Mkos
Mkos is a harmful piece of Windows malware that is targeted at the victim’s files, as it seeks to make them inaccessible. The purpose of Mkos is to extort money from you by not allowing you to open your files until you pay a ransom.
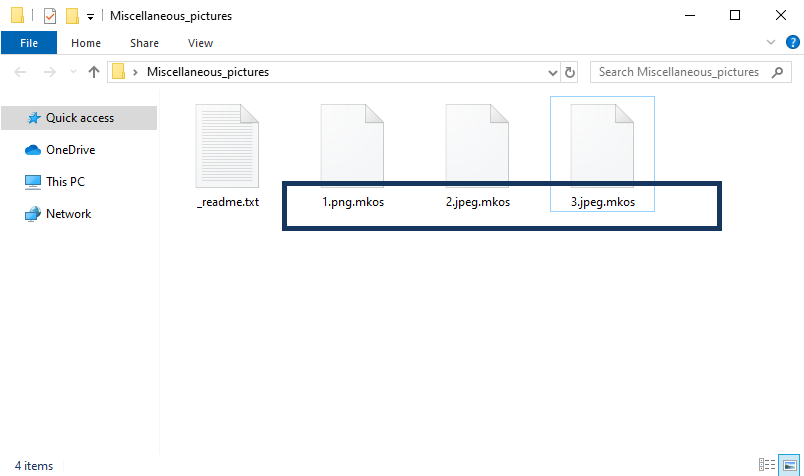
The Mkos Virus will encrypt your files and leave a _readme.txt file behind.
If you have been hit by a virus such as this one, you must be well-acquainted with its specifics in order to know how to counteract it and how to ameliorate the negative consequences of its attack. Mkos is a representative of the so-called Ransomware virus category. Ransomware threats like Mkos are malware tools used for the purposes of money extortion. Mkos, in particular, uses data-encryption to make it impossible for you to open or edit any of your files. The encryption this malware employs is nearly unbreakable and, in most cases, the only thing that can allow you to remove it from your files is a special private key. Of course, this key wouldn’t be available to you once the Ransomware finishes putting its encryption on your files. Initially, only the hackers who’ve created this malware have the key to decrypt your files. They give you the option to pay them for this key, but if you go for this course of action there’s always the risk of getting tricked into sending your money without receiving the means to unlock your data after the payment. Therefore, our suggestion is to explore the alternative file-recovery options that may be available to you.
Mkos is a file-encrypting malware virus that will keep your files locked through its encryption until you obtain the corresponding private key. The Mkos file-encryption is typically unbreakable without the key. Still, there may be alternative ways to release your data from Mkos. In the following article and guide, we will explore those alternatives and we will try to provide you with instructions that will help you remove the infection and potentially even bring some of your locked data back to its normal accessible state.
The Mkos virus
The Mkos virus is a malicious Ransomware program with the ability to put encryption on most of your files and thereby render them inaccessible. Once the Mkos virus finishes encrypting your data, it will show a message on your screen that demands a ransom payment.
As we already established earlier in this post, paying the hackers is probably something you shouldn’t immediately do once you find out that the malware has put your data under its lockdown. In many cases, there may be a deadline of a day or two within which you are supposed to pay the ransom unless you want the demanded sum to double. This is, of course, done in order to intimidate you into paying sooner. However, it is important to not act out of impulse and fear. Instead, what you should do is systematically try every other possible method that may bring at least some of your data back. However, before you do any of that, you must first make sure to clean your computer from the Ransomware infection. Removing the virus itself is quite manageable and while it won’t automatically free your files, it will at least prevent the virus from locking any new data you may create or download. Also, if you want to use any file backups from external devices, you should only attempt to do that once the malware is removed. Otherwise, all data present on the backup is likely to get encrypted by the Ransomware, killing your best data-recovery option. You will find instructions on how to remove the Ransomware down below. If you want, you can save the details from the ransom note should you later decide to still go for the ransom payment in case none of the other methods have worked.
The Mkos file encryption
The Mkos file encryption is the process that allows this Ransomware virus to restrict all access to your most valuable data files. The Mkos file encryption could be unlocked without a key if there is a free decryptor tool available for this specific virus.
Alternatively, there may be ways to bypass the encryption altogether by restoring some of your data from shadow copies hidden deep in your system. In the recovery part of our guide, you will find both instructions on how to try to recover data from shadow copies as well as an extensive list of free file decryptors available for different versions of Ransomware. Hopefully, some of our recovery suggestions will help you bring back at least a portion of your important data in case you don’t have a full data backup at your disposal.
SUMMARY:
| Name | Mkos |
| Type | Ransomware |
| Detection Tool |
Remove Mkos Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment