*Source of claim SH can remove it.
Masodas
This page aims to help you remove the Masodas Virus Ransomware for free. Our instructions also cover how any .masodas file can be recovered.
If you know anything about Ransomware, then you should be aware of the fact that the representatives of this malware category are among the worst possible software threats you could get in your computer. To be fair, the potential damage that a Ransomware data-encryption virus (such as the newly released Masodas) may cause if it gets in your computer largely depends on what data you keep in your machine and if you have that data backed up.
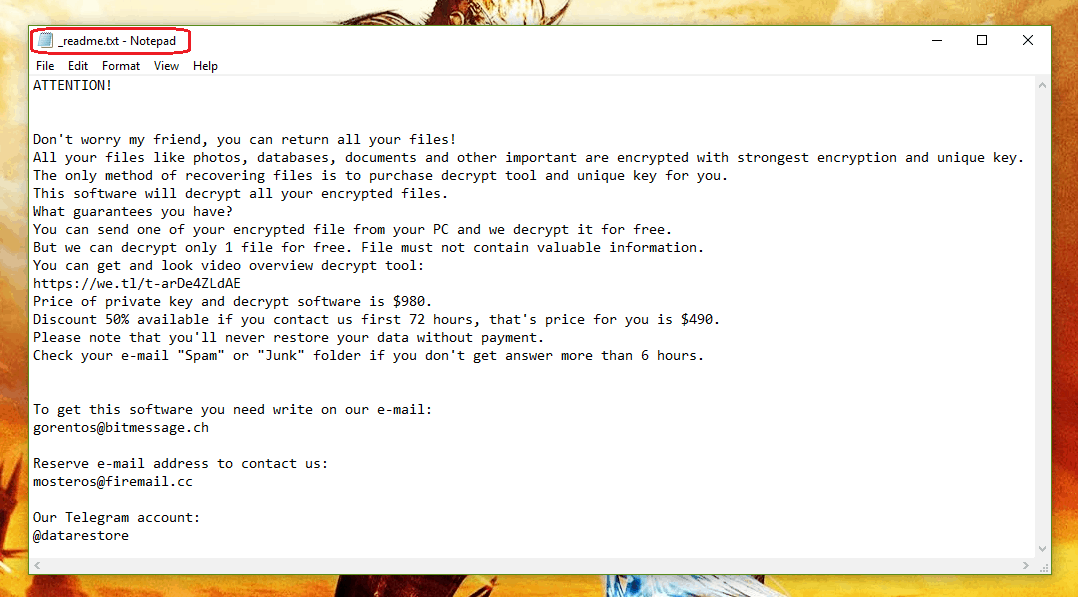
For example, if you don’t store any sensitive, and important files in your machine, or if you have the valuable data in your computer backed up somewhere else, then a Ransomware attack wouldn’t be such a huge issue – all you’d need to do is remove the virus, which is actually not all that difficult. However, statistics show that most users do indeed keep a lot of important files in their systems without having proper backups for those files. This is a problem because the main target of a cryptovirus like Masodas, Nuksus or Verasto are indeed the files kept on the infected computer. However, instead of damaging, stealing, or corrupting them, a typical cryptovirus would simply encrypt the said files. The employed encryption makes it very difficult, if not impossible, for the user to open the files without the corresponding access key that is unique for each infected computer. Of course, the idea is that the victims of Masodas would be blackmailed to pay a ransom for this special key. If they refuse to do so, their files would remain sealed forever.
Facing the .Masodas virus
If you are one of those users with many valuable data in their machines and without a backup for that data, you must know what your options are if a Ransomware like this one has placed its encryption on your files.
First and foremost, we must address the issue of paying the money. While this may sometimes work, and get you your data back, there are two big problems with this approach.
The first one is the fact that not everyone may be able to afford the ransom payment, as the sums demanded by the hackers may get quite high, and also there are oftentimes deadlines, after which the demanded sum doubles.
The second problem is the possibility that the hackers may never really send you anything after you carry out the payment. After all, this isn’t a legitimate online deal – it is a criminal blackmailing money extortion, so you don’t really have a reason to trust those shady anonymous people.
Because of those two things, paying the ransom isn’t really a desirable option.
.Masodas file encryption alternative solutions
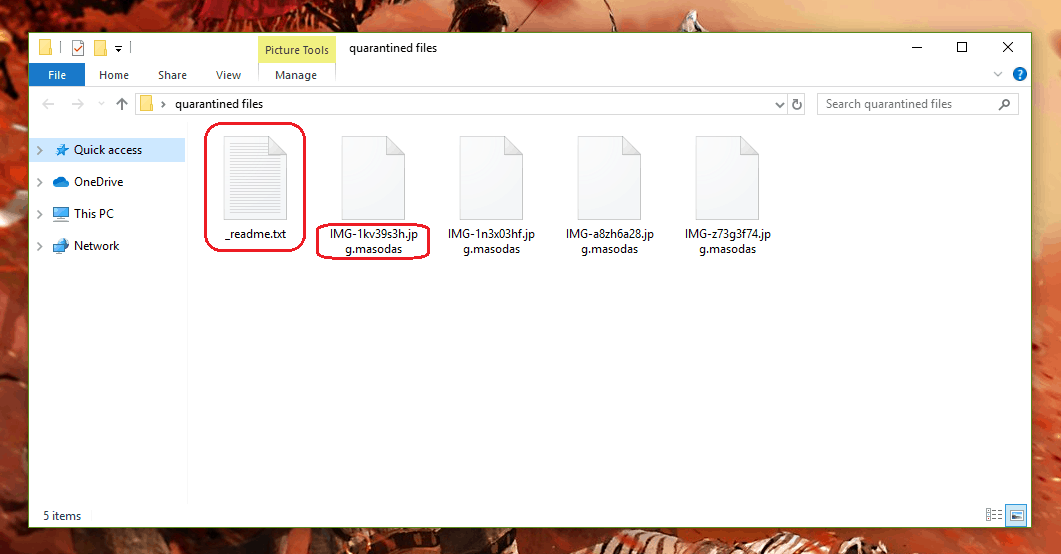
The advisable thing to do in a situation like this is to quickly find a way to remove the virus, which will allow you to try some of the potential alternative data restoration methods. Some such methods you can find in the second section of the removal guide from the current page. However, before you get to that, you should remove the virus, and the guide below will help you do that. Remember that we can’t promise the full recovery of your data, but if you go for the alternatives, you will at least save your money!
SUMMARY:
| Name | Masodas |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Source of claim SH can remove it.
Remove .Masodas Virus Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

My computer was hit by Masodas ransomware and my files are locked by it.
I had format my windows os 10 but still my other partition files are blocked by masodas.
kindly do the needful
Can’t delete the folders
Is the decryption tools over yet?
hi! can I use it with .nesa?