*Mlap is a variant of Stop/DJVU. Source of claim SH can remove it.
Mlap File
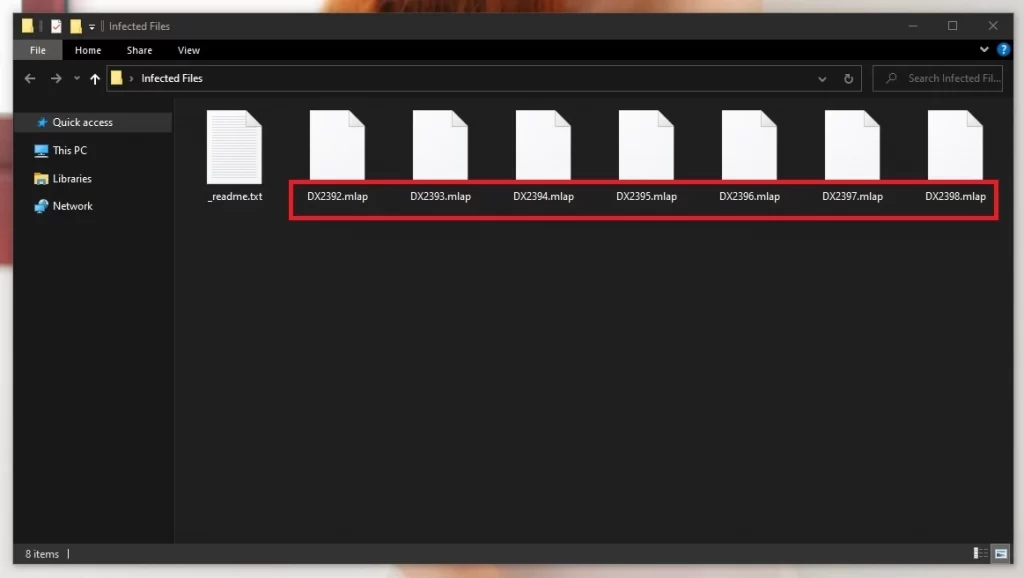
Noticing an Mlap file in your system is a sign of an attack by this malicious ransomware. The ransomware operates by initiating a file encryption process as meticulous as it is malignant. Its primary strategy revolves around identifying and encrypting a vast range of file types, turning each targeted piece of data into a “Mlap file”. This label becomes a beacon of the file’s inaccessible status, a grim reminder of the sophistication of the encryption; a layered process using a robust algorithm virtually impossible to crack. The difficulty in dealing with such files after the ransomware encryption lies in this cryptographic fortress that shields the entrapped data. The task of decoding the encrypted files demands time, expertise, and a formidable computational prowess, often making recovery excruciatingly difficult.
How to decrypt Mlap ransomware files?
There’s no guaranteed way to decrypt Isal ransomware files, but some options are certainly preferable to others. The option that we recommend is to first follow our removal guide to delete the virus, after which you can try out the free file recovery tool linked at the bottom of this page.
How to remove the Mlap ransomware virus and restore the files?
We will show you how to remove the Mlap ransomware in our guide on this page, after which we’ll explain how to use a free data decryption tool to potentially restore the files that the malicious program has managed to render inaccessible.
Mlap Virus
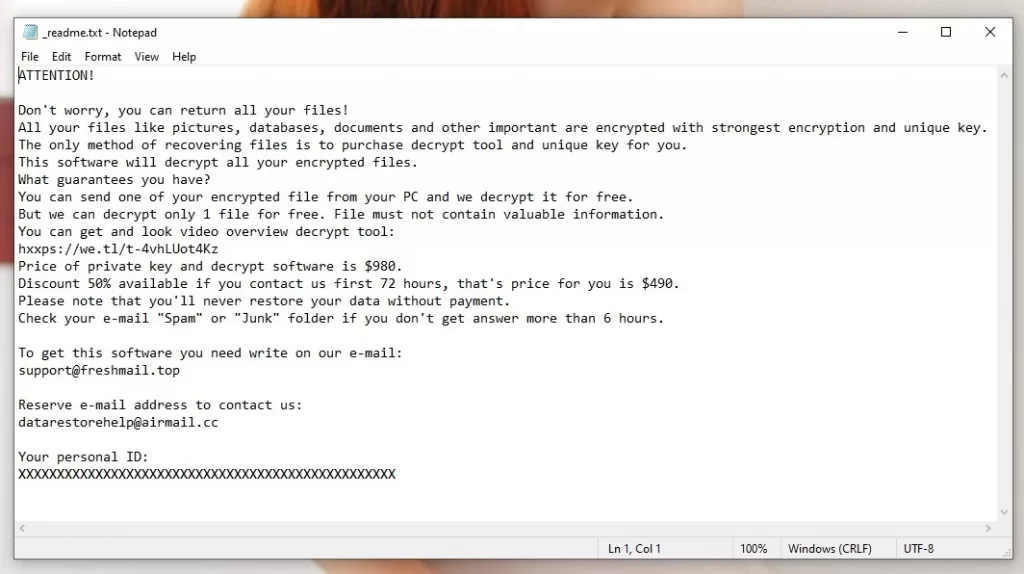
In a digital ecosystem rampant with diverse malware species, the Mlap virus stands apart, commanding a notorious reputation. Unlike many malwares that simply vandalize or pilfer information, ransomware like this one, or other similar ransomware threats like Ttza and Ttrd, hold your files hostage, demanding a ransom for their release. This difference, the ability to forcibly monetize its attack by leveraging the victim’s data, renders it a particularly severe threat. It weaponizes one’s personal or business assets, creating a sense of urgency, a ticking clock that can drive individuals or corporations into a corner, making them more liable to heed to the extortion demands. This distinguishing factor escalates the Mlap virus from being a mere nuisance to a substantial financial hazard, placing it on a different level of cybersecurity threat.
Mlap
The Mlap ransomware employs cunning distribution tactics to infiltrate systems surreptitiously. Frequently leveraging fake emails that are meticulously crafted to appear legitimate, it deceives the recipients into executing the malicious payload. These emails often contain attachments or links harboring the ransomware. Another method involves exploiting unpatched vulnerabilities in software, offering a silent entry point, especially when a backdoor Trojan is used to facilitate the attack. To counter these, one should employ all available prevention strategies such as maintaining a stringent email filtering system and promoting cautious interaction with unsolicited communications. Further, ensuring a routine update of all software to patch potential security loopholes is vital to preventing future Mlap attacks. Last but not least, maintaining a robust backup system can effectively negate the ransomware’s leverage over the victim.
.Mlap
This ransomware exhibits a distinctive marker, appending the .Mlap extension to each encrypted file, a virtual scar declaring them hostage. The advent of this suffix signals the file’s transition into a state of inaccessibility, held at ransom till a payment purportedly promises restoration. However, succumbing to the demand isn’t recommended due to the lack of guarantees surrounding file retrieval. Moreover, it fuels the malicious economy endorsing such cyber-attacks. Recovering files with the .Mlap extension without paying the ransom encompasses exploring potential decryption tools developed by cybersecurity researchers. Often, experts are able to create decryption keys for specific ransomware variants. Additionally, maintaining a regular backup of vital data in separate storage mediums can facilitate the recovery process, offering a pathway to restore the system without yielding to the ransom demand.
Mlap Extension
Let’s delve into the grim signature of this ransomware – the .Mlap extension. While it may seem that files labeled with this extension are irrevocably damaged, there’s a silver lining; they remain intact but locked away in an inaccessible vault of encryption. Resorting to paying the ransom to reclaim access should dwell in the last place in the recovery plan. See, forking over the demanded sum doesn’t guarantee a safe return of your files or removal of the Mlap extension; it’s just playing into the hands of cyber criminals. The recommendation always leans heavily towards exploring every other possible route for file recovery before even considering meeting the ransom demands.
Mlap Ransomware
Now turning our attention to the nitty-gritty of Mlap ransomware, it is pivotal to understand how this menace manages to worm its way into computer systems. Often arriving through spam emails or exploiting vulnerabilities in outdated software, it comes equipped with deceit and disguise. The very moment of its inception marks the time for quick action. One primary damage control measure is swiftly disconnecting external drives and devices to halt the spread. It’s also wise to become a bit of a detective, looking out for signs of the Mlap Ransomware, such as system slowdowns or strange file extensions popping up, a proactive stance that could prevent a full-blown data encryption.
What is Mlap file?
A Mlap file is essentially a digital hostage; a file that has been encrypted to a degree that regular software just can’t decipher it, leaving it unreachable and isolated in its own data environment. The sophistication behind this encryption is what makes recovery a tall order; the “Mlap file” encryption utilizes advanced algorithms that create a fortress around the piece of data, a fortress that standard programs cannot breach. Thus, while the files exist, they remain out of grasp, held captive by a barrier of intricate codes, demanding a ransom for a key that might not even work. For this reason, we recommend the alternative approach of first completing our removal guide and then moving on to the suggested free decryption tool.
SUMMARY:
| Name | Mlap |
| Type | Ransomware |
| Detection Tool |
*Mlap is a variant of Stop/DJVU. Source of claim SH can remove it.
Mlap Ransomware Removal

The next instructions will require you to restart your computer. Therefore, if you don’t want to lose this Mlap removal guide, we recommend that you Bookmark the page in your browser, so you can quickly reload it as soon as the computer restarts.
Next, for the successful removal of all ransomware-related traces, we advise you to reboot the infected computer in Safe Mode and then get back to this page to complete the rest of the instructions.
Once you enter Safe Mode successfully and the computer restarts, click the Start menu button, type msconfig in the search field and hit enter. Then select Startup from the tabs at the top:

If you detect that Mlap has added malicious Startup Items in the list, make sure that you Uncheck their checkmark in order to disable them and then click the Ok button.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Mlap is a variant of Stop/DJVU. Source of claim SH can remove it.
Next, open the Task Manager (CTRL + SHIFT + ESC) and click on the Processes Tab to check for any active malicious processes that are possibly running in the background:

If a given process looks questionable, right click on it to open its File Location folder. After that, use the free online virus scanner below to scan the stored files for malware:

A single file that is detected as dangerous during the scan is enough to indicate that there is something malicious with the process that is running. Therefore, your next action should be to end the related processes and delete the folder that contains malicious files.

Back to the Start menu button, click it and copy the next line in the search box:
notepad %windir%/system32/Drivers/etc/hosts
Open the Hosts file that appears on the results and scroll the text until you find Localhost. Then, if the ransomware has added some malicious IP addresses in the file. If something disturbing grabs your attention, please write us in the comments. The image below describes what you should be looking for:


*Mlap is a variant of Stop/DJVU. Source of claim SH can remove it.
The hardest part of the removal of Mlap is to correctly detect and remove the malicious entries that the ransomware might have added in the Registry. This task may be complicated for inexperienced users, therefore, if you are not confident enough, please do not delete or change anything in the Registry but rather use a professional removal tool (such as the one recommended on this page) to clean the system from malicious files.
If, anyways, you have decided to use the manual method, type Regedit in the windows search field and press Enter to start the Registry Editor.
Next, once in it, open a Find box by pressing CTRL and F together and type the name of the ransomware. Then, search the Registry for entries matching that name and if anything gets detected, then it most likely needs to be removed as it could be linked to the infection. It is also a good idea to check a few more system locations where malicious files may hide. For this, type each of the lines listed below in the Windows Search Field and check them for entries that have been added around the time the ransomware infection occurred:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Make sure you delete the content of the Temp folder and check the other folders for randomly named sub-folders or files that look suspicious.

How to Decrypt Mlap files
In the event of an infection, your initial step is determining the precise ransomware variant you’ve been hit with and understanding the requisite removal procedures before you can commence recovering your files. Identifying the variant could potentially be assisted by observing the extensions attached to your encrypted files.
Yet, before delving into recovery, it’s imperative to confirm the complete eradication of the ransomware from your system. To safeguard against further damages, we advocate adhering strictly to the aforementioned removal guidelines and initiating a comprehensive system analysis using a dedicated antivirus solution or a web-based virus scanner.
New Djvu Ransomware
The STOP Djvu emerges as the latest iteration in the Djvu Ransomware lineage, establishing itself as a formidable threat globally. The distinctive .Mlap suffix tagged to files encrypted under this variant facilitates distinguishing it from its predecessors.
Albeit challenging to counter newer ransomware versions, there exists a glimmer of hope for decoding data compromised by STOP Djvu, provided the encryption leveraged an offline key. Furthermore, there is available decryption utility to aid in your data retrieval endeavors. Access and procure the tool via the following link, navigating to and selecting the download option:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Ensure to operate the downloaded decryptor with administrative privileges, affirming your action in the subsequent confirmation prompt. Prior to proceeding, acquaint yourself with the terms outlined in the license agreement and the concise instructional guide displayed. To initiate the decryption, select the Decrypt button. However, bear in mind the tool’s potential limitations in handling data affected by unidentified offline keys or online encryptions.

Leave a Comment