This page aims to help you remove .Lotep Virus Ransomware for free. Our instructions also cover how any .lotep file can be recovered.
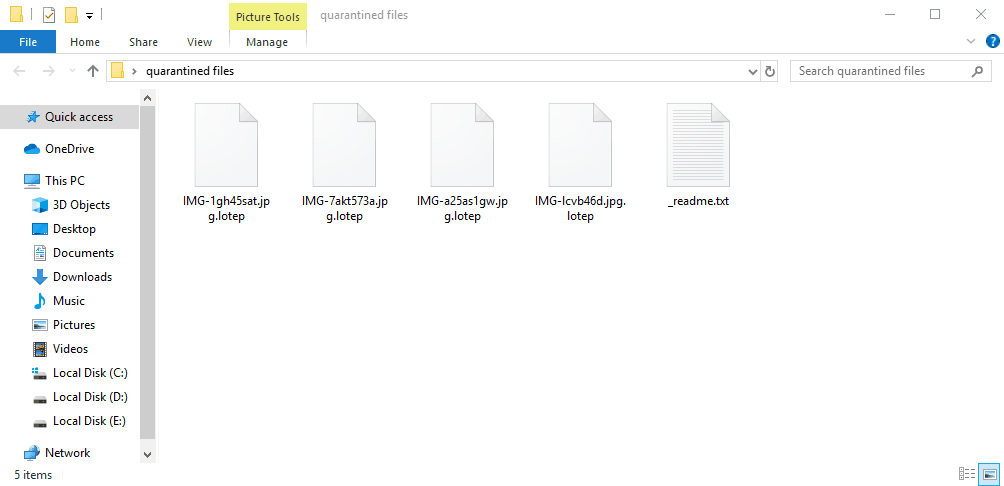
When the encryptng is finished .Lotep Ransomware will leave a _readme.txt file which will hold instructions for you to follow
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
*Redacted for security reasons*
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
The Internet can be very helpful and entertaining but, at the same time, if the web users are not cautious enough, it can also expose them to nasty system infections and all sorts of harmful computer viruses. Nonetheless, not many of those threats are as noxious and as challenging to deal with as the notorious Ransomware kind of computer viruses such as .Truke or .Dalle. One thing that makes Ransomware one of the main threats of the Web is related to the way these infections operate and, in the next paragraphs, we’re going to tell you what we mean. The main focus of the current post is a newly developed Ransomware piece called .Lotep which falls under the subcategory ofj cryptoviruses. This malware is famous for utilizing a really sophisticated data encryption method through which it could restrict the access to your most valuable computer files. Later on, the attack of .Lotep Virus would go to its next stage where it will demand a ransom from the victim in exchange for a special file-decrypting code. Details on the way to carry out the ransom payment would normally be given in a notification, which typically gets displayed immediately after the file encryption process is over. In this article, we’ve made our best to provide you with a guide that may help you and all our readers, who have been attacked by .Lotep Ransomware to take care of this nasty infections.
The typical way Ransomware operates
There are a couple of extremely important things which a user needs to take into account when faced with a Ransomware such as .Lotep Virus. The first aspect which makes those threats such a danger is their ability to remain unnoticed in the system until they have already accomplished their goal and the data has been sealed by their encryption. This is exactly why a lot of users never have the chance to realize what is happening with their data till it is far too late.
To top it all, these Ransomware-based viruses are typically created with great attention and complexity in the code they are using. Because of this, in some cases, the encoding simply can’t be breached and the encoded files are lost forever. Their capability of staying unnoticed by the majority of the anti-virus tools doesn’t really help either. Though Ransomware versions such as .Lotep seem to be very unpleasant, they do not harm the PC or its system directly. Unlike other viruses and security threats, those pieces of malware are not designed to gain access to information, to format hard drives or to harm system files – all they do is they simply make encrypted illegal copies of the files on your computer and delete the originals so that you cannot access your files before carrying out the ransom payment. And since the file-encryption is not considered as an actual damage, this is exactly why an antivirus piece of software could, more often than not, dismiss such a virus. In fact, it is worth to mention that file encryption is usually used as a sort of advanced data protection technique which is just one more reason why the majority of the cyber safety applications can’t identify it as a possible risk. Paying the money to the hackers behind .Lotep Ransomware, however, is not advisable and security experts, including our team, suggest using alternative methods which focus on removing the infection and recovering files through backups.
SUMMARY:
Remove .Lotep Virus Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Reply