.Mars
.Mars is a file-encrypting ransomware variant that encodes files on its victims’ computers and then asks them to pay a ransom. .Mars does not destroy the encrypted information but keeps it inaccessible until the victims fulfill the ransom demands.
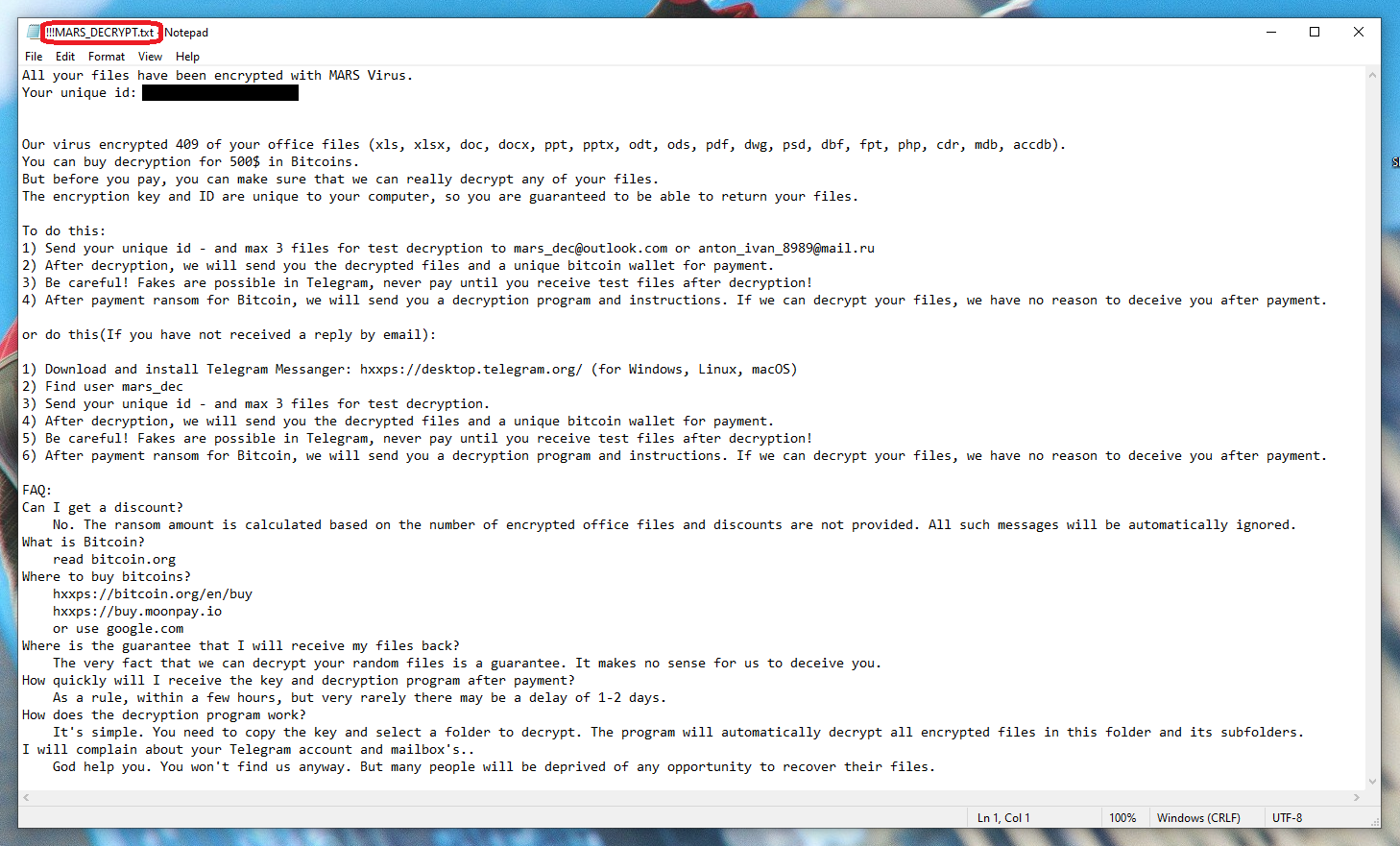
Once the .Mars virus has encrypted your files it will leave a note in a MARS_DECRYPT .txt file.
Every file-encrypting ransomware representative essentially prevents user access to specific files that are found on the compromised computer. .Mars in particular, can make a variety of digital data unusable by applying a special encryption to it that no program or software can read. The hackers behind this infection usually offer their victims to send them a decryption key with the help of which they can reverse the applied encryption. But, obviously, there is a catch. And the first thing the victims will have to do if they want to receive that key is to pay a big sum of money as a ransom. Unfortunately, there is no guarantee that they will get a decryption key from the crooks even if they fulfill all of their demands, which makes ransomware viruses such as .Mars one of the most dangerous piece of malware to deal with. But this doesn’t mean that the only choice you have is to pay the hackers. In the removal guide below you will find some suggestions that may help you recover your files without paying ransom to anyone. First, however, we advise you to carefully remove .Mars to make sure that it does not encrypt any more files on your computer. If you don’t know how to do that, we have described the exact removal steps in the first section of the guide.
The .Mars virus
The .Mars virus is a malicious piece of software that can target the most common types of files such as digital documents, archives, databases, images, videos, audios, etc. Once it detects them, the .Mars virus creates encrypted copies while the originals are removed from the system.
It can often take up to several hours, depending on the computing power and the amount of data stored on the computer, to complete the file-encrypting process. In some cases, this can eventually give the user a chance to stop the virus before it can encrypt all the data on the infected device. Sadly, there usually are no visible symptoms that can give the ransomware away and the only symptom will most likely be a slowdown in the computer’s performance for the time that the file-encrypting process is running in the background. Advanced versions of the ransomware class such as .Mars may also remain under the radar of the antivirus on your computer which makes the timely detection of the malware even harder.
The .Mars file encryption
The .Mars file encryption is very complicated code that is applied to specific files and can only be reversed by using a special decryption key. In certain cases, a solution to the .Mars file encryption can be found online in free decryptor software.
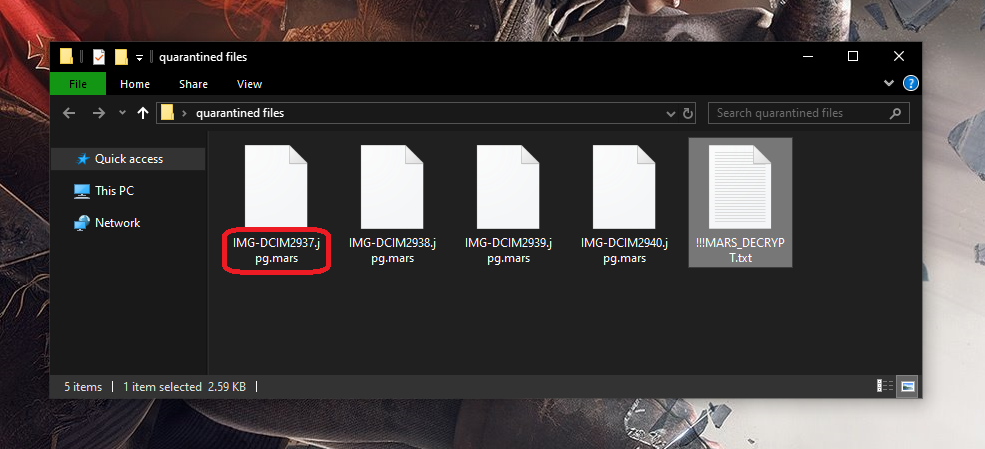
The .mars file
Restoration of the files encrypted by .Mars, Foop and .Mmpa. can also be possible if the victims have personal backup file copies. We have listed a few more options to restore your information in the guide below, but before you give them a try, make sure that you remove the ransomware and all its related files by using the removal instructions.
SUMMARY:
| Name | .Mars |
| Type | Ransomware |
| Detection Tool |
.Mars Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment