The Looy File
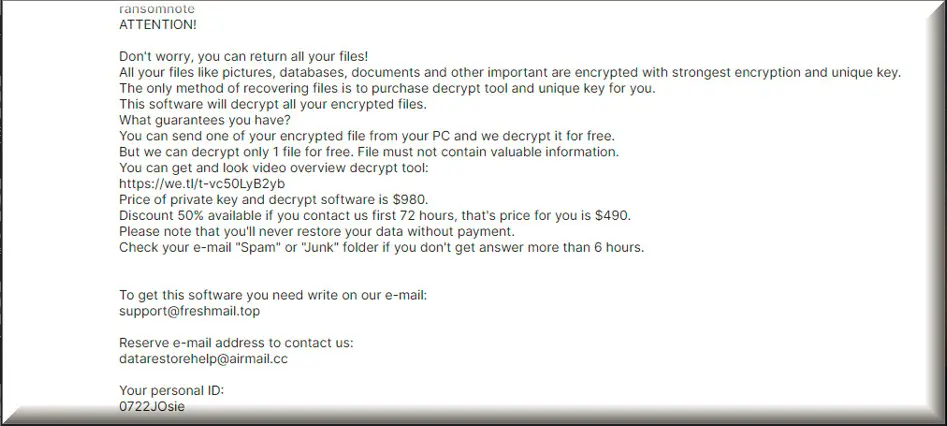
The Looy file encryption is a way to lock up your files and keep them hidden from everyone except those who have the special key to open them. But here’s the problem: the hackers who use the Looy file encryption have that key, and they want you to pay them money to get it. These types of ransomware, like Looy, can sneak onto your computer in different ways. They might come attached to emails you don’t want or show up in social media messages. Sometimes, you can even get them from online ads that lead to dangerous websites. So, you have to be really careful about what you click on and where you download things from to avoid getting your computer infected.
How to decrypt Looy ransomware files?
Decrypting Looy ransomware files is a complex and challenging process. It’s essential to identify the specific ransomware variant that has encrypted your files, as each one may require a unique decryption method. In some cases, cybersecurity experts and law enforcement agencies have released decryption tools for certain ransomware strains, so researching if such a tool is available is a good first step. However, if no decryption tool is available, you may have to rely on backups of your files if you have them. Paying the ransom is generally discouraged, as it does not guarantee the safe return of your files and encourages cybercriminals.
How to remove Looy ransomware virus and restore the files?
To remove a Looy ransomware virus and restore the files you need to consult cybersecurity experts or use reputable antivirus software. However, the removal process doesn’t decrypt your files. To restore them, you typically need a backup of your files that predates the ransomware infection. Once your computer is clean, you can safely transfer your backup files to your device. If you don’t have backups, check if a decryption tool exists for the specific ransomware variant you encountered. Some cybersecurity organizations provide these tools for free. However, paying the ransom is strongly discouraged, as it doesn’t guarantee file recovery and supports criminal activities.
The Looy virus
The Looy virus employs a multifaceted entry strategy in order to get inside as many computers as possible. From deceptive emails to tainted downloads, phishing schemes, rogue online ads, and exploiting instant messaging platforms — it leaves no stone unturned. As the ransomware unfurls its encryption net, files across the system find themselves ensnared. The problem doesn’t end with the removal of the Looy virus; accessing the encrypted data remains a formidable challenge. This highlights the urgency of consistent backups — either on physical external drives or secure cloud storage. It’s not just about data recovery; it’s a safeguard against the unpredictable nature of ransomware.
Looy
Looy is a type of computer virus that wants your money. It does this by locking up your files and making you pay a fee to get them back. It spreads through sneaky methods like backdoor viruses, spam emails, and downloading illegal software from the internet. Ransomware like Looy is especially troublesome because it can completely block you from using your files or even your whole computer until you pay the hackers. If you don’t agree to pay the ransom, you might lose access to all your locked data. So, it’s important to be careful and learn more about how to protect yourself from these types of viruses.
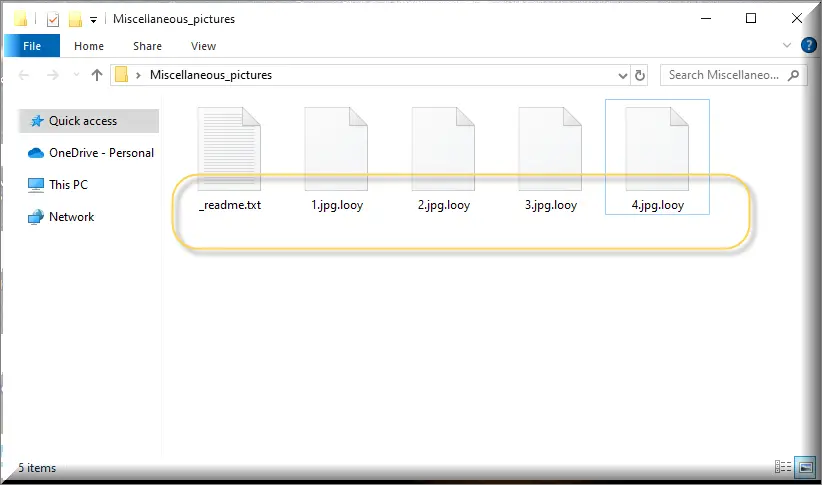
.Looy
The .Looy suffix is like a digital tag cybercriminals attach to your files when they want to lock them up. This tag helps the ransomware remember which files it has encrypted and which ones it hasn’t. The .Looy suffix is specific to the particular kind of ransomware that has infected your computer, and it can look like a mix of letters and numbers tacked onto the end of your file names. For instance, if you had a file called “photo.jpg,” after the ransomware encrypts it, it might turn into something like “photo.jpg.Looy”. This suffix basically says that your files are off-limits until you pay the hackers for the special key to unlock them.
Looy Extension
Removing a Looy extension can be challenging primarily because ransomware is designed to be persistent and resistant to removal. Additionally, this malware often employs sophisticated encryption techniques that require a unique decryption key to unlock the files, and hackers hold this key hostage until a ransom is paid. Removing the ransomware itself can be complex because it may have established deep-rooted system-level access or hidden itself in obscure locations within the computer. To effectively deal with the Looy extension it, specialized knowledge and tools are often required, and even then, the process can be time-consuming and not always successful in recovering the encrypted files, which is why prevention through regular data backups and strong security measures is crucial.
Looy Ransomware
The Looy Ransomware is a sophisticated malware threat that uses a method called file-encryption to lock users’ data. During the last two decades of the 20th century, programs under the name of Ransomware first appeared in Russia. At first, there were only two versions of Ransomware-like viruses – file-encrypting ransomware, like Looy Ransomware, that locks up your files by encrypting them, and then asks for a ransom to unlock them and sends you a message with details on how to pay and screen-lockers, that don’t encrypt your files but instead blocks your computer screen with a big message asking for money to unlock it. However, now there are even ransomware versions that can infect phones and tablets, doing similar things as the ones mentioned before. So, it’s important to be cautious and protect your devices from these tricky viruses.
What is Looy File?
A Looy, Nood, Kool or Wisz file is any file on your computer that has been locked with ransomware encryption. It’s crucial to understand that there’s no surefire way to guarantee that you’ll get your encrypted Looy file back, even if you remove the ransomware. Paying the ransom isn’t a guaranteed solution either, as hackers might take your money and run. Therefore, instead of paying the ransom, it’s better to explore alternative options, such as seeking help from experts experienced in dealing with such viruses or following a reliable removal guide. Prevention is your best defense against these types of threats. Regularly back up your data to avoid falling victim to file encryption, ensuring that no one can blackmail you for access to your files.
SUMMARY:
| Name | Looy |
| Type | Ransomware |
| Detection Tool |
Looy Ransomware Removal

If you’ve decided to follow the instructions on this guide, you’ll need to restart your computer during some of the steps below. Therefore, it’s a good idea that you bookmark this page in the beginning, so you can get back to it and swiftly finish removing Looy.
Once you’ve bookmarked the removal guide, we recommend you reboot your computer in Safe Mode by following this link’s instructions.Then, with the computer successfully booted in Safe Mode, please follow the steps below.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
In this step, what you need to do is check the compromised system for processes that are related to the ransomware and are running in the background. The best way to do that is to go to the Start menu and open the Task Manager.
Launching the Start menu is as simple as clicking on the Start button in the bottom left corner of your screen. When you do that, the Windows search box will appear. Type “Task Manager” into it, then hit Enter on your keyboard.
When you get there, look for any processes on the Processes tab with the Looy name or any other suspicious processes that consume a lot of system resources.
Select each suspicious-looking process, right-click on it, and then choose Open File Location to see the files of the dubious-looking process and check if they are legitimate.

The File Location folder will contain files related to the selected process. Use the virus scanner provided below or another reliable scanning program to ensure that these files are free of harmful code.

If the scan results detect a danger in any of the scanned files, it’s important that you immediately stop the running process related to these files and delete any malware-infected data from your computer.
Note that you may check as many processes as you like using the scanner above to ensure that the system is free or ransomware-related processes running in the background.

Your infected computer may already have some ransomware-related processes that are set to start when you turn it on. For this reason, as soon as you complete the instructions in step two and stop all malicious processes from running in the background, in the third step, you should check the Startup Tab in System Configuration and see what startup items have been configured to start when your computer boots up.
For that, enter msconfig into the Start menu search bar and press Enter to launch System Configuration. Click the “Startup” tab at the top of the new window to view the startup process.

There, you’ll see a list of startup entries associated with the programs you’ve installed. Remove the checkmarks from anything with an unknown manufacturer or a strange-looking name after carefully researching it. Click the OK button to save your changes.
Please bear in mind that ransomware often disguises itself as another application in order to avoid detection. As a result, you must carefully research the list of startup items that are checked online before attempting to deactivate any of them.

The persistence of ransomware threats like Looy is commonly attributed to the addition of damaging registry entries inside the system’s registry, which is a popular target for threats of this kind.
This is why you should launch the Registry Editor (type “regedit” in the windows search bar and hit Enter), search it for any Looy-related entries and remove everything that you think is dangerous to make sure the threat doesn’t reinstall itself when you reset your computer.
After entering the Registry Editor, use CTRL+F to open a new Find window. Type the name of the ransomware in it and run a registry scan using the Find Next button to see whether there are any ransomware-related entries, and then delete the files that you discover.
Attention! Remove registry entries with caution to prevent causing damage to your system. Use a professional registry cleaning tool like the one we recommend here if you aren’t sure what needs to be deleted. Such software will save you time and will ensure that your computer’s records are free of any harmful software.
Once you’ve completed wiping the registry clean, use the Start menu search bar to type the locations listed below and open each one of them by pressing Enter.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
If you find any new files or folders with suspicious-sounding names or files that seem to be part of the Looy malware, be sure to delete them immediately.
Open Temp, then select and delete all the files in there, including those that were generated by the ransomware itself.

If, aside from being infected with Looy, you have a doubt that your PC has been compromised by another threat or has been hacked, we recommend you to check what is going on in your Hosts file.
For that, open the Start menu and type the following into the search box:
notepad %windir%/system32/Drivers/etc/hosts
See whether there are any suspicious-looking IP addresses under Localhost in the file’s text, as those in the example below:

If you see anything strange in your Hosts file that concerns you, please let us know in the comments section below and a member of our team will do their best to assist you.
How to Decrypt Looy files
Upon facing a ransomware attack, several avenues can be ventured into for accessing the encrypted content. Yet, the chances of these strategies working rest on the ransomware variant that is meddling with your files. The initial step is discerning the ransomware type, which is achievable by inspecting the file suffix of encrypted content.
Spotlight on Djvu Ransomware
A recent addition in the Djvu ransomware series is the STOP Djvu edition, evident by the .Looy suffix on compromised files. If offline keys are the used for the encryption, data recovery can be possible. A decryption solution for this variant can be accessed using the link below.
Decryption
Kickstart by downloading the decryption application and activating it as a system administrator. Prior to diving in, glance through the displayed license agreement. Clicking the “Decrypt” option starts the decyrption process.
Please understand that the tool might not work well against new offline keys or online encryption. If you have any questions, please leave them in the comments below.
Alert! It’s important to examine your system for dangerous components linked to ransomware and questionable registry logs before starting your decryption attempts. To eradicate any malicious files, consider the virus removal tool and the online virus scanner on this page.

Leave a Comment