The Luckyguys.top Malware
Luckyguys.top is categorized as a browser hijacker by security experts. Luckyguys.top is known to cause browser redirects and different pop-up advertisements in addition to security vulnerabilities.
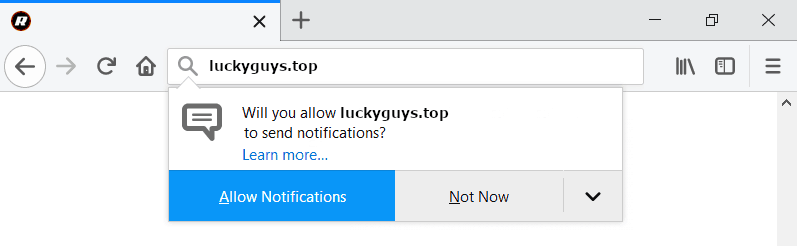
The Luckyguys.top Pop up Malware will display pop up ads and messages
A browser hijacker is a type of software program/application that operates through the user’s browser after having become part of it. Most such apps can get added (or rather add themselves) to the majority of browsing programs out there – any browser from Chrome and Firefox to Edge and Opera can have a hijacker app operate from it. Initially, it might seem that hijacker apps are like regular extensions for browser programs. However, in reality, most such software elements are rather annoying and sometimes might even expose the computer they’ve been installed on to different forms of online hazards such as virus attacks from nasty threats the likes of Ransomware, Trojans, Spyware, etc. The main symptoms that most users experience when they have a hijacker is random page redirects and ads generation as well as replacement of the browser’s default search engine, homepage and new tab page. Typically, the said browser modifications tend to make the browser less effective since the changed starting page/new-tab page and search engine oftentimes facilitate the advertising campaigns that hijacker apps typically conduct. This means that if a hijacker is on your browser, the new search engine or homepage/new-tab page that it might have added to your browser are likely to redirect you to web locations that you don’t really want to visit just so that those web locations could get more exposure to a greater number of users. Naturally, all of this could be highly frustrating to anyone who is forced to experience it on their PC. This is why apps belonging to the hijacker category are widely regarded as unwanted and why most users would rather have them uninstalled than put up with their presence.
A typical example of a potentially unwanted program is the Segurazo Antivirus.
Here, we will give you an example with one specific hijacker app. This is a software element named Luckyguys.top that seems to possess some of the main characteristics of a typical browser hijacker – the ability to spam the targeted browser with random irritating ads, banners, pop-up messages and blinking boxes, the ability to redirect the user’s searches to unrelated pages and sites and also the ability to alter some of the browser’s functions and settings (the homepage, the toolbar, the search engine, etc.). Due to all this, Luckyguys.top is regarded as an undesirable piece of software and many customers would like to have it removed from their machines. In case you are one of those people with Luckyguys.top on their computer who are seeking methods of getting rid of it, look no further. Below this write-up, you can find a set of detailed instructions alongside a tested removal tool both of which you can employ in the quick and effective removal of the pesky app. Just follow the steps from the guide or use the automatic removal program and you should be able to eliminate Luckyguys.top in just a couple of minutes.
The Luckyguys.top Malware on iPhone
In the start of this article we mentioned that aside from being highly irritating, hijackers might actually sometimes trigger certain security hazards. What we meant by that is the fact the banners, pop-ups, redirects and all the other advertising materials generated by a typical hijacker might sometimes be unreliable, fake and even unsafe.
Hazardous adverts and web locations can be found all over the Internet and although the hijacker itself is no virus, it could easily expose you to ads that might land you on malware-infested locations where nasty threats the likes of Trojans, Spyware, Rootkits and Ransomware could attack and infect your computer. Because of this, it is always preferable to take the necessary actions and see to the quick and full removal and elimination of any hijacker-related data which might be on your computer. Note that a simple uninstall is unlikely to get rid of everything associated with an app like Luckyguys.top, Luckyguys.xyz, “Pornographic Virus Alert from Microsoft” which is why, once again, we advise you to refer to the instructions from the guide below or to the recommended removal tool.
Luckyguys.top
You surely don’t want any more undesirable software elements to find their way inside your computer. In the case of hijackers, one of the most typical and effective ways of distribution seems to be the so-called file bundling technique. This is when a certain app is added to another piece of software, thus forming a file bundle/installation package.
Normally, one should be able to install only the main program from the package leaving out anything that’s optional (such as an added hijacker). However, in order to do that, one should manually customize the settings in the setup manager and uncheck the optional components that look like something unwanted. Only then would it be safe to continue with the installation of the main program. Remember and use this tip and also make sure that you also use your common sense when browsing the Internet and you should be able to keep your machine safe and clean in the days to come.
SUMMARY:
| Name | Luckyguys.top |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Hijackers reveal themselves by altering the functionality and appearance of your browser and also by triggering irritating page redirects and ads generation. |
| Distribution Method | Most hijackers get distributed through spam letters, deceitful ads and low-quality downloads with the hijacker bundled with them. |
Remove Luckyguys.top Pop up Malware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment