan to detect and eliminate invasive malware. Once your system is ransomware-free, you can use backup files to restore your data with ease. Those without backups can contact seasoned data recovery specialists or turn to reputable recovery software.
Lkfr Virus
Within the category of ransomware, the Lkfr virus (similar to infections like Lkhy and Ldhy) emerges as a formidable threat, notorious for encrypting digital files and restricting access to them until a ransom is paid. This insidious malware infiltrates computers through various channels – seemingly harmless spam emails, enticing advertisements, and even concealed backdoor viruses. Confronting the Lkfr virus proves to be a serious challenge because it uses cutting-edge file encryption techniques and operates in stealth until it completes its malicious agenda. The aftermath of its attack often leaves victims grappling with permanent file unreadability, all while the criminals ask for a ransom payment in exchange for an elusive decryption key.
Lkfr
As the online landscape evolves, so do the ransomware threats. Presenting itself as a digital nightmare, Lkfr can be described as the latest online danger, causing a lot of trouble to those unfortunate enough to encounter it. This malicious software can lay siege to your personal files and documents. This includes a range of data such as family photos, videos, personal correspondence, and important documents. The intent behind targeting personal files is to exploit the emotional attachment and critical value individuals place upon them, leveraging this sentiment to amplify the pressure for a ransom payment. The corporate landscape doesn’t remain unscathed either, as Lkfr sets its sights on business-critical data that can disrupt business operations and coerce organizations into paying ransoms to resume their work.
.Lkfr
While the path to .Lkfr decryption may initially appear shrouded, there are some methods for data recovery that may be worth checking. Although the hackers possess the elusive decryption key, and promise to send it to the victims as soon as they pay, we strongly advise against sending money to anonymous cybercrooks. The reason is, not only there’s no guarantee that doing so will result in the safe return of your .Lkfr data, as attackers may not provide a functional decryption key, but also, paying only encourages future attacks, and may even have legal and ethical implications.
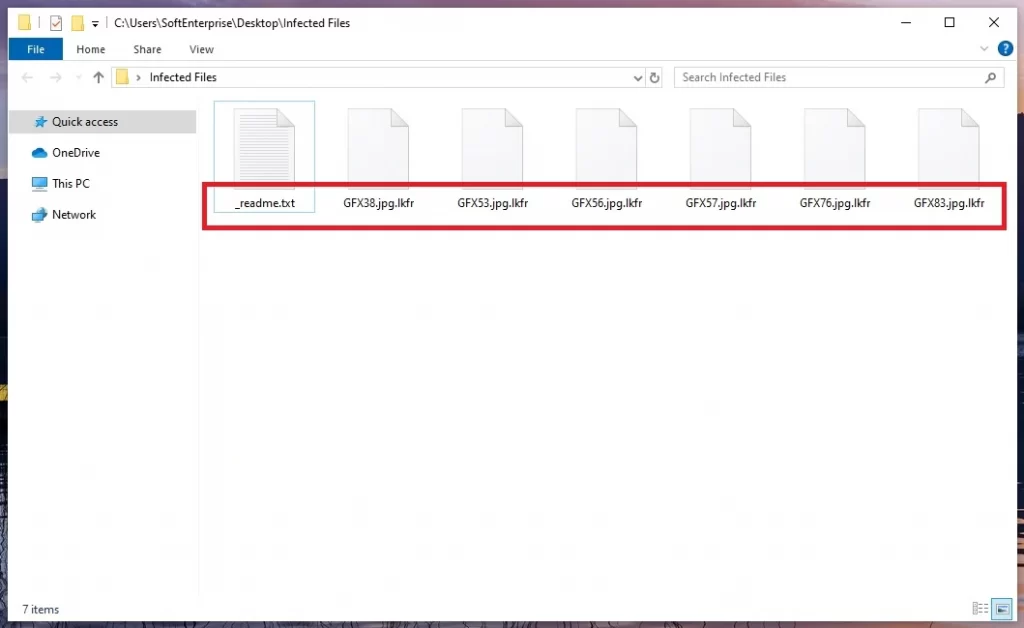
Lkfr Extension
The Lkfr extension is a special file extension that is added to encrypted files as a way for attackers to distinguish between locked and unlocked data. While the presence of the Lkfr extension can indicate an attack, it’s important to note that the absence of such doesn’t necessarily mean your files are safe. Cybercriminals often use unique file extensions for different ransomware variants, making each attack distinct. Some ransomware families append random characters to file names or use well-known extensions to deceive victims. Therefore, understanding the specific ransomware variant and its associated extension is crucial for recovery efforts. This information can guide your response, such as searching for decryption tools or seeking professional assistance.
Lkfr Ransomware
The Internet space knows no bounds, sparing no one from the grasp of the Lkfr ransomware. Whether you’re an everyday user or a multinational corporation, the threat looms large. The grim statistics unravel the myth that only high-profile entities are targeted – the average online user is equally susceptible to the attacks of cybercriminals. As the reach of these attacks grows, you face a tough choice: pay the hackers to get your data back or try other ways to recover your files. Don’t worry, though – before you get overwhelmed, our detailed guide on removing Lkfr ransomware can help you start fixing the problem.
What is Lkfr File?
The Lkfr file is like any other regular file on your computer, but it has gone through a special kind of transformation called encryption. This encryption process turns the file’s contents into a secret code that can’t be understood without a special key. As a result, the file becomes unreadable and unusable until it’s decrypted back to its original form. The Lkfr file is not dangerous and will not cause harm by staying on your computer, but will simply take up digital space. Cleaning your computer is important to get it back to normal. You can try using backups, copies from external disks, or even check our list of free decryption tools on our website. It’s linked in the guide below to help you out.
SUMMARY:
| Name | Lkfr |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Recovery Tool | Not Available |
| Detection Tool |
*Lkfr is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Lkfr Ransomware

Just as with most other ransomware variants, removing Lkfr requires complete focus and attention to detail. To avoid searching for this guide multiple times during the ransomware removal process, mark this page as a favorite in your browser and save the instructions for later use. Restarting in Safe Mode, which disables all but the most essential programs and services, makes it easier to identify and remove malware, thus we recommend you do that before you move to the instructions in the second step of this guide.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Lkfr is a variant of Stop/DJVU. Source of claim SH can remove it.
Open the Task Manager by pressing CTRL+SHIFT+ESC on your keyboard and look through the Processes tab for any suspicious processes. An emphasis should be placed on CPU and memory-intensive processes that look odd and cannot be linked to any of the programs that you normally run on the computer. If you detect a specific process that looks suspicious, right-click on it and select Open File Location.

The powerful free online virus scanner below can be used to scan the files of the suspicious-looking process for malicious code. You can do that by dragging and dropping the files found in the File Location folder of a process that you suspect is harmful in the scanner and starting a file check.

If danger is found in the files, those files need to be deleted. First, however, you need to go back to the suspicious process and stop it by right-clicking on it and selecting End Process. After you do that, go back to the files and delete them from the system. If you do the other way round, some of the files may not want to be deleted while the process is still running.

Ransomware may make some changes in the System Configuration settings, particularly the Startup tab, therefore, the next step is to go there and search for unwanted alternations and potentially unwanted startup items. You can easily open System Configuration check what is listed in the Startup tab by typing msconfig in the Windows search bar, hitting Enter, and clicking on the result:

You should uncheck any startup item that has an unfamiliar name or a manufacturer that you don’t trust. If you make any changes, save them and only leave the checkboxes next to legitimate startup items checked.
Malware frequently targets the Hosts file on a computer. Therefore, the Hosts file should be opened in order to search for any malicious IP addresses listed under “Localhost“. To do that, press Windows and R at the same time and hit the Enter key to open a Run window. Next, in it, copy/paste the following line and press Enter:
notepad %windir%/system32/Drivers/etc/hosts
Once you see the Hosts file on the screen, go to Localhost in the text. Any IP addresses that look like the ones in the image below should be sent to us so that we can check them out. They will be examined by a member of our team to see if they pose a threat.


*Lkfr is a variant of Stop/DJVU. Source of claim SH can remove it.
In order to remain on the system longer and be more difficult to remove by inexperienced users, more advanced malware frequently adds harmful registry entries. Therefore, if you’ve had your computer infected by Lkfr, the ransomware may have added harmful files to your system registry that you don’t know about. In order to determine whether or not the infection is still present, you must run a Registry Editor check. This can be done in a variety of ways. One of the easiest ways is to type Regedit in the Windows search bar, and then press Enter. The CTRL and F keys can be used to open a Find window. In the Find box, type the name of the ransomware and the Find Next button.
Delete any entries of the ransomware infection that are detected by the search. If needed, repeat the search again until no more entries are found. When deleting ransomware-related files, be aware that your operating system may be damaged if you happen to delete entries that are not related to the infection. On the other hand, Lkfr may reappear if you don’t remove all registry entries associated with the threat. For this reason, we recommend using anti-malware software to scan your computer for hidden malware files and clean your registry thoroughly.
Ransomware-related entries can also be found in the following five places, which should be checked by hand. By typing their names into the Windows search bar and then pressing Enter, you can open them one by one.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Carefully search for recently added files in each of these locations and delete any potentially harmful files you find there. To complete this step, open the Temp folder, select all files, and then press the Del key on your keyboard to delete all the temporary files.

How to Decrypt Lkfr files
If ransomware is removed successfully, the next most pressing issue for those infected is how to decrypt their encrypted files. This procedure must be done with extreme caution because each ransomware variant has a different method of file-recovery that can be used. The encrypted file extensions are a good indicator of the variant of ransomware that you are faced with.
Professionals recommend that you use a trusted anti-virus program (like the one available on this page) to get rid of malicious software before trying to recover your files. Once you are sure that Lkfr has been completely removed from your system, you can safely experiment with various file-recovery methods and even connect backup sources to the ransomware-free computer.
New Djvu Ransomware
STOP Djvu, a new Djvu ransomware variant, has been discovered recently by professionals in the cyber security field. What distinguishes this infection from others is that, in most cases, the files encrypted with this threat end with the Lkfr suffix. The good news is that the decryptor in the following link may help you decrypt the data if an offline key was used to encrypt it.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Once you click on the link above, click the blue Download button on the web page to start the STOPDjvu.exe download.
To run the program, select “Run as Administrator” and then press the Yes button. Decryption can begin after you have read the license agreement and the brief instructions and have clicked the Decrypt button on the application’s toolbar. Unknown offline or online keys cannot be decrypted using this tool.
Keep in mind that the anti-virus programs listed in this removal guide can help you quickly and easily remove the ransomware if you get into trouble. Alternatively, you can use a free online virus scanner to check suspicious files.

Leave a Comment